Attack detection method aiming at inorganization hostile attack
A malicious attack and attack detection technology, applied in the field of learning, can solve the problems of poor recommendation method and inability to detect malicious attackers, and achieve the effect of effective detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] Below in conjunction with specific embodiment, further illustrate the present invention, should be understood that these embodiments are only used to illustrate the present invention and are not intended to limit the scope of the present invention, after having read the present invention, those skilled in the art will understand various equivalent forms of the present invention All modifications fall within the scope defined by the appended claims of the present application.
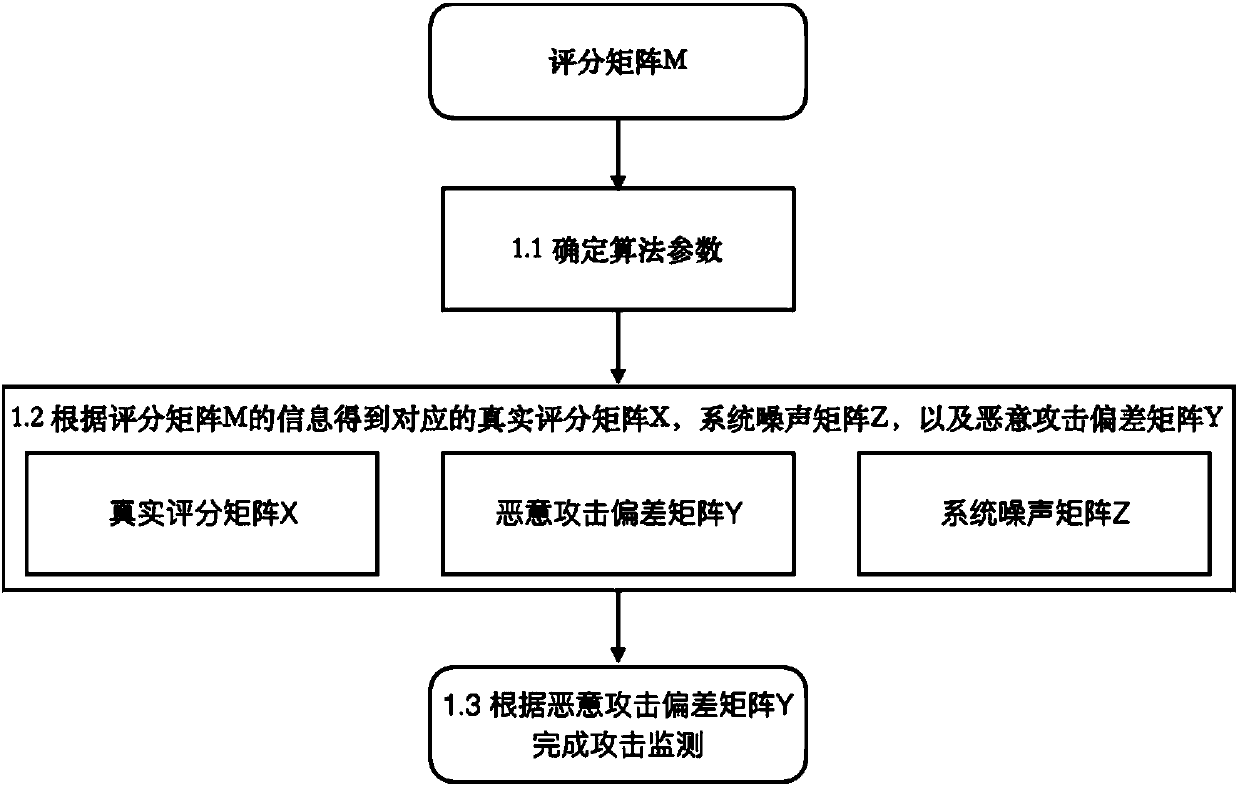
[0025] Such as figure 1 As shown in the attack detection method for disorganized attacks, the specific steps are as follows:
[0026] Step 1.1, convert all the ratings given by users to items into an incomplete rating matrix M, and determine the parameters of the algorithm according to the number of users, number of items, number of ratings and range of ratings in the rating matrix M.
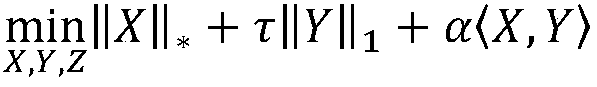
[0027] The parameters of the algorithm are determined according to the information of the scoring matrix M, spe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More