Android mobile attack traceability method
An API calling and sensitive technology, applied in the computer field, can solve problems such as false negatives, inability to meet the traceability of mobile attacks, and difficulty in completely covering the program code in the execution path, so as to achieve the effect of improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
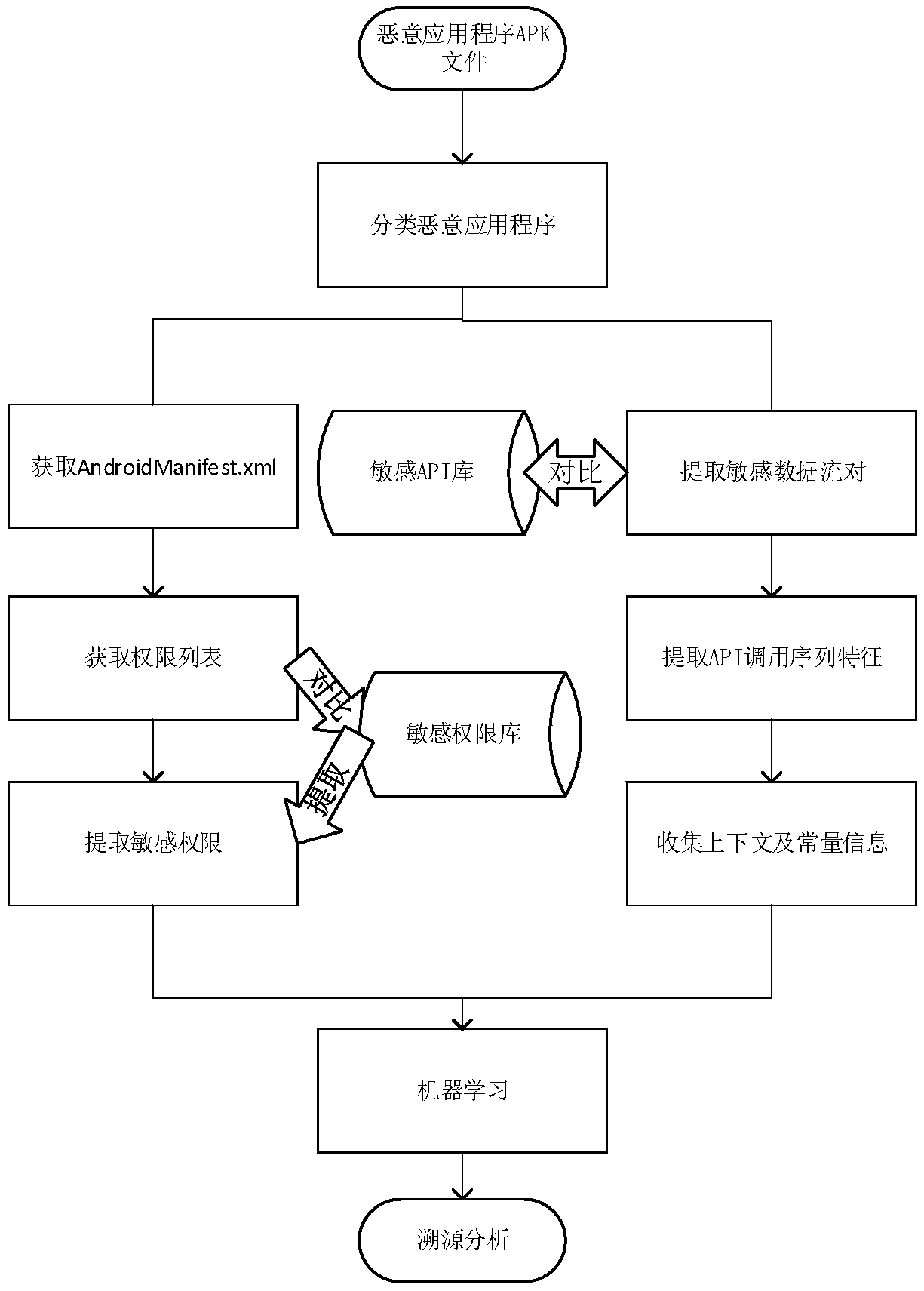
[0018] The embodiment of the present invention provides a method for tracing the source of an Android mobile attack. The method reads the list of rights items applied for by the malicious application program from the AndroidManifest.xml file of the malicious application program, and determines the sensitive authority by matching with the sensitive authority database; The data flow analysis tool extracts sensitive data flow pairs of malicious applica...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More