[0011] 1) For example, a
consumer scans a QR code in a supermarket to pay for food with a
mobile phone, but the store’s QR code is planted with a
Trojan horse by criminals due to poor management. The
payment account number and
password are stolen, so criminals can use the stolen
payment account number and
password of consumers to consume. Such crimes are difficult to be discovered in advance, and consumers have already suffered a lot by the time they are discovered. economic loss
[0012] 2) Another example, at the 3.15 conference in 2019, the
bank admitted that its mobile terminal-based flash
payment has security risks. In this regard, UnionPay announced that as long as the report is made within 72 hours, the loss can be fully compensated
[0013] 3) For another example, there are a large number of illegal POS machines in the market now, swiping cards on these illegal POS machines will bring major security risks to cardholders
[0030] 3. Spending money to illegally purchase
fingerprint or face template data from relevant personnel in companies that provide
fingerprint or face recognition services like the current buying and selling of personal information;
[0031] 4. Illegal use of stolen template data;
[0032] 5. Use stolen template data to illegally track from one
system to another;
[0050] 4) The former is a passive defense that cannot actively discover online hackers hiding in the
virtual world, because traditional cryptography only studies the digital signature itself and does not study the people behind the digital signature
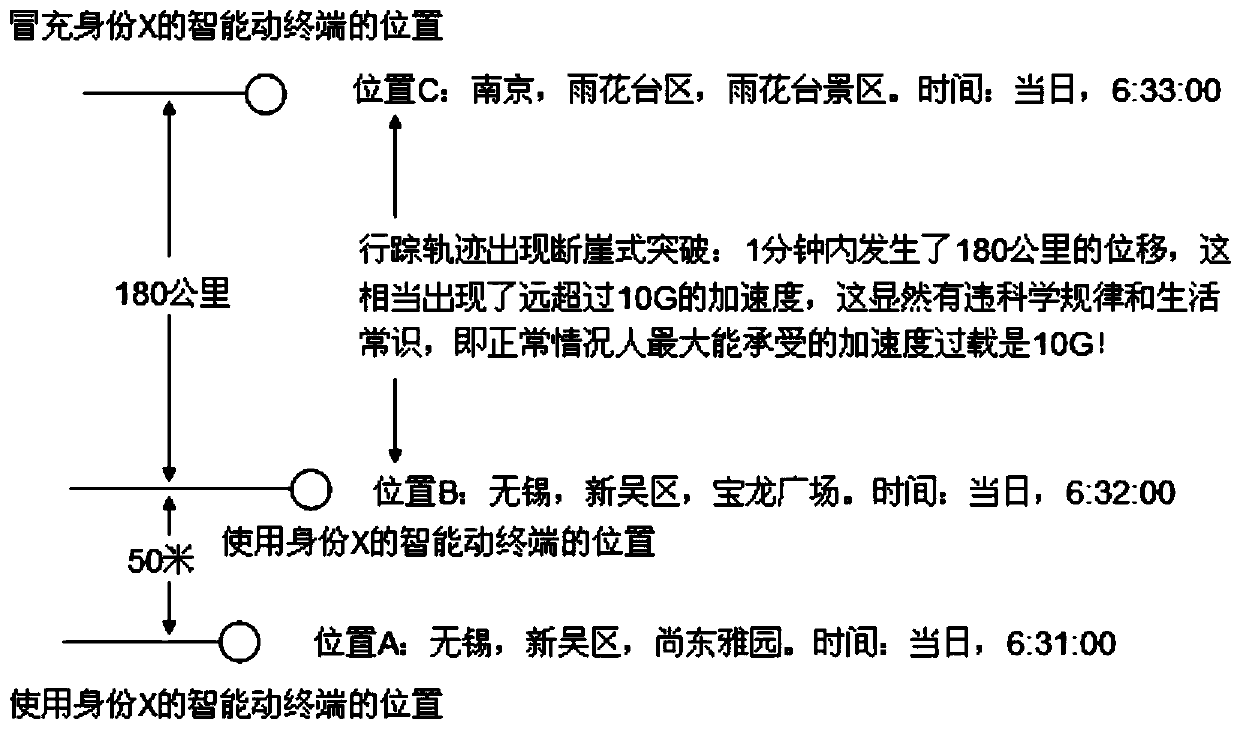
[0058] For example, although
satellite positioning is a public and open service, and the obtained
satellite positioning latitude and
longitude are real, network hackers can abandon it and develop an application APP that can completely simulate the user's current use, and artificially input a
satellite positioning by themselves.
Longitude and
latitude, but the problem is: a major feature of cyber hackers is that they don’t know where the victim’s precise location is now—so they can’t input the victim’s correct satellite positioning location! !
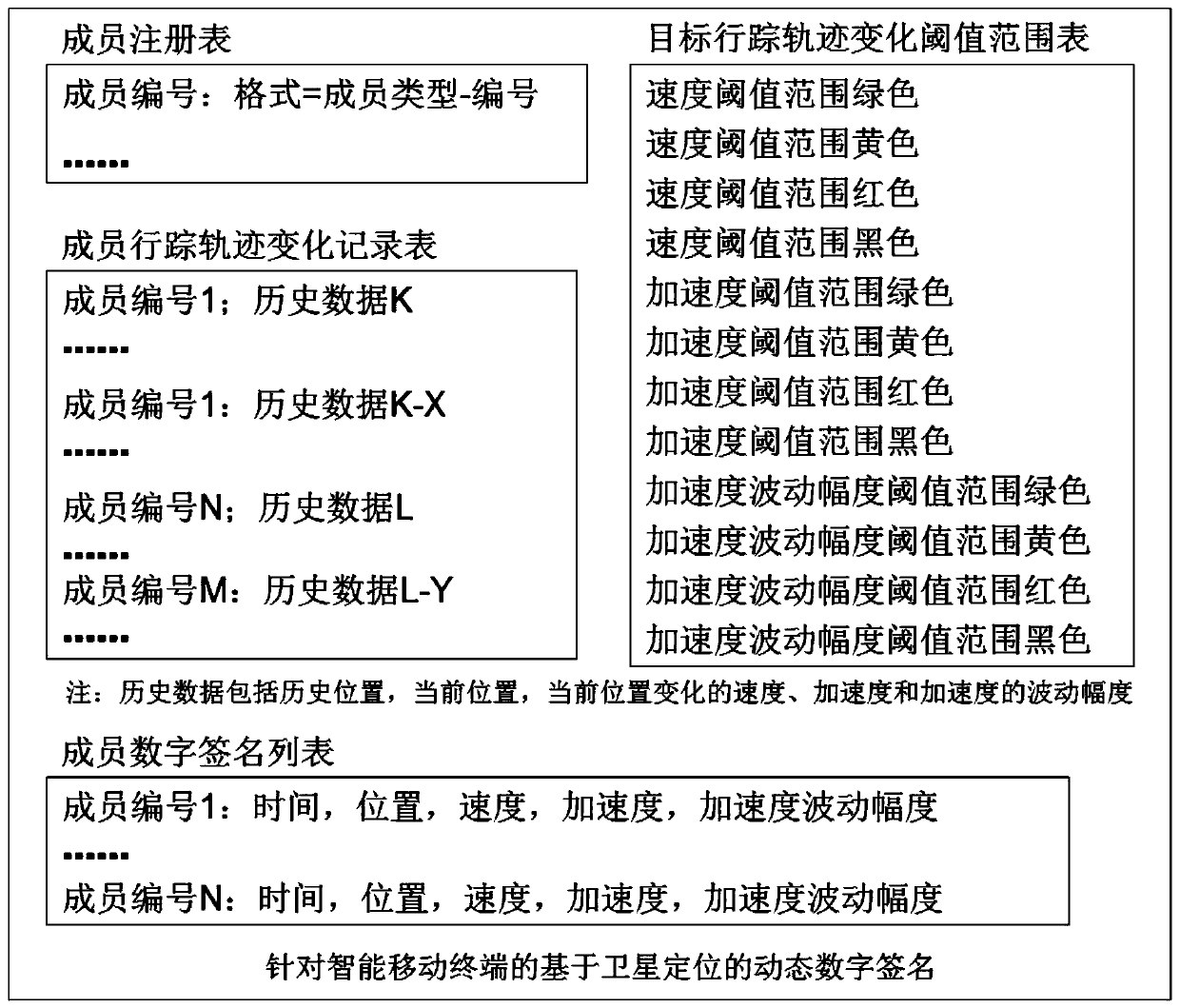
[0062] 1) Recording an individual's whereabouts involves personal privacy issues;
[0063] 2) If the certification service is limited to this industry, this field, this application, and this enterprise, then there will inevitably be thousands of redundant constructions carrying out the same certification business, resulting in a huge waste of social resources;
[0064] 3) If
authentication is turned into a third-party service, then the organization that provides this third-party
authentication service must face the need to store the whereabouts of hundreds of millions of authenticated users every day, including more than 1 billion
authentication operations per day. Computing power and
network service capabilities are a very heavy
cost burden [0067] It should be pointed out that when cryptography came out, there was no
mobile Internet, let alone satellite positioning, so how to solve the security problem on smart mobile terminals, if we ignore the characteristics of mobile terminals themselves, including ignoring the seemingly irrelevant frontier Science, but just blindly thinking about how to strengthen the
encryption code or the strength of
encryption, so that criminals cannot crack it within an
effective time, then they may fall into an endless loop of "the road goes up one foot and the devil goes up one foot", because Once
quantum computers appear, all existing traditional
encryption methods will be vulnerable! On the other hand, user passwords representing personal identities will never disappear, and
Trojan horse viruses in smart mobile terminals will never disappear, so what should we do? !
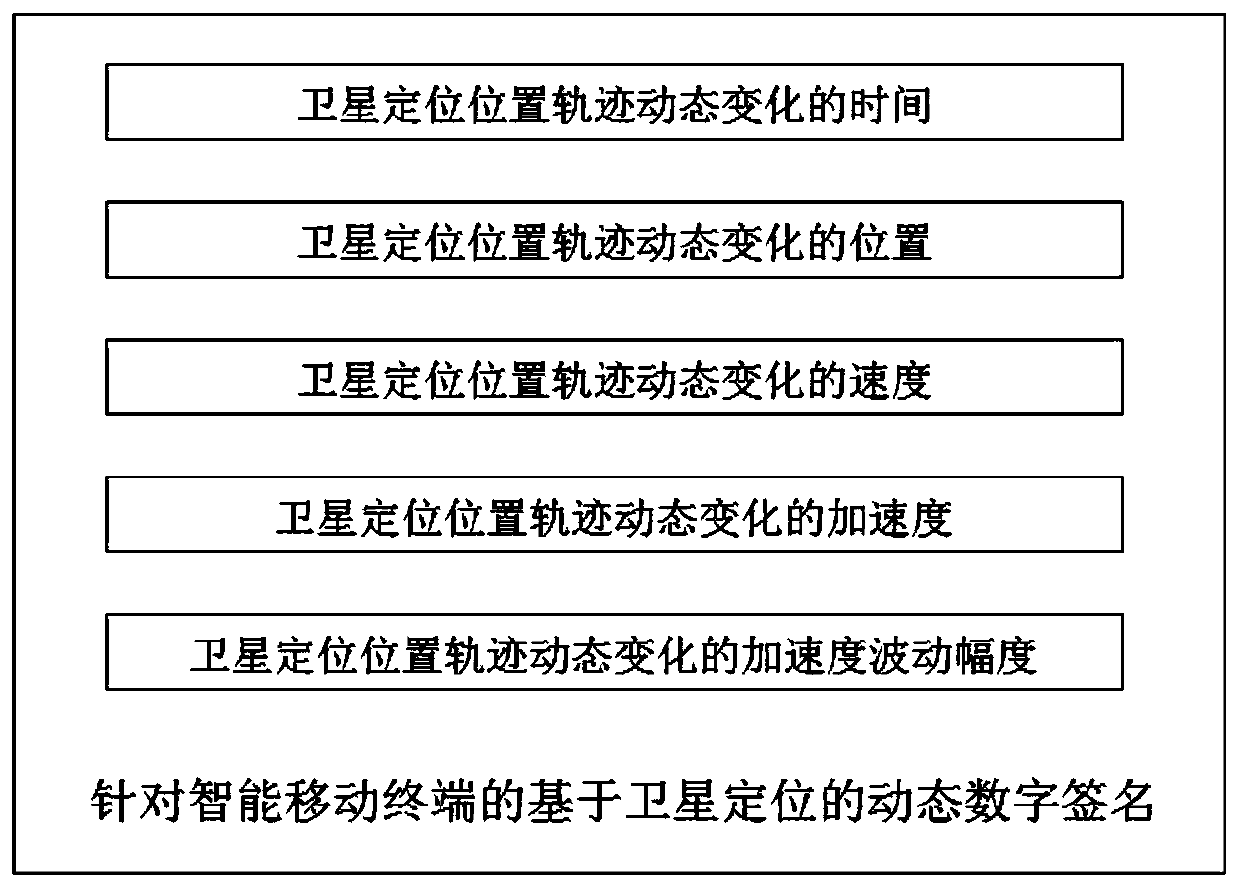
[0068] To sum up: In order to realize the above assumptions and solve the problem that traditional cryptography only recognizes passwords but not people, we invented the "Dynamic
Digital Signature Method Based on
Satellite Positioning for Smart Mobile Terminals"
 Login to View More
Login to View More  Login to View More
Login to View More