Method and apparatus for orchestrating files based on containers
A container and file technology, applied in the Internet field, can solve problems such as insufficient security, data security problems, data theft and tampering, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
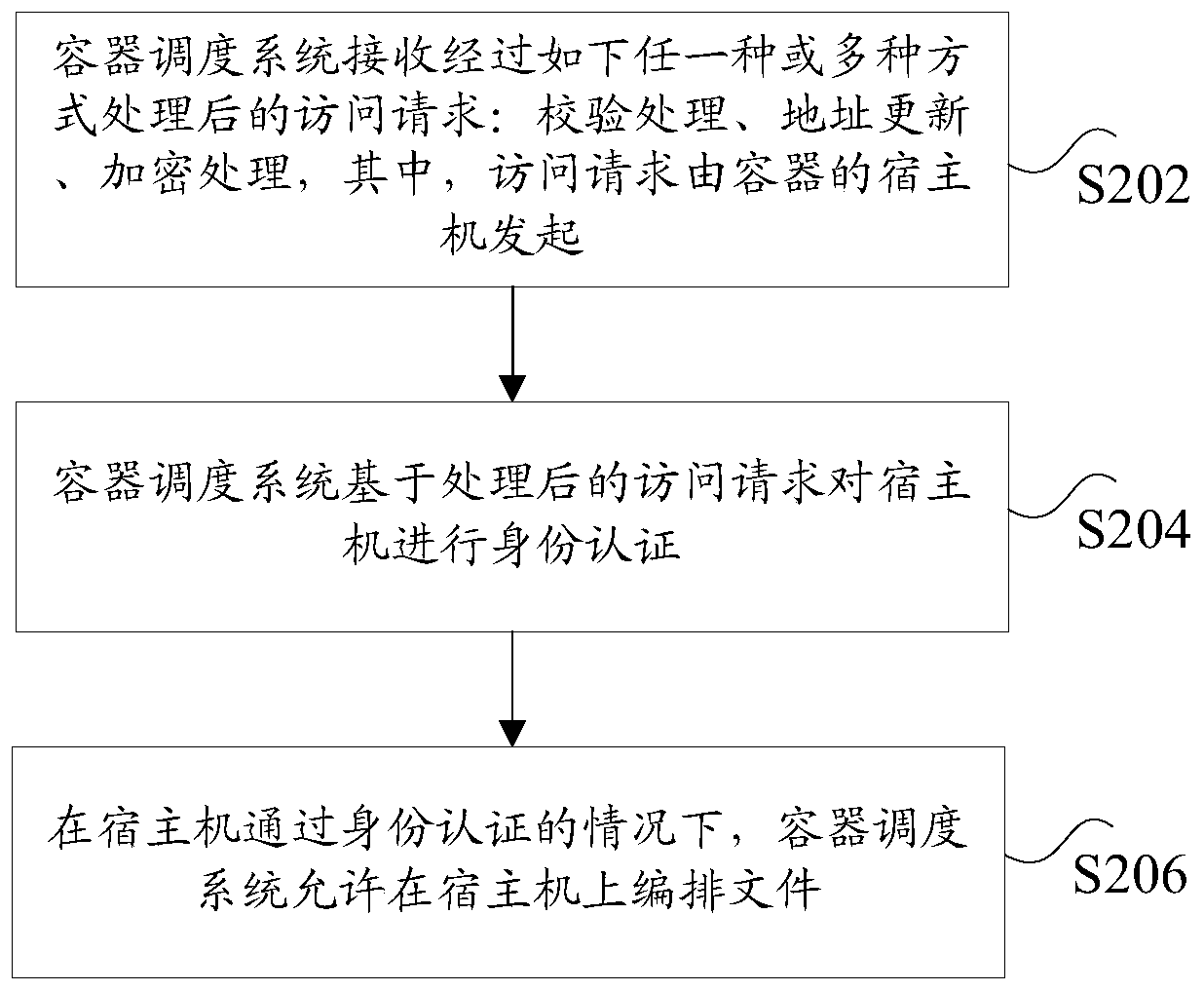
[0033] According to an embodiment of the present invention, an embodiment of a method for arranging files based on a container is also provided. It should be noted that the steps shown in the flowcharts of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions , and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
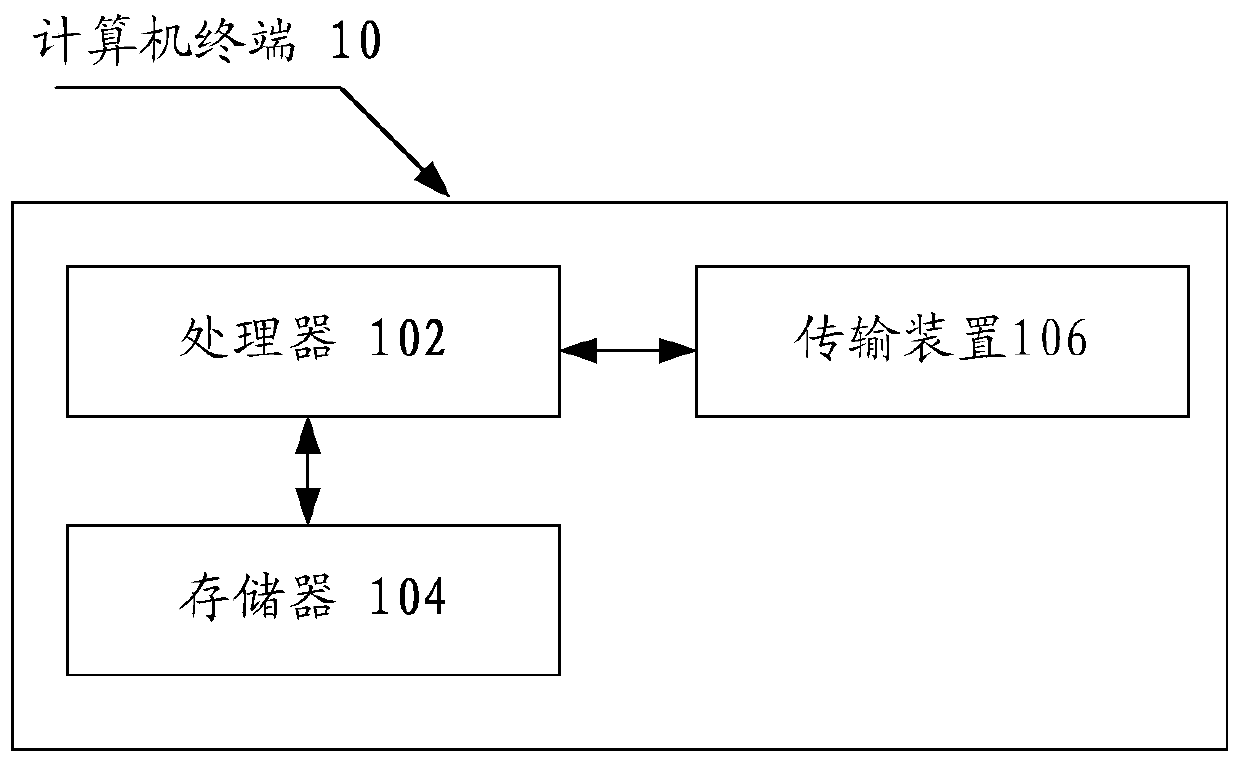
[0034] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. Take running on a computer terminal as an example, figure 1 It is a block diagram of hardware structure of a computer terminal according to a container-based method for arranging files in an embodiment of the present invention. like figure 1 As shown, the computer terminal 10 may include one or more (only one is show...
Embodiment 2
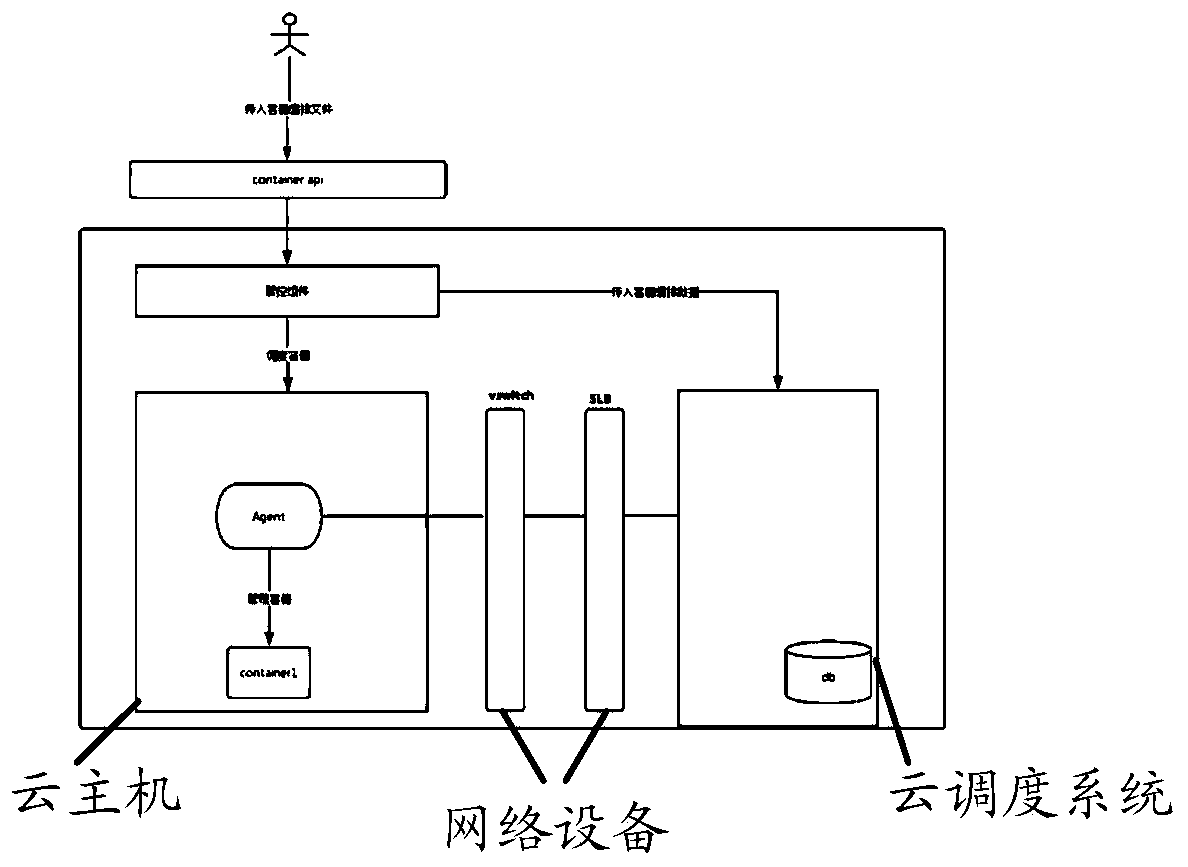
[0059] According to an embodiment of the present invention, there is also provided a device for implementing the above container-based method for arranging files, such as Figure 4 as shown, Figure 4 is a schematic structural diagram of a device for arranging files based on a container according to Embodiment 2 of the present invention, and the device includes:
[0060] The receiving module 42 is configured to receive an access request processed by any one or more of the following methods: verification processing, address update, and encryption processing, wherein the access request is initiated by the host of the container; the authentication module 44 is configured to The processed access request performs identity authentication on the host machine; the arrangement module 46 is configured to allow the arrangement of files on the host machine when the host machine passes the identity authentication.
[0061] Optionally, the device further includes: a sending module, configu...
Embodiment 3
[0065] According to still another aspect of the embodiments of the present invention, there is also provided a storage medium, the storage medium includes a stored program, wherein, when the program is running, the device where the storage medium is located is controlled to execute the container-based method for arranging files in the first embodiment above .
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More