A Modeling and Analysis Method for Network System Security Vulnerabilities Correlation
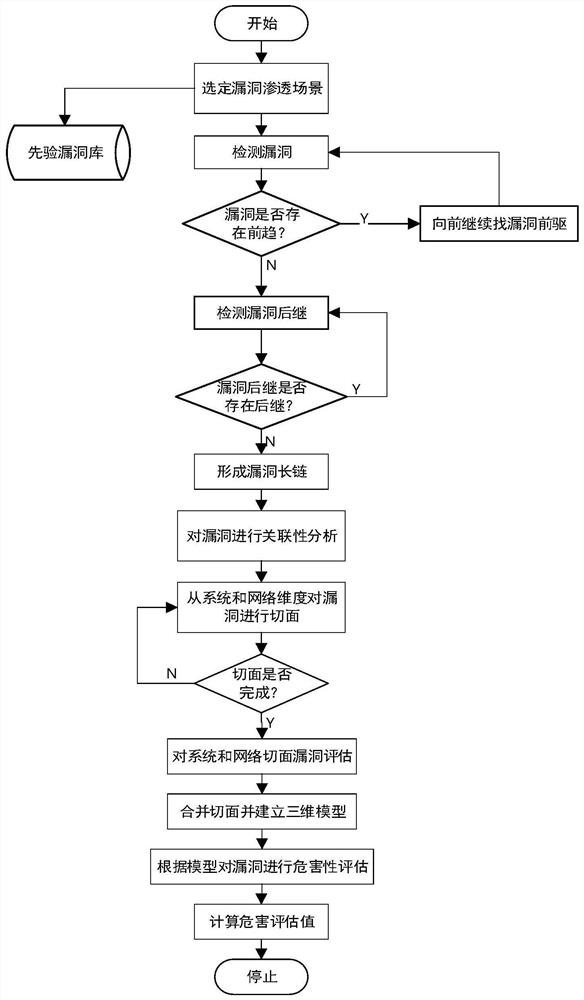
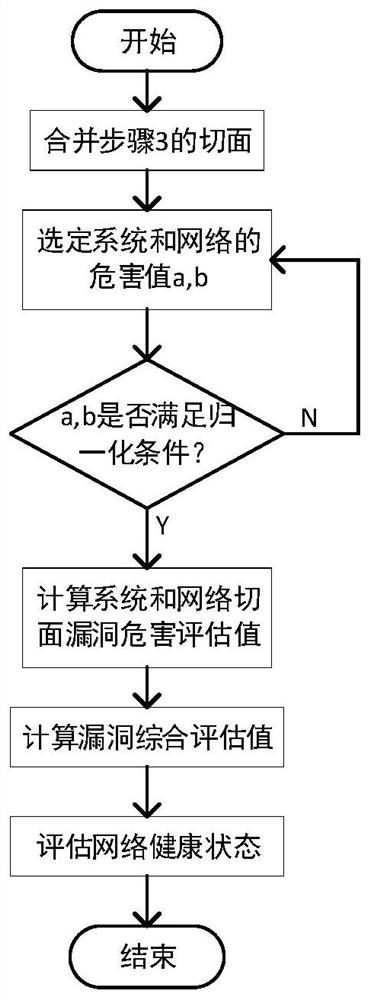
A network system and analysis method technology, which is applied in the field of network system security vulnerability correlation modeling and analysis, can solve the problem of inaccurate network harm degree measurement standards, and achieve the effect of thorough vulnerability analysis, high accuracy, and comprehensive evaluation perspective
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0061] In the network system, the leakage of some user information will activate the system loopholes and then infiltrate them. Some infiltration results can even be used again. Step by step, they can penetrate deep into the system to obtain higher rights. In order to cover up the infiltration behavior, the infiltrator The infiltration traces are erased. In order to facilitate the next attack, the infiltrator will leave a back door.
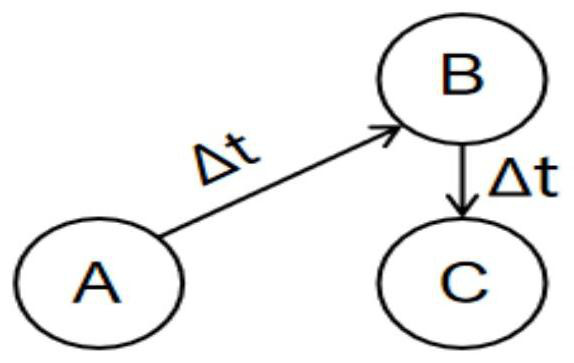
[0062] Note that A is the vulnerability caused by the system version being too low. The attacker uses this vulnerability to cause an overflow vulnerability B in the system. Through the overflow, the infiltrator can obtain the system shell, and then use the shell to trigger the privilege escalation vulnerability C. The infiltrator logs in through ordinary users. System, escalate privileges, obtain administrator information, log in to the background, make changes to the database or other information of the website, and finally the attacker successfu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More