Computer data protection system based on identity authentication
An identity authentication and protection system technology, applied in the field of computer data protection system based on identity authentication, can solve the problems of data leakage, single access verification method, etc., achieve good data security, solve data leakage, and improve the effect of security protection strength
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The embodiments of the present invention are described in detail below. This embodiment is implemented on the premise of the technical solution of the present invention, and detailed implementation methods and specific operating procedures are provided, but the protection scope of the present invention is not limited to the following implementation example.
[0041] The embodiment of the present application solves the technical problem of poor data protection effect in the prior art by providing a computer data protection system based on identity authentication, and achieves the technical effect of improving data security protection effect and ensuring data security.
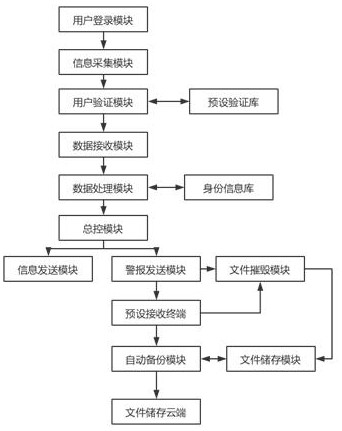
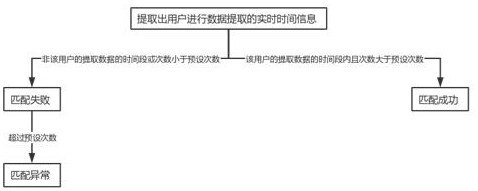
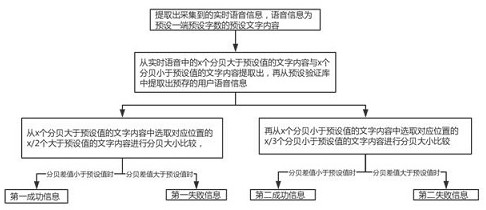
[0042] Such as Figure 1~3 As shown, this embodiment provides a technical solution: a computer data protection system based on identity authentication, including a user login module, an information collection module, a user verification module, a preset verification library, a data receiving module, a dat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More