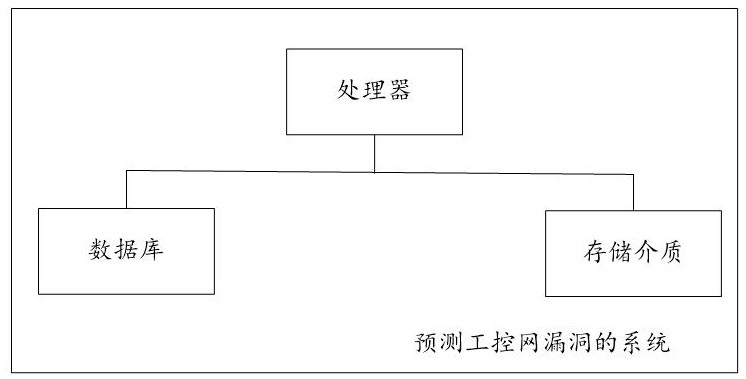
System for predicting industrial control network vulnerabilities based on Summary word segmentation features
A loophole and industrial control technology, applied in the computer field, can solve problems such as the inability to guarantee the security of the industrial control network, and achieve the effects of improving accuracy and prediction efficiency, widely using value, and improving accuracy and training efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
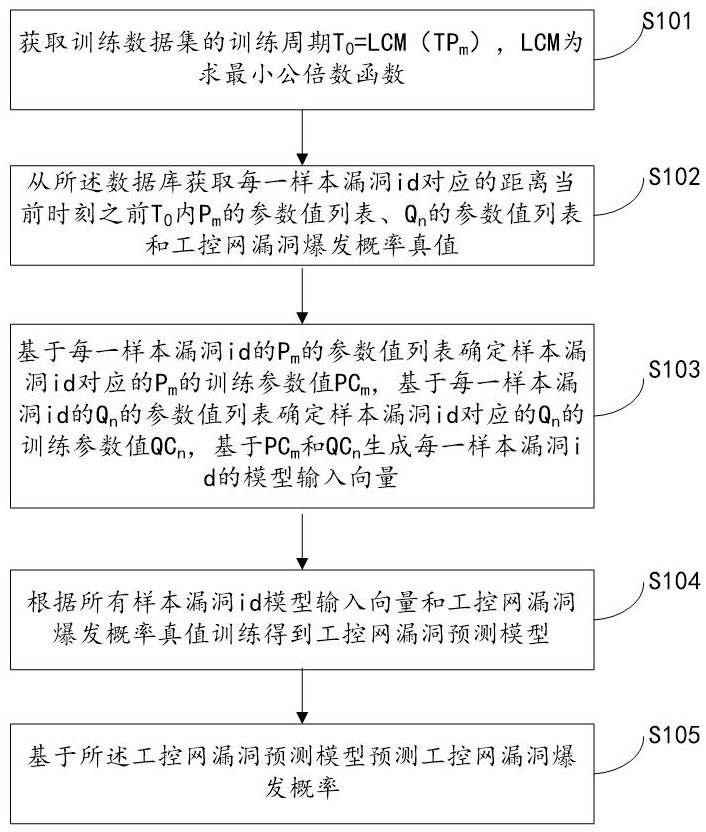
[0036] The computer program stored in the storage medium includes a first computer program, and when the processor executes the first computer program, the following steps are implemented:
[0037] Step S101, obtain the training period T of the training data set 0 =LCM(TP m ), LCM is the least common multiple function.
[0038] Due to different P m and Q n The update period of t is very different. If the sliding window is directly used to select the training parameters, many parameters will not change within a certain period of time, which wastes computing resources and has little significance for model training. Therefore, this embodiment selects TP m The small common multiple of is used as the training period. It should be noted that since the update period of the characteristic parameters of Internet vulnerabilities is much longer than that of the characteristic parameters of industrial control network, only the update period of characteristic parameters of Internet vul...
Embodiment 2
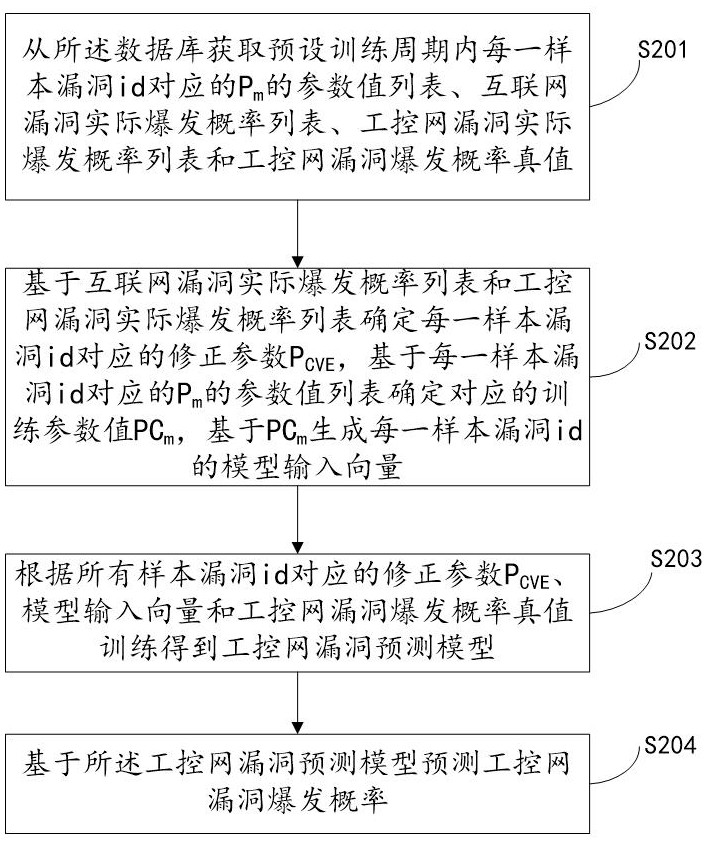
[0064] It should be noted that there are many characteristic parameters of Internet vulnerabilities and are easy to obtain. However, in some application scenarios, due to various factors such as the scale of the industrial control network, it may not be possible to obtain sufficient characteristic parameters of the vulnerability of the industrial control network to train the industrial control network. Vulnerability Prediction Model. However, since the trend of the outbreak of the same vulnerability in the industrial control network is consistent with the overall trend of the Internet outbreak, there is correlation. Therefore, the outbreak probability of the industrial control network vulnerability can be calculated based on the correlation between the industrial control network and the Internet vulnerability outbreak and the characteristic parameters of the Internet vulnerability. predict.
[0065] Specifically, the computer program stored in the storage medium includes a sec...
Embodiment 3
[0094] The computer program stored in the storage medium includes a third computer program, and when the processor executes the third computer program, the following steps are implemented:
[0095] Step S300, obtain the text sequence {Str of each sample vulnerability id in the corresponding Summary from the database 1 ,Str 2 ,...},Str e It is the summary text corresponding to the e-th update period, and the value range of e is from 1 to infinity.
[0096] Step S301, when e=1, according to Str e The length of Str e The feature weight w e .
[0097] Through step S301, for each Str e Set the corresponding initial feature weights.
[0098] Step S302, when e>1, compare Str e-1 and Str e If the text information of is completely consistent, then judge z*w e-1 Whether it is greater than the preset first feature weight threshold w emin , if greater than, then set w e =z*w e-1 , where z is the preset weight adjustment coefficient, 0e-1 less than or equal to w emin , then s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More