Network fragility analyzing system based on privilege lift
A technology for privilege escalation and system analysis, which is applied in the system field of network security technology to achieve the effect of low time complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] The embodiments of the present invention will be described in detail below. This embodiment is carried out on the premise of the technical solution of the present invention, and the detailed implementation and specific operation process are given, but the protection scope of the present invention is not limited to the following embodiments.
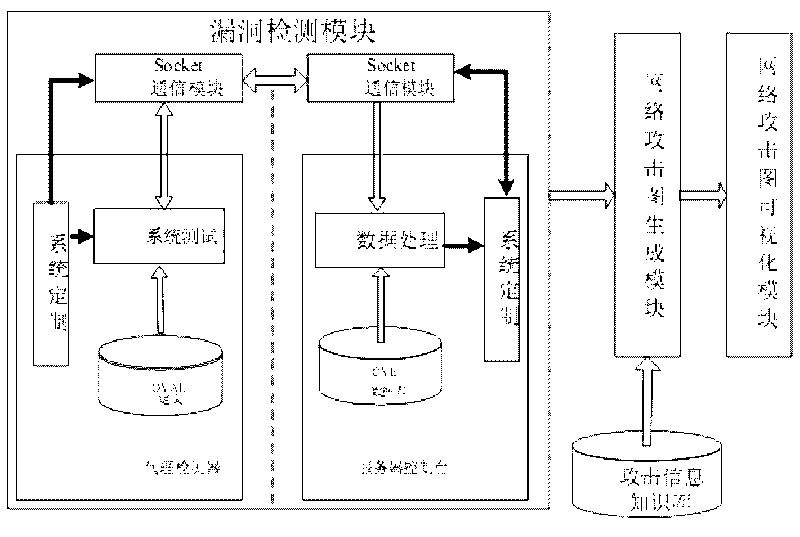
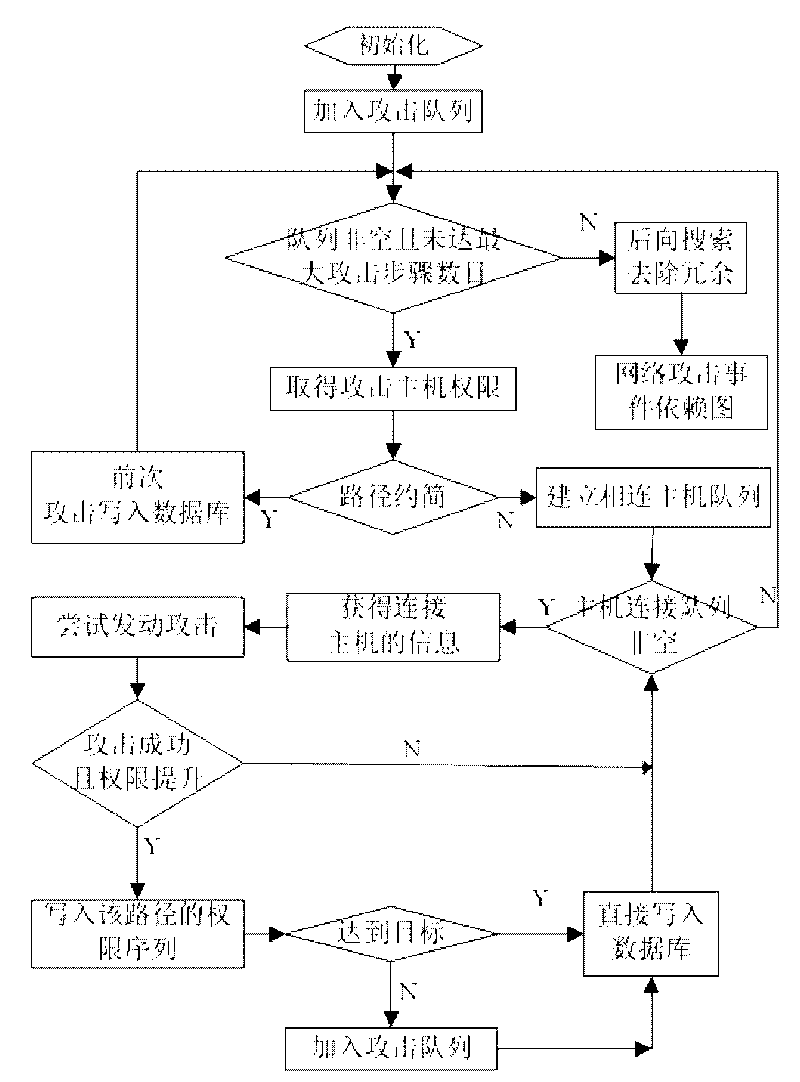
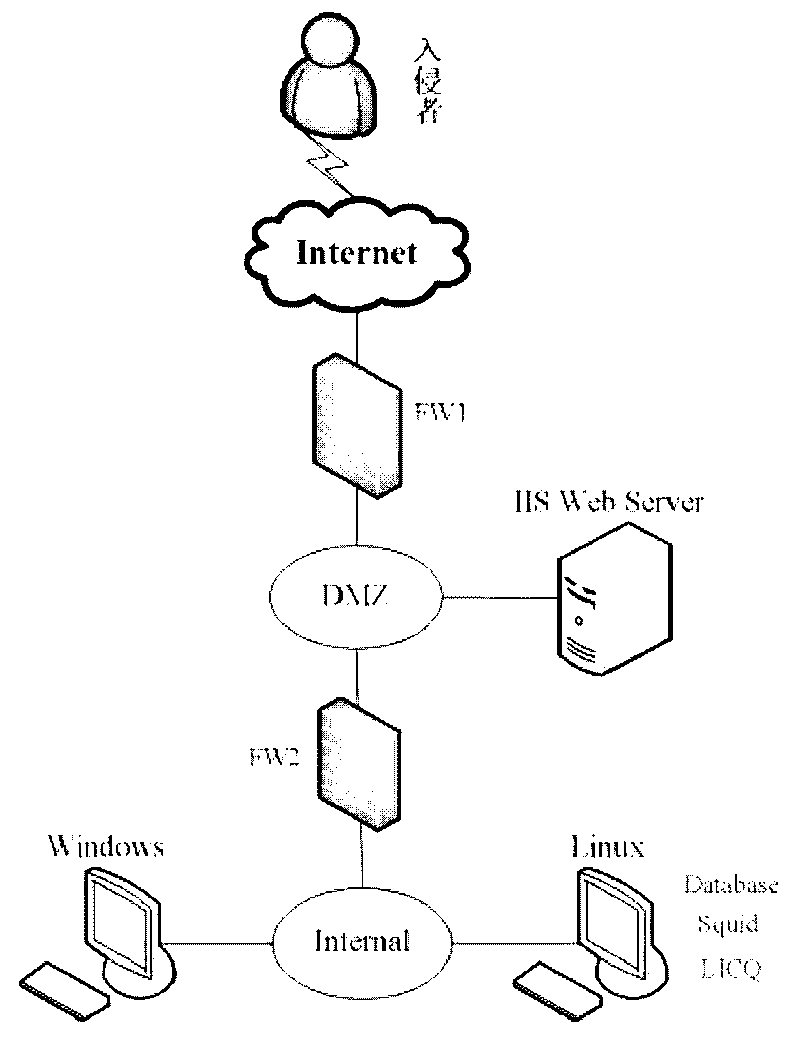
[0028] Such as figure 1 As shown, this embodiment includes: a vulnerability detection module, an attack information knowledge base, a network attack graph generation module and an attack graph visualization module, wherein: the vulnerability detection module is connected with the network attack graph generation module and transmits vulnerability information, network connectivity information and host Information, the attack information knowledge base is connected with the network attack graph generation module and transmits vulnerability exploit information, the network attack graph generation module is connected with the attack gr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More