Random validation method for making random constraints be selectively driven by coverage rate
A random verification and coverage technology, applied in the field of random verification, can solve problems such as reducing engineers, and achieve the effect of reducing time consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
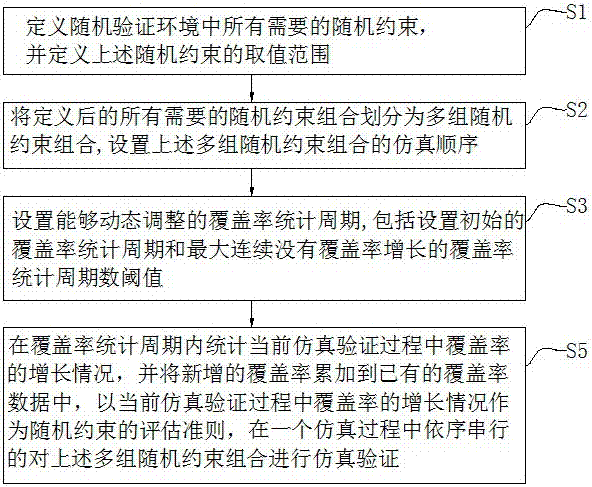
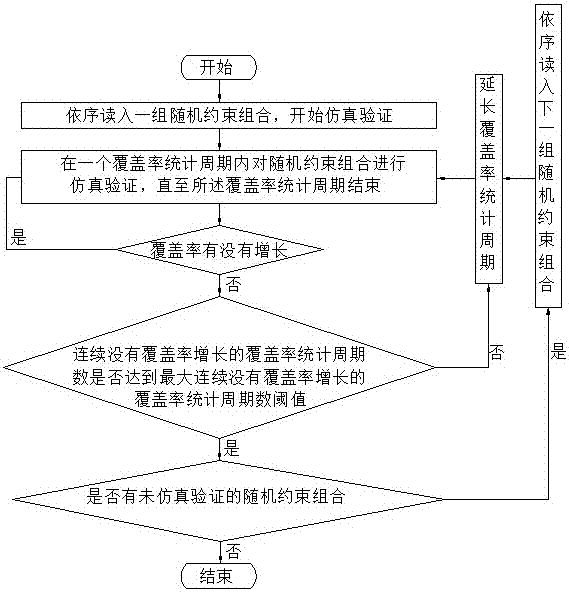
[0067] as attached figure 1 As shown, the optional random verification method based on coverage-driven random constraints of the present invention includes the following steps:
[0068] (1) Clearly define all required random constraints in the random verification environment, and define the value range of the above random constraints;
[0069] (2) Divide the random constraints defined in step (1) into multiple groups of random constraint combinations, and set the simulation order of the above multiple groups of random constraint combinations, wherein there is no actual functional completeness between each two groups of random constraint combinations In the case of overlap, for example, in a system where there are only two nodes, and the interface of each node can only send at most two requests in one clock cycle, the random constraint a limits the node to send only one request per clock cycle, and the random constraint b limits A node only receives one request per clock cycle...
Embodiment 2
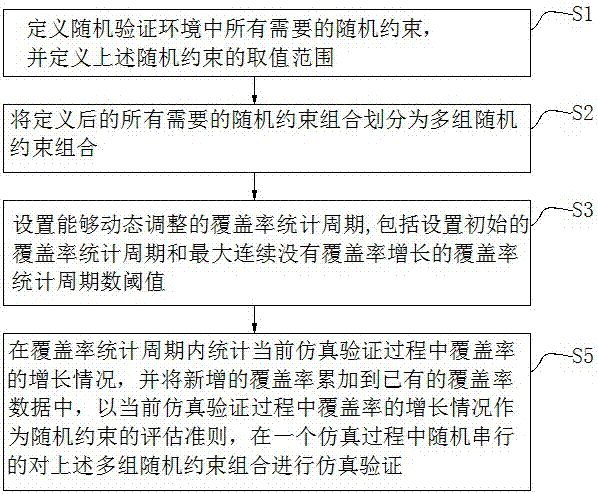
[0085] as attached image 3 As shown, this embodiment is a further improvement on the basis of Embodiment 1. The difference between this embodiment and Embodiment 1 is: in a simulation process, all required random constraint combinations are simulated and verified in random order. This embodiment The difference between embodiment and embodiment 1 is specifically:
[0086]In step (2), the random constraints defined in step (1) are divided into multiple groups of random constraint combinations, and there is no complete overlap of actual functions between each group of random constraint combinations, for example, there are only two nodes, In a system where the interface of each node can only send at most two requests in one clock cycle, the random constraint a restricts the node to send only one request per clock cycle, and the random constraint b restricts the node to receive only one request per clock cycle, then These two constraints are actually equivalent in this system, an...
Embodiment 3
[0098] Embodiment 1 performs simulation verification on all required random constraint combinations in one simulation process, but when the number of random constraint combinations is large, traversing all random constraint combinations through one simulation process is relatively inefficient. In view of the above problems, this embodiment has been further improved on the basis of embodiment 1, as attached Figure 5 As shown, the difference between this embodiment and embodiment 1 is specifically:
[0099] In step (2), the random constraints defined in step (1) are divided into multiple groups of random constraint combinations, and there is no complete overlap of actual functions between each group of random constraint combinations, for example, there are only two nodes, In a system where the interface of each node can only send at most two requests in one clock cycle, the random constraint a restricts the node to send only one request per clock cycle, and the random constrain...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap