RTL hardware Trojan horse detection method based on a gradient lifting algorithm
A hardware Trojan detection and hardware Trojan technology, applied in computing, computer security devices, instruments, etc., can solve problems such as high false alarm rate, limited detection accuracy, and difficult weighting coefficients, achieving high detection accuracy and improving security , the effect of low false alarm rate
Active Publication Date: 2019-04-19
ZHEJIANG UNIV
View PDF8 Cites 6 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
For machine learning detection technology based on gate-level netlist: on the one hand, the detection accuracy of existing methods is limited, and there is a high false alarm rate; on the other hand, the detection method based on gate-level netlist is not It is also difficult to eliminate Trojan horse circuits at the same level
In the RTL detection method, although the method of matching control flow graph subgraphs based on the Trojan horse sample library has a certain detection effect, but in this method, the matching indicators are weighted according to the Trojan horse type. How to determine the weighting coefficient in practical applications There are great difficulties
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
Embodiment 1
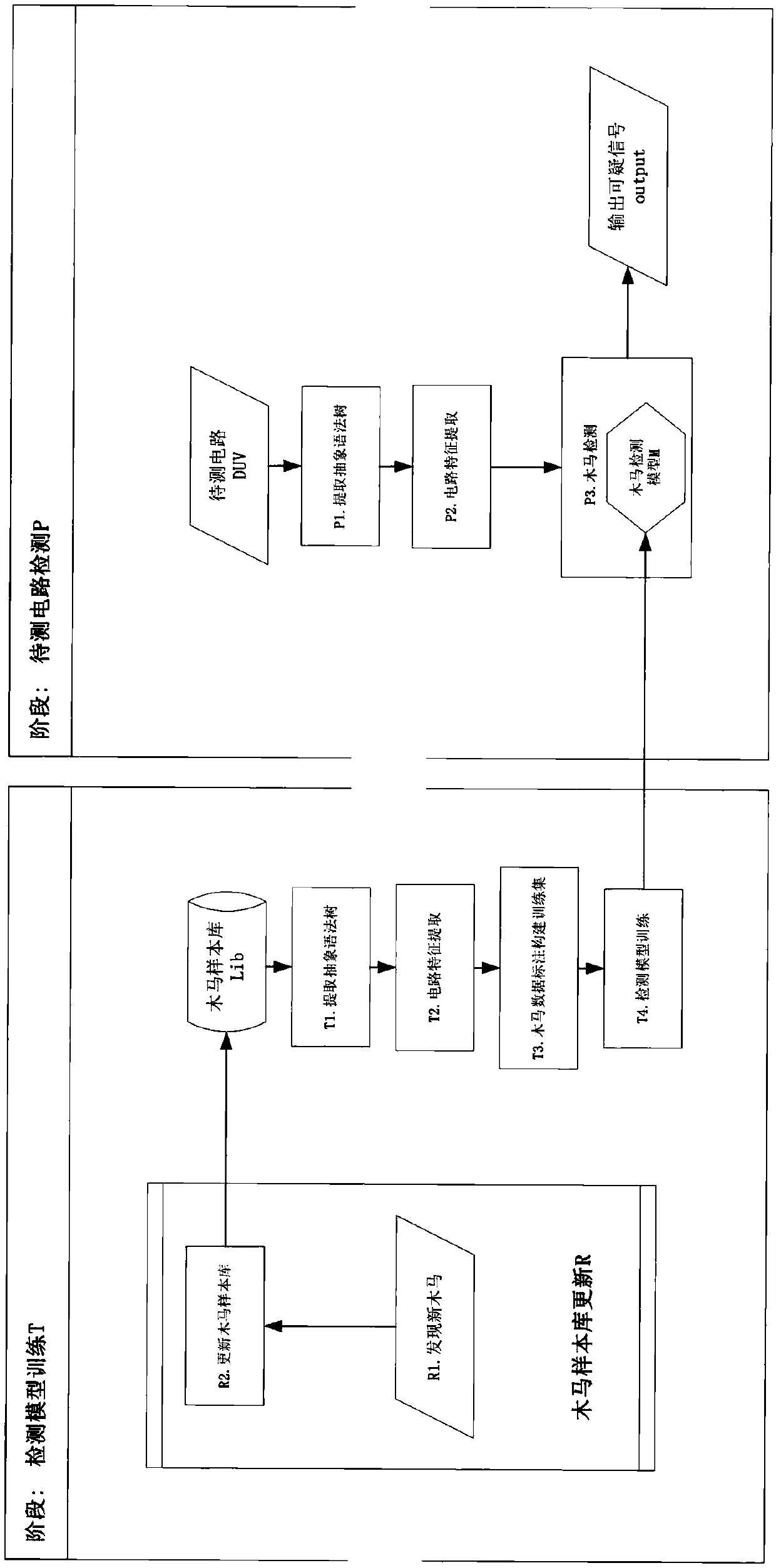
[0076] Embodiment 1, the RTL hardware Trojan detection method based on the gradient lifting algorithm, such as Figure 1~4 shown, including the following:
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
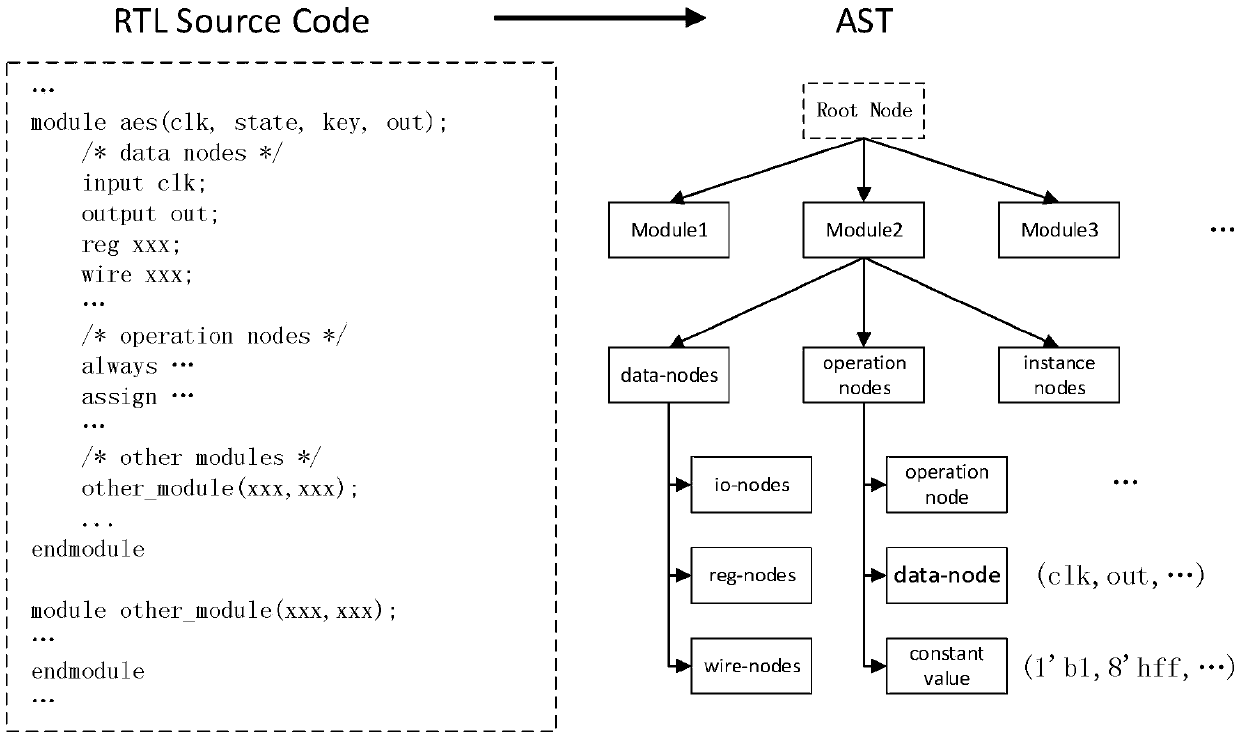
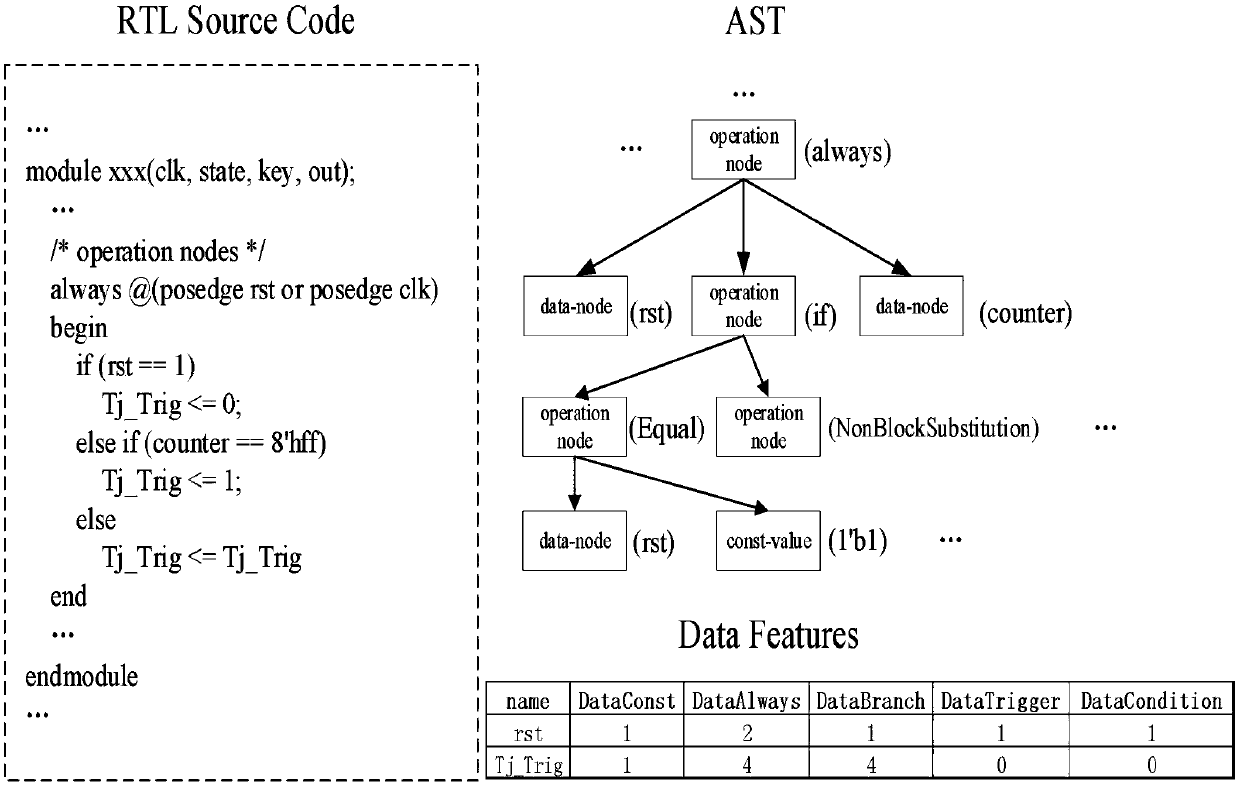
The invention provides an RTL hardware Trojan horse detection method based on a gradient lifting algorithm, and the method comprises the steps: firstly, carrying out the extraction of an abstract syntax tree of a to-be-detected circuit, carrying out the construction and extraction of circuit features of the to-be-detected circuit according to the extracted abstract syntax tree, and obtaining the vectorization feature of each signal node in the to-be-detected circuit; And inputting the vectorized features into a Trojan detection model, detecting the vectorized features by the Trojan detection model, and outputting a label corresponding to each signal node so as to obtain a Trojan detection result corresponding to the signal node. Wherein the Trojan horse detection model is obtained based onXgboost framework training realized by a gradient lifting algorithm; a decision tree model is adopted as a base classifier I for gradient lifting, a new decision tree model is added in the gradient descent direction of a loss function to serve as a base classifier II for improving the classification effect, and an appropriate loss function and an appropriate parameter range are selected through hyper-parameter configuration; The method has the advantages of high detection accuracy, low false alarm rate and high detection efficiency.
Description
technical field [0001] The invention relates to the field of design and manufacture of integrated circuits, and specifically proposes an RTL hardware Trojan horse detection method based on a machine learning algorithm. Background technique [0002] RTL is registertransfer level, which refers to the register transfer level circuit. [0003] Today's integrated circuit technology has profoundly promoted social changes, and integrated circuit chips with complex structures and powerful functions play a very critical role in more and more fields, which makes people pay more and more attention to their safety. However, with the increasingly complex chip structure and the globalization of the chip design and manufacturing process, ensuring the safety and reliability of integrated circuit chips in the design and manufacturing process has become a very challenging task. [0004] In the design process of an integrated circuit chip, it is first necessary to use a hardware description l...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More IPC IPC(8): G06F21/55G06F21/56
CPCG06F21/554G06F21/561
Inventor 韩涛王宇泽李宏亮刘鹏
Owner ZHEJIANG UNIV