Multiple encryption methods for service providers to transmit business messages
A technology for multiple encryption and transmission services, applied in transmission systems and key distribution, can solve problems such as uncontrollable data use, high cracking costs, and long access cycles, and achieve controllable development costs, high cracking costs, and fast online speed Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
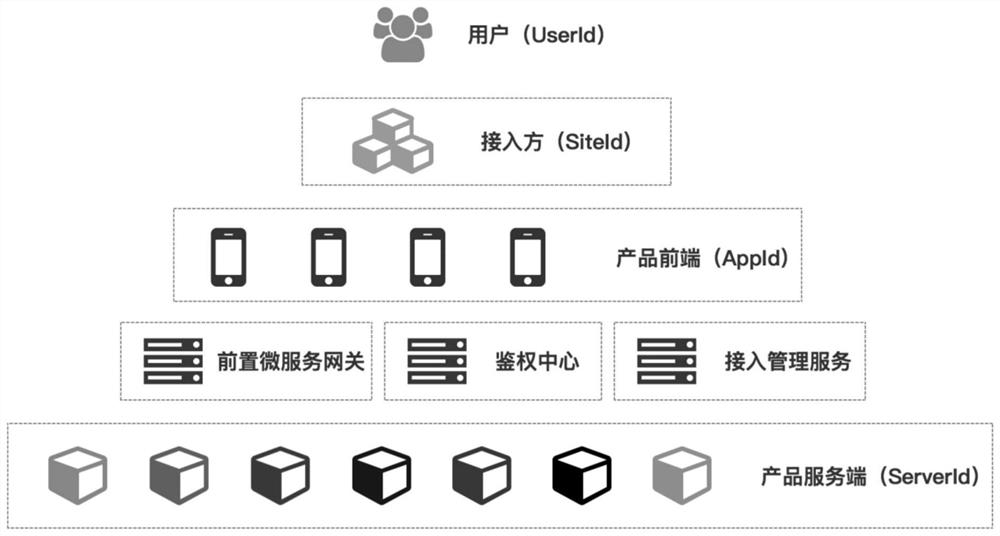
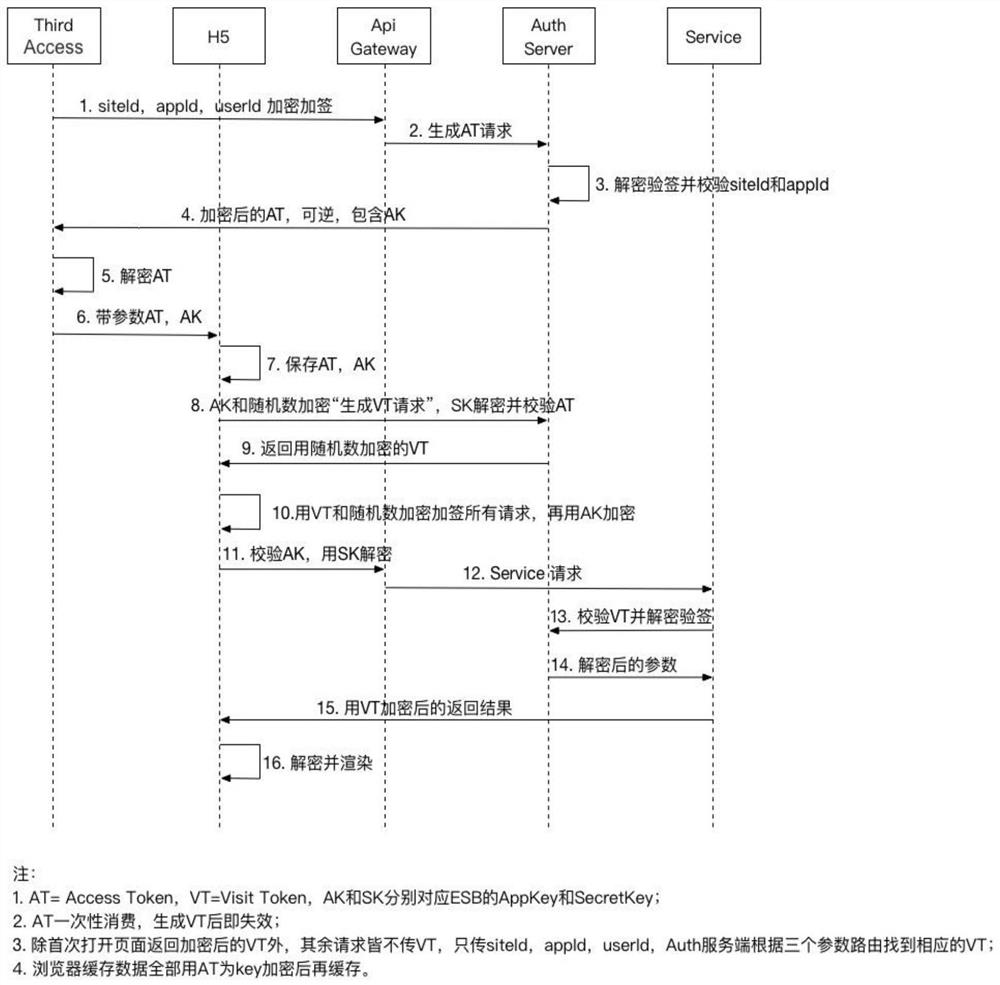
[0037] Such as Figure 1 to Figure 2 As shown, the third-party security access method in the form of H5 application of the service provider includes the third-party backend, the H5 end of the service provider, the gateway server of the service provider, the authentication end of the service provider, and the backend of the service provider. Include the following steps:
[0038] A. The user of the third-party client clicks an entry request to enter the service application provided by the service provider, and notifies the third-party backend of the message;
[0039] B. The third-party backend initiates a request to the service provider to generate an access key AT (Access Token, referred to as AT) through the service provider gateway server, and the service provider generates the access key AT and passes it through the service provider gateway The server returns to the third-party backend;
[0040] C. After the third-party backend receives the encrypted AT, it decrypts the AT...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More