Cross-domain identity authentication method based on edge computing network architecture
A network architecture and edge computing technology, applied in the field of communications, can solve the problems of limited edge computing authentication resources, low network security and efficiency, and exposure of user identity privacy.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0067] Below in conjunction with accompanying drawing and specific embodiment, the present invention is described in further detail:
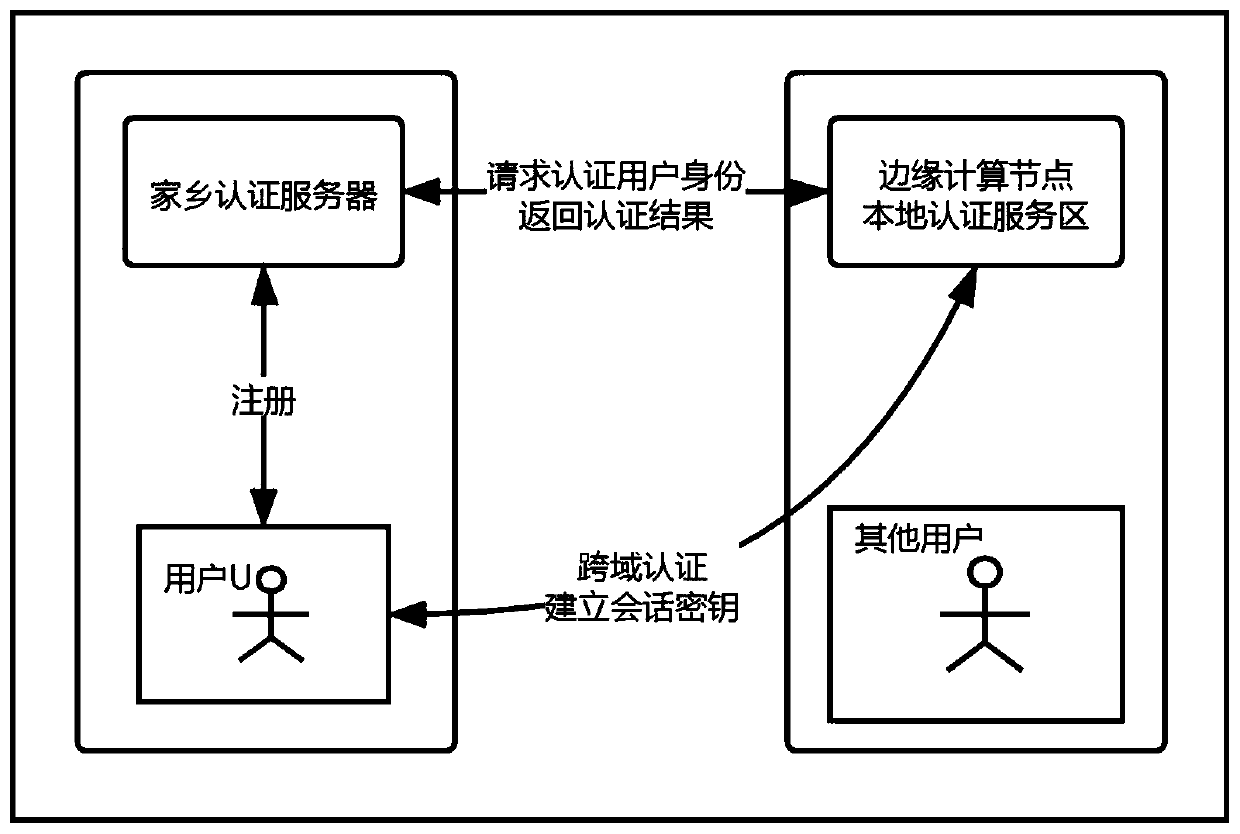
[0068] refer to figure 1 , a schematic structural diagram of a security authentication system applicable to the present invention. The security authentication system applicable to the present invention includes at least a home authentication server, a user and a local authentication server of an edge node, wherein the user is used to make an authentication request to the local authentication server of the edge node, and the home authentication server is used to To verify the legitimacy of the user's identity and return the information to the local authentication server of the edge node, the local authentication server of the edge node is used to generate the user's temporary identity, manage and maintain the user list, and verify the legitimacy of the user.
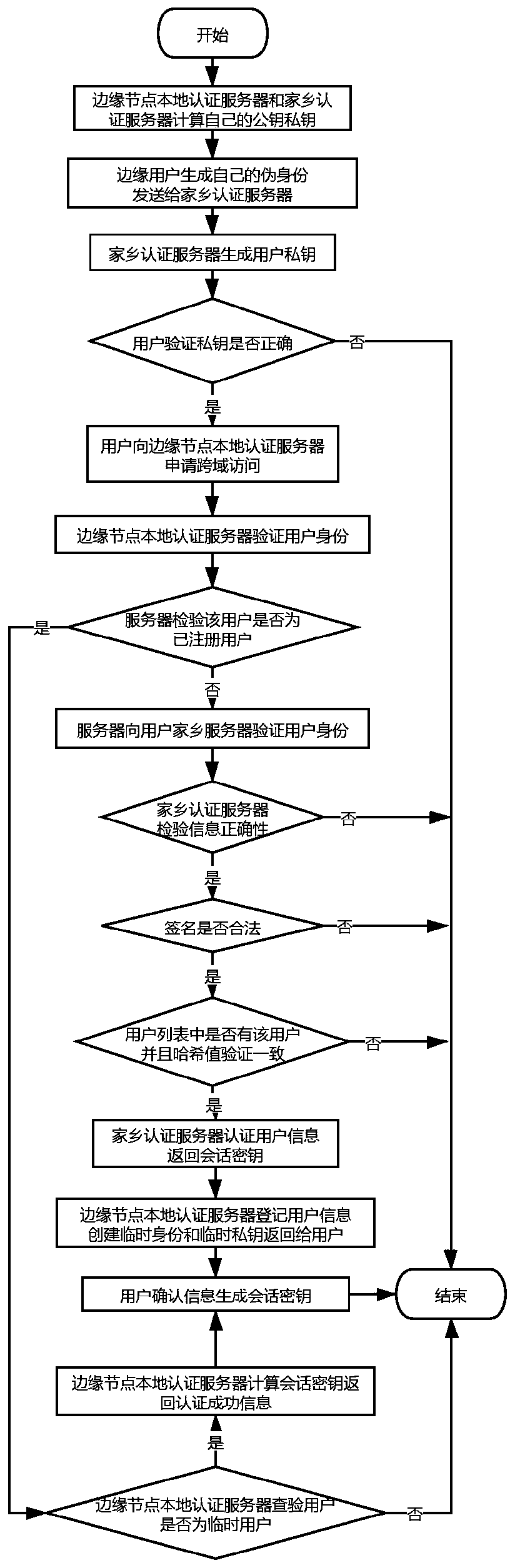
[0069] refer to figure 2 , a cross-domain identity authentication method based on an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More