WLAN association method and system based on block chain
A blockchain and associated device technology, applied in the Internet field, can solve problems such as insufficient intelligence and efficiency in the authentication process, decline in user happiness, and unfavorable city-wide interconnection, and achieve the effects of improving convenience, ensuring security, and simplifying verification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
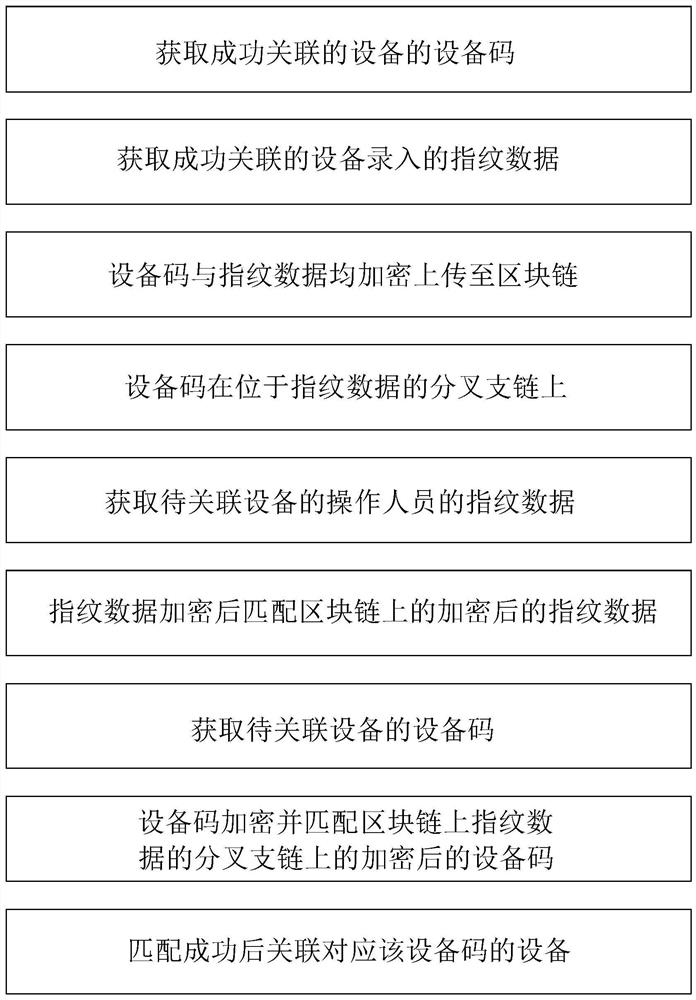
[0037] Blockchain-based WLAN association methods, including
[0038] Obtain the device code of the successfully associated device;
[0039] Obtain the fingerprint data entered by the successfully associated device;
[0040] The device code and fingerprint data are encrypted and uploaded to the blockchain;
[0041] The device code is on the forked branch chain located in the fingerprint data;
[0042] Obtain the fingerprint data of the operator of the device to be associated;
[0043] The encrypted fingerprint data matches the encrypted fingerprint data on the blockchain;
[0044] Obtain the device code of the device to be associated;
[0045] The device code is encrypted and matches the encrypted device code on the branch chain of the fingerprint data on the blockchain;
[0046] After the matching is successful, associate the device corresponding to the device code.
[0047] After the fingerprint data encryption is successfully matched with the encrypted fingerprint data...
Embodiment 2
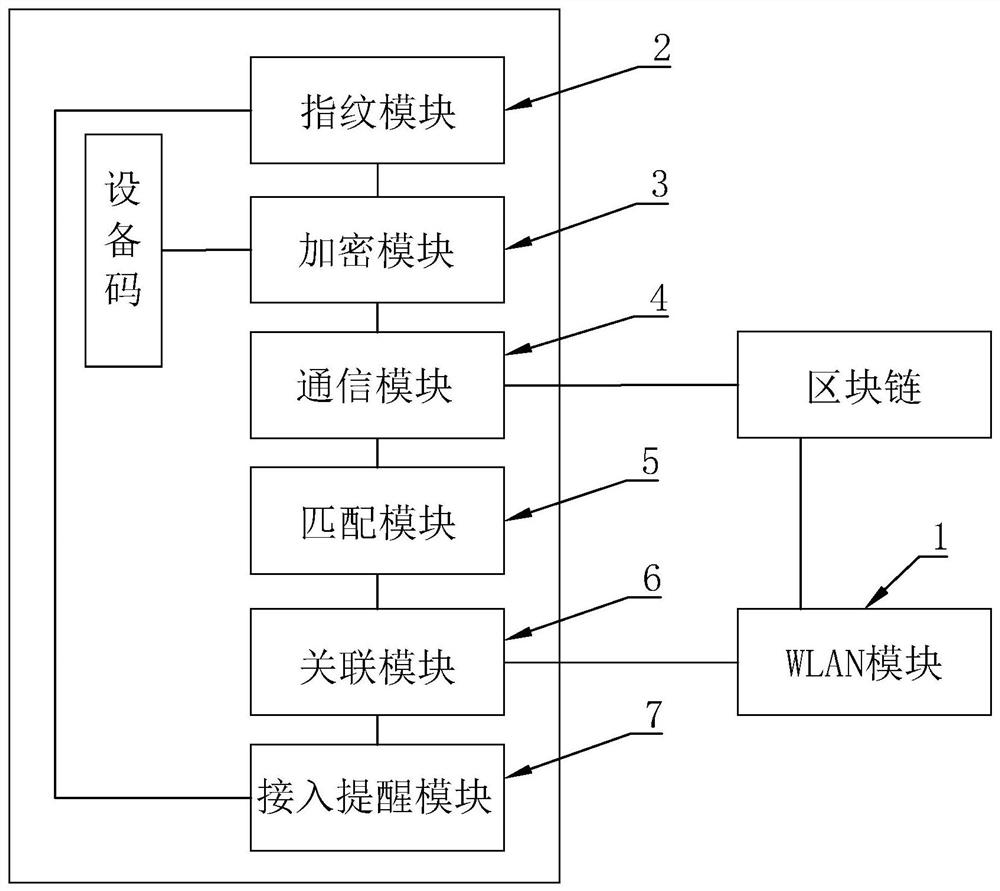
[0054] Blockchain-based WLAN association system, including
[0055] The WLAN module 1 is used to provide a wireless network connection port;
[0056] The fingerprint module 2 is used to obtain the fingerprint data of the equipment operator;
[0057] Encryption module 3, used to encrypt equipment code and fingerprint data;
[0058] The communication module 4 is used to upload the encrypted fingerprint data to the block chain, and upload the encrypted device code to the branch chain of the block chain where the corresponding encrypted fingerprint data is located;
[0059] The matching module 5 is used to match the encrypted fingerprint data of the device sending the association request to the WLAN module 1 with the encrypted fingerprint data on the block chain, and match the encrypted device code of the corresponding device with the block chain where the encrypted fingerprint data is located. Match on the forked branch chain;
[0060] The associating module 6 is configured to...
Embodiment 3
[0066] Based on the solution of Embodiment 2, an access reminder module 7 is also included, which is used to obtain the number of access points and the load under the current WLAN, and pass the number of access points and the load through two groups of squares of different colors and the same size Integrating into display data in the form of two groups of blocks, the number of blocks in the two groups corresponds to the number of access points and the load capacity, and is displayed by a block group composed of several blocks; the display data includes quantity groups, load capacity group, overlapping group, the number group is the block group graphic data composed of blocks corresponding to the number of access points, the load amount group is the block group graphic data composed of blocks corresponding to the load amount, and the two groups of block group diagrams The width of the shape data is the same, the overlapping group is the overlapping display group of the block gro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com