Data flow limiting method and device, electronic equipment and readable storage medium
A technology of data and target traffic, applied in the Internet field, to achieve the effect of ensuring accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0035] To facilitate the understanding of this embodiment, an electronic device that implements a method for limiting data current disclosed in this embodiment of the present application is firstly introduced in detail.
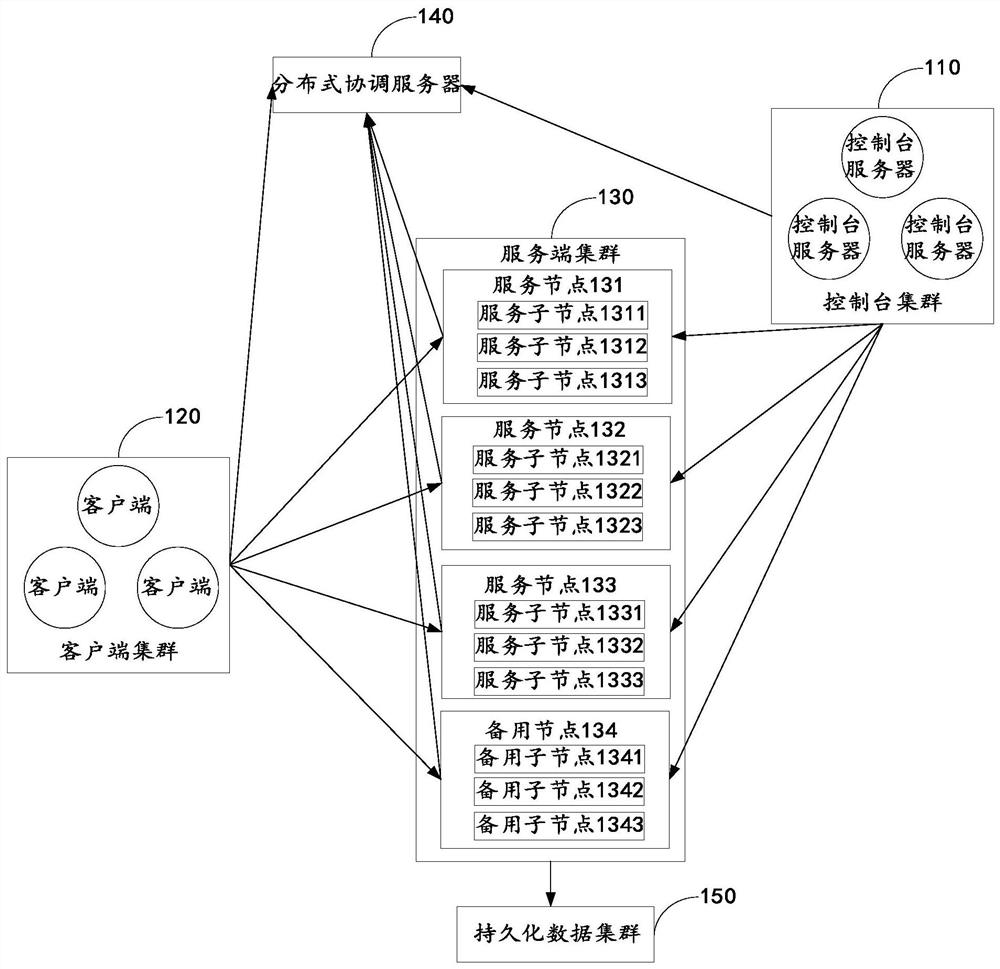
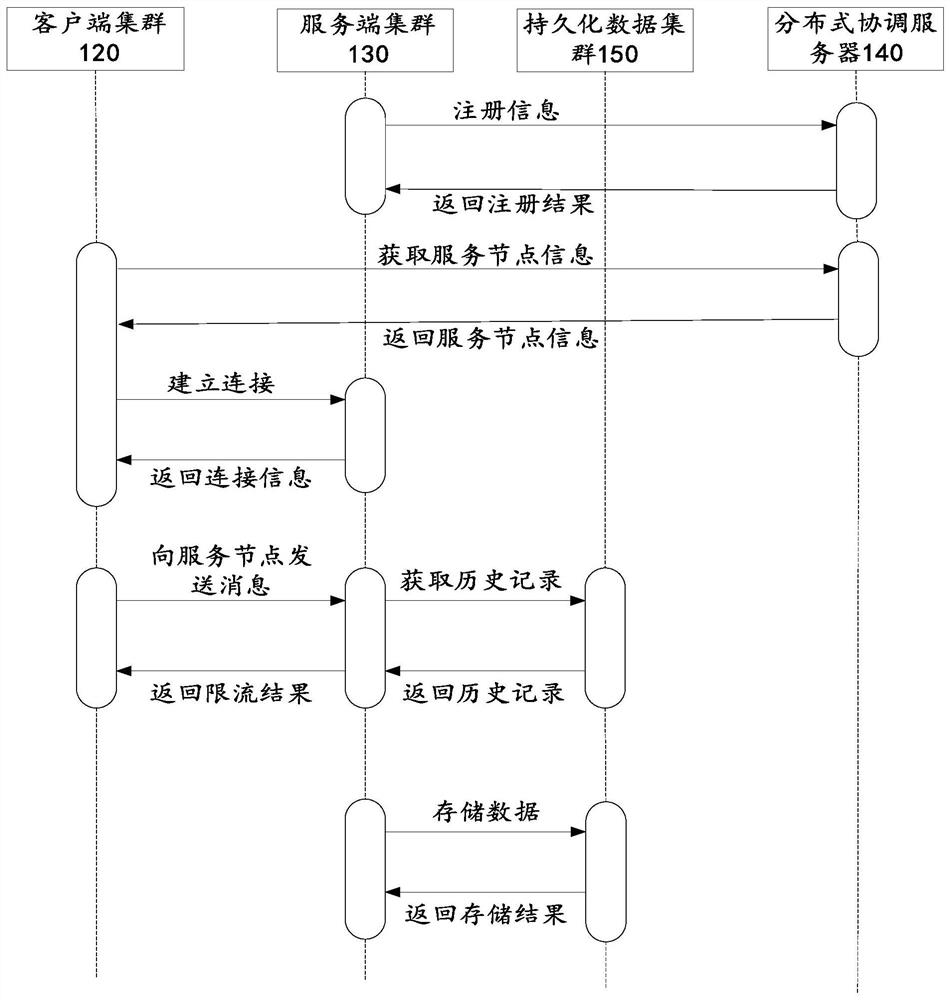
[0036] Such as figure 1 As shown, it is a schematic diagram of the operating environment of the data throttling method provided by the embodiment of the present application. Wherein, the operating environment includes: a console cluster 110 , a client cluster 120 , a server cluster 130 , a distributed coordination server 140 and a persistent data cluster 150 .
[0037] The console cluster 110 may include one or more console servers for communicating with the server cluster 130 to monitor the server cluster 130 . The console server may be a network server, a database server, or a personal computer (personal computer, PC), a tablet computer, a smart phone, a personal digital assistant (personal digital assistant, PDA) and the like. The console cluster 110 can...
Embodiment 2
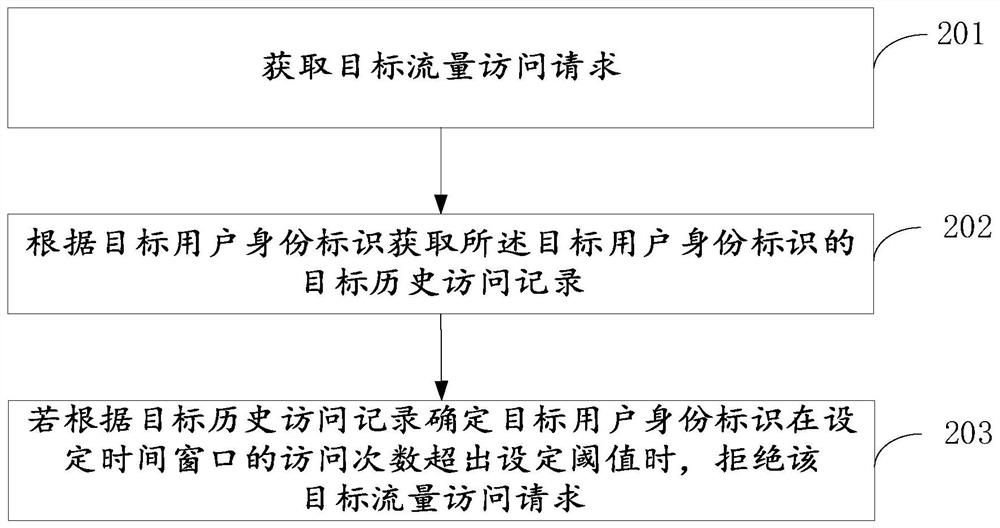
[0054] see image 3 , is a flow chart of a data rate limiting method provided in an embodiment of the present application. The following will be image 3 The specific process shown will be described in detail.
[0055] Step 201, obtaining a target traffic access request.
[0056] Optionally, the target traffic access request carries a target user identity.
[0057] Optionally, the target user identity includes, but is not limited to, the target user's identity information, the target user's access data, the target user's spatial naming (such as an access record list), and the like.
[0058] Step 202, acquiring the target historical access records of the target user ID according to the target user ID.
[0059] Optionally, the target historical access record is access data within a set time window identified by the target user identity.
[0060] Optionally, a record is formed in a time period, and each visit updates the access data recorded in the corresponding time period....
Embodiment 3
[0122]Based on the same application idea, a data current limiting device corresponding to a data current limiting method is also provided in the embodiment of the present application. Since the problem-solving principle of the device in the embodiment of the present application is the same as that of the aforementioned data current limiting method The embodiments are similar, so the implementation of the device in this embodiment can refer to the description in the embodiment of the above method, and the repetition will not be repeated.
[0123] see Figure 6 , is a schematic diagram of functional modules of a data current limiting device provided in an embodiment of the present application. Each module in a data current limiting device in this embodiment is used to execute each step in the above method embodiment. A data current limiting device includes an acquisition module 301, a request module 302, and an output module 303; wherein,
[0124] Obtaining module 301: used to...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More