Authentication security level and resource optimization method for computing offload in edge computing network
An edge computing and computing offloading technology, applied in the field of communications, can solve the problems of expensive security, occupying idle bandwidth resources, and large transmission packets, and achieve the effect of saving energy consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0086] In order to make the objectives, technical solutions and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the embodiments. It should be understood that the specific embodiments described herein are only used to explain the present invention, but not to limit the present invention.
[0087] In view of the problems existing in the prior art, the present invention provides an authentication security level and resource optimization method for computing offload in an edge computing network. The present invention is described in detail below with reference to the accompanying drawings.
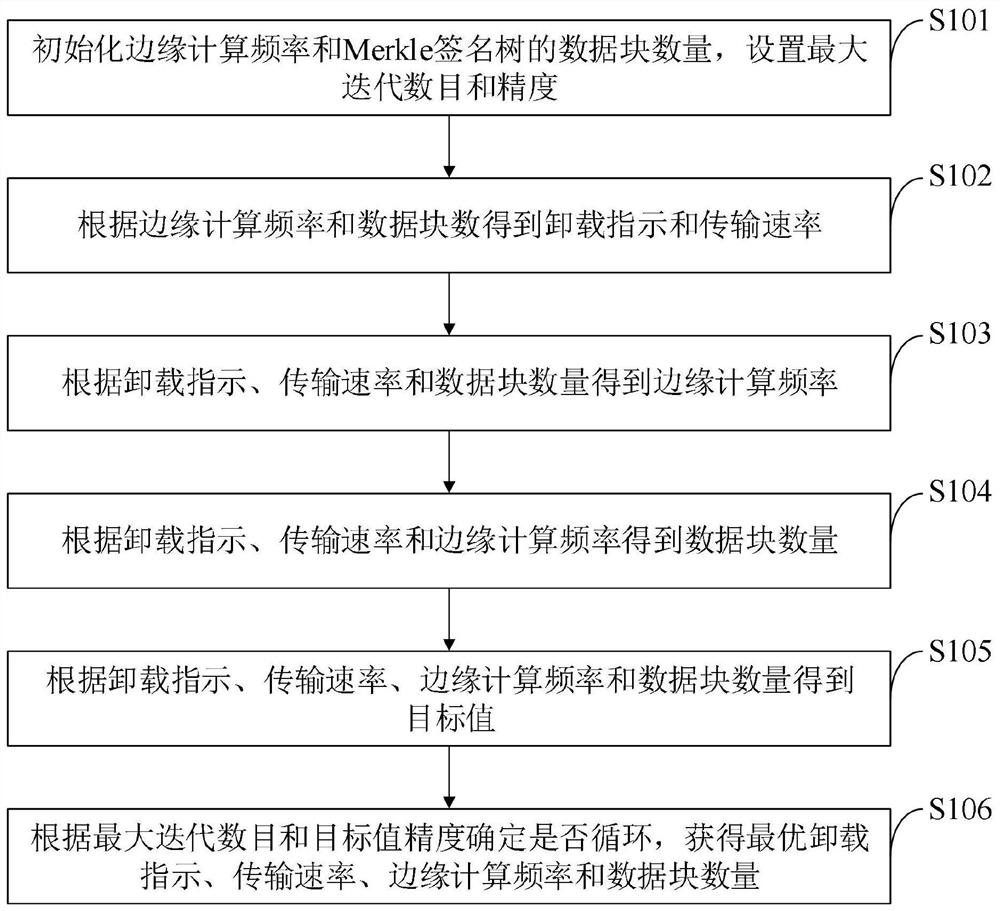
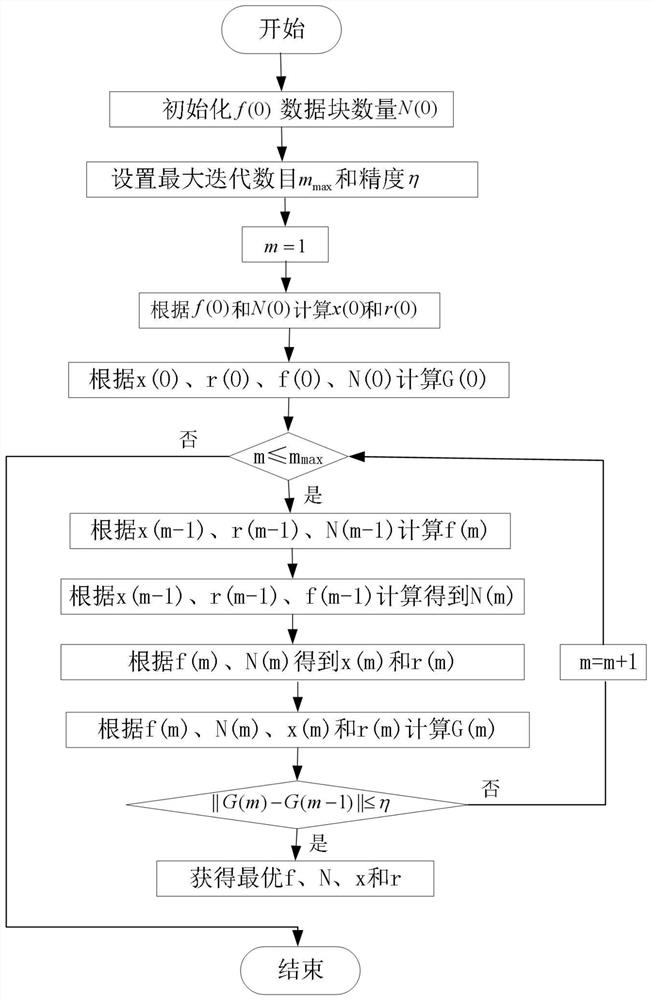
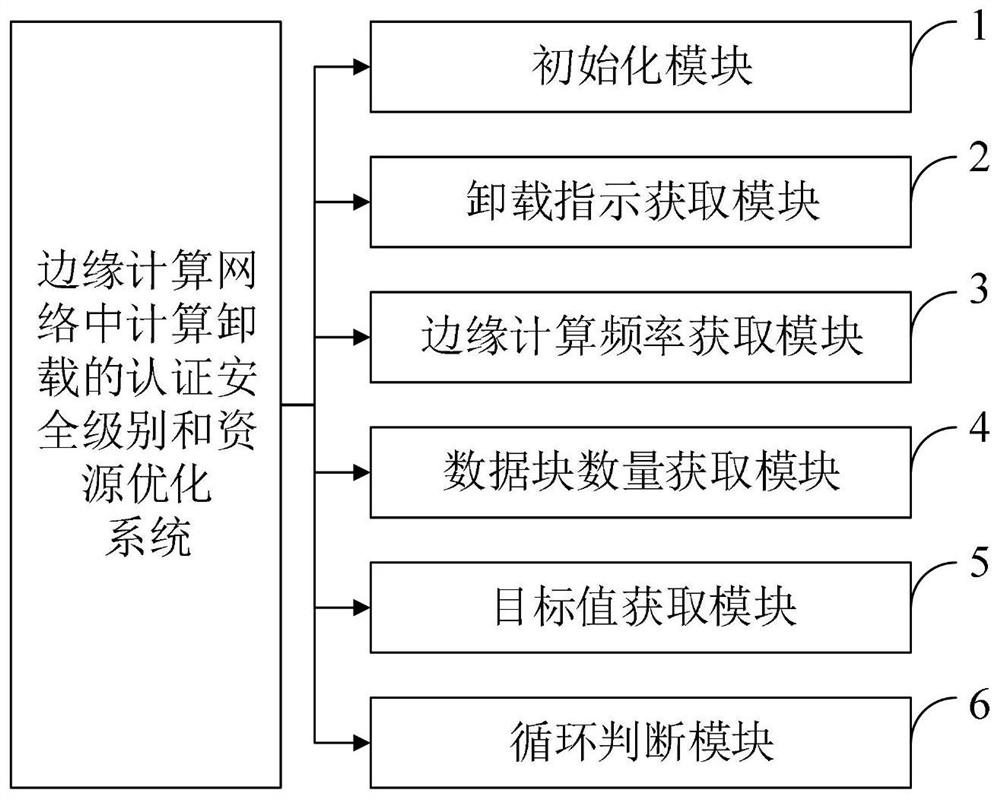
[0088] like figure 1 As shown, the authentication security level and resource optimization method for computing offload in an edge computing network provided by the embodiment of the present invention includes the following steps:
[0089] S101, initialize the edge computing frequency and the number of data blocks ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More