Resource access control method based on zero-trust single packet authentication and authorization
A resource access, zero-trust single technology, applied in the field of information security, can solve problems such as network security threats, achieve the effect of improving efficiency, improving network security, and reducing network attack surface
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present invention.
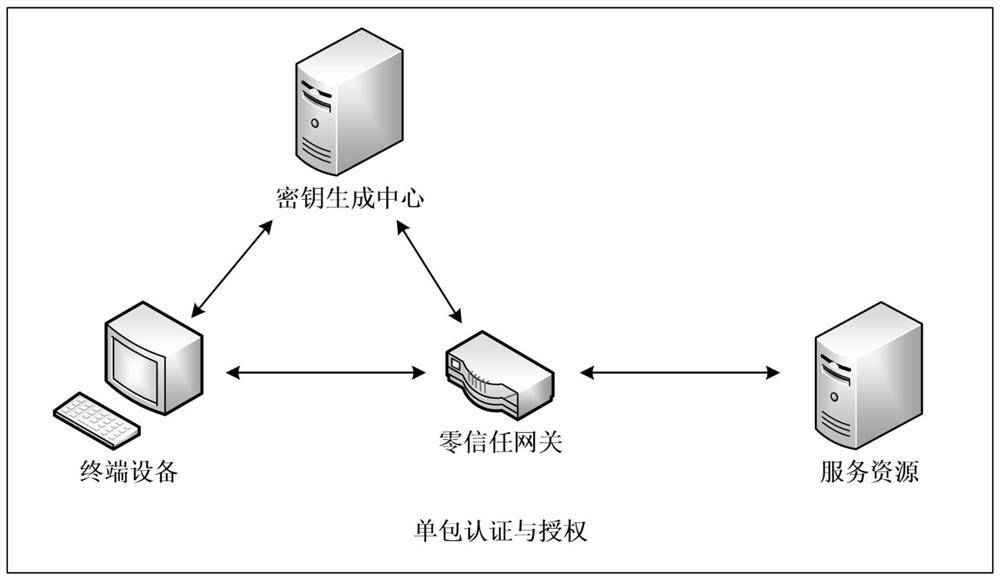
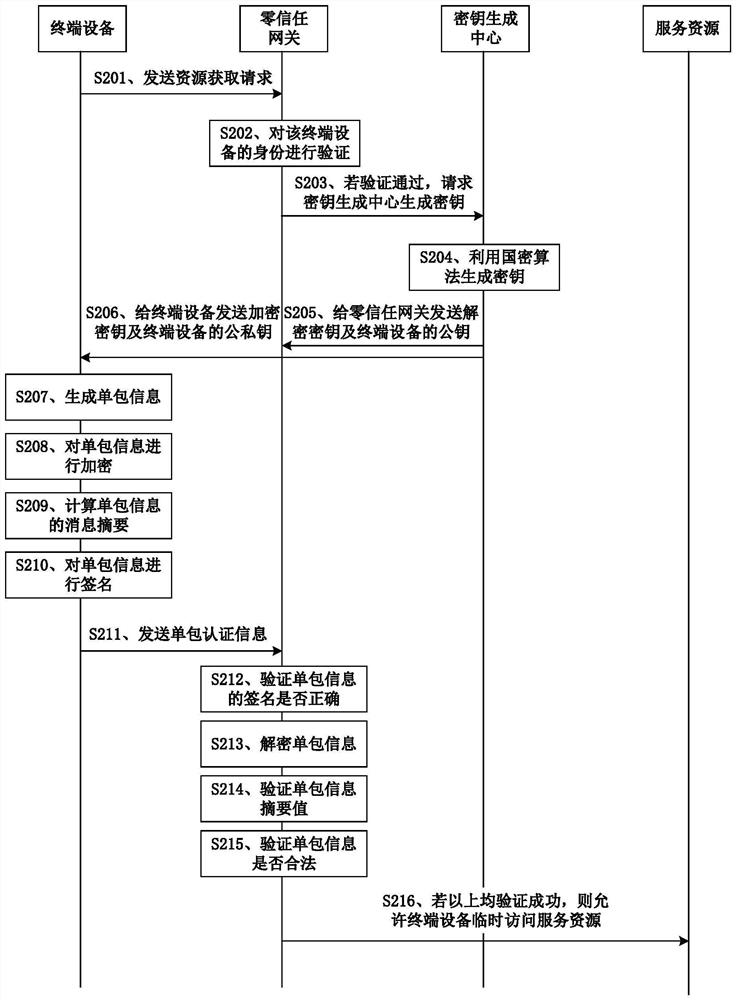
[0027] like figure 1 As shown, a system framework diagram of resource access control based on zero-trust single-package authentication and authorization, the system framework includes terminal equipment, zero-trust gateway, key generation center and service resources.
[0028]Terminal equipment or also called terminal, can be a kind of equipment with wireless transceiver function, which can be deployed on land, including indoor or ou...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More