For example, although
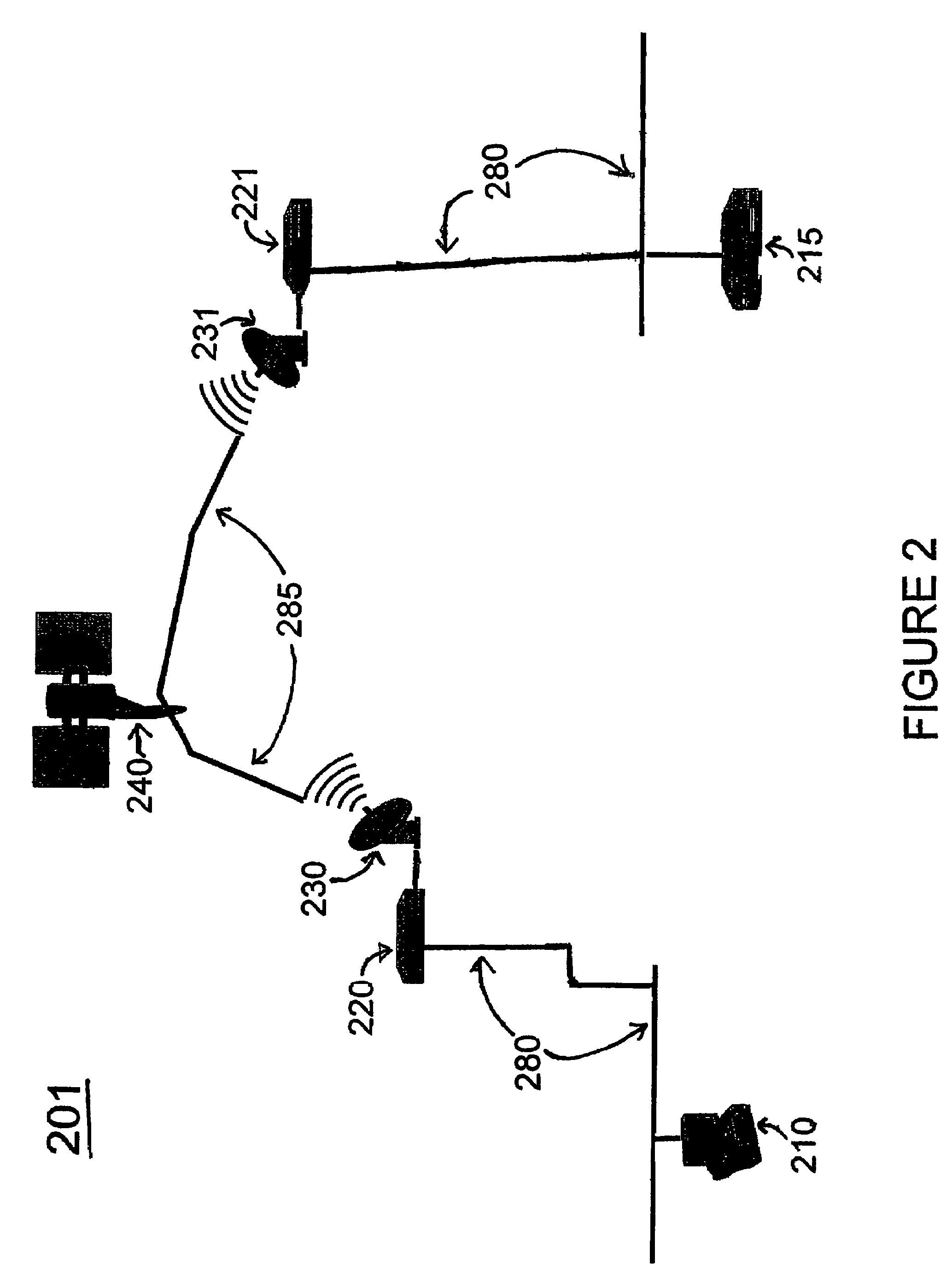
satellite networks have advantages such as permitting telecommunication across any distance without laying ground lines, the distance between the ground and the satellite introduces significant
transmission delay.
As another example, cellular
wireless networks contain many packet switches, each of which introduces some latency; the cumulative
delay can exceed that of a satellite link.
As a result of the distance traveled by transmissions from one node (e.g., a
ground station) to another node via a satellite, significant transmission delays may be incurred.
Such delay causes certain performance issues for voice applications.
For example, problems such as “conversation collisions” occur wherein both parties start talking at the same time because neither can hear that the other party is also talking.
Data protocols within satellite and other high-latency networks also face problems with long delays.
Two problems in particular handicap the use of satellite networks for data applications:
throughput limitation and partial security.
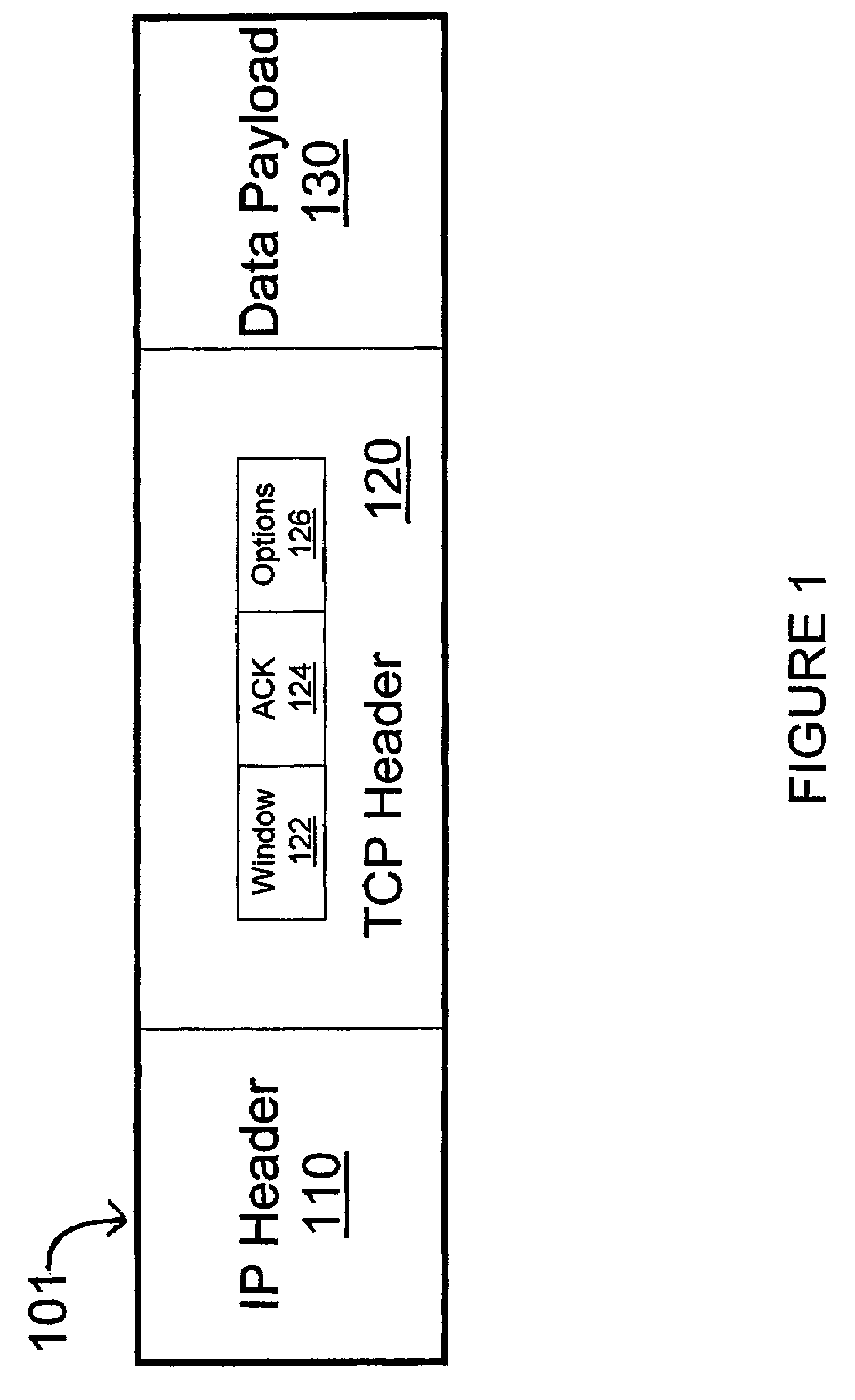
However, in a
satellite network, the inherent delay caused by long-distance transmission results in each sending TCP device being required to wait idle for each
acknowledgement.
In practice, this forced wait limits the average transmission speed to approximately 130 kbit / s, regardless of the channel bandwidth of the satellite transmission.
An additional problem is that a TCP device may misinterpret the inherently long delay as
network congestion.
This
algorithm implemented by TCP further reduces the efficiency of a channel impaired by high latency.
A second drawback in using satellite communication is low security.
However, hub earth stations are seldom at customer sites and so there will likely exist a terrestrial segment that is not protected by the satellite
service provider.
Prior art solutions for each problem (i.e.,
throughput limitation and low security) do exist, but each have their own respective drawbacks.
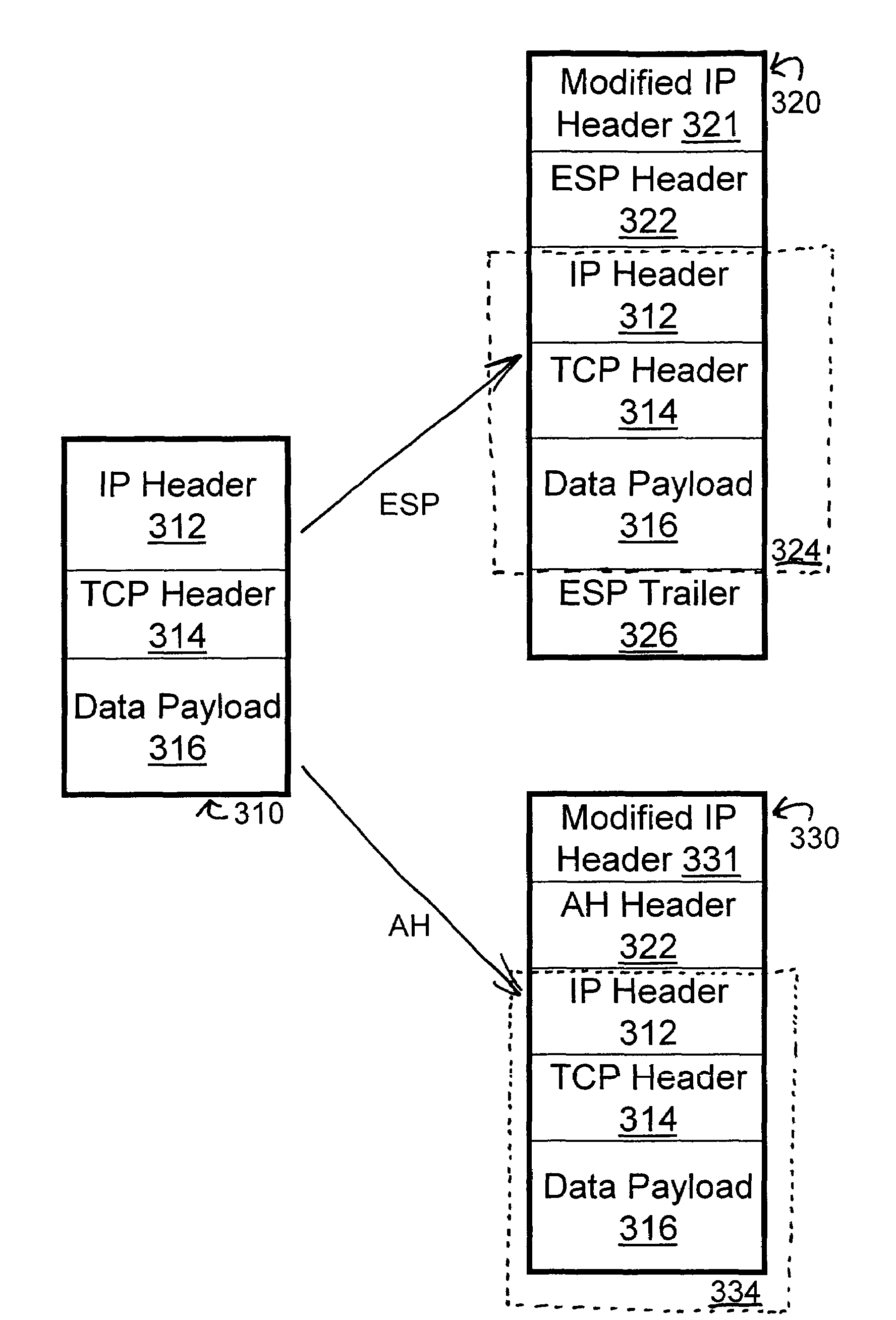
This total
encryption, however prevents the PEP device from seeing or modifying the original TCP header 314 (specifically, the ACK and Window fields of the header), so these sessions cannot be accelerated by PEP devices.
Any change in the protected TCP header (like those changes made by PEP devices) will result in a failure of the
authentication process and a rejection of the protected packet.
The result is that a PEP device that has just decrypted data will send unencrypted data to an
IPsec router.
Even though the
IPsec router may be
proximate to the PEP device, the existence of an “unencrypted six inches” on the cable between an
IPsec router and a PEP is unacceptable to many enterprises and government agencies as they often require complete end-to-end
confidentiality.
The result of these problems has been a conflict between maximizing
throughput and maximizing
high security using IPsec VPNs.
In summary, standard IPsec cannot be accelerated by PEP devices; the additional
processing time to encrypt / decrypt (and compress / decompress) further lengthens the ACK cycle,
cutting throughput and reducing security.
 Login to View More
Login to View More  Login to View More
Login to View More