A Stream Cipher Key Control Method Fused with Neural Network and Chaotic Map
A technology of chaotic mapping and neural network
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] The present invention will be further described below in conjunction with the accompanying drawings.
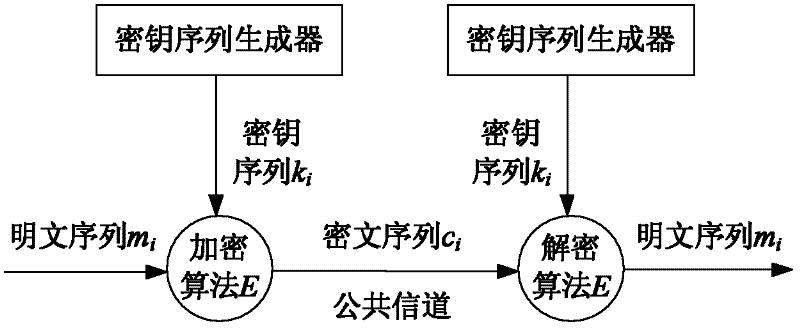
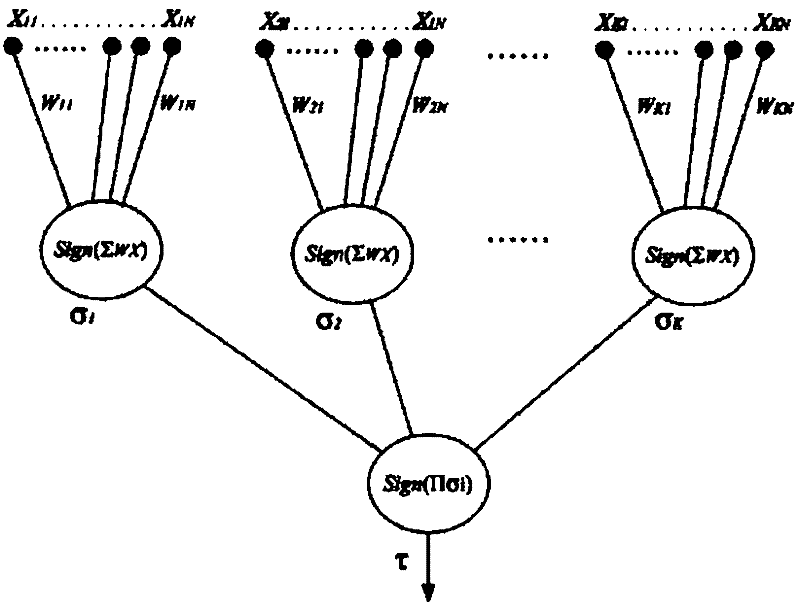
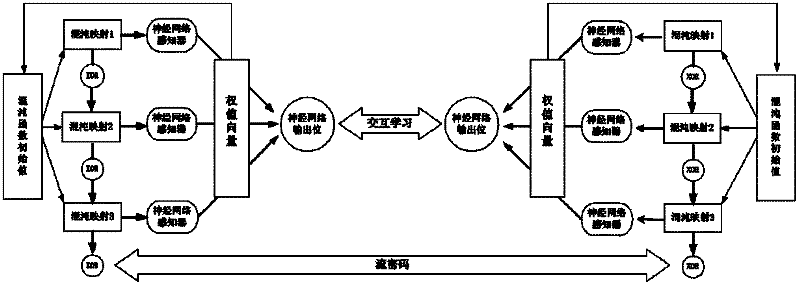
[0058] refer to Figure 2 ~ Figure 4 , a stream cipher key control method that integrates neural network and chaotic map, setting the neural network weight synchronization model with the same parameters for the sender and the receiver and three chaotic map functions with the same initial value respectively, setting the sender Having the same initial value of the chaotic function as the receiver, the stream cipher key control method includes the following steps:
[0059] (1) Determine the mixed key stream generator based on 3 chaotic maps:
[0060] XOR the random bits generated by the three chaotic maps to get the final random sequence, namely:
[0061] Mixed chaos map sequence = (chaos map 1 sequence) XOR (chaos map 2 sequence) XOR (chaos map 3 sequence);
[0062] Among them, the initial values of the chaotic map 1 sequence, the chaotic map 2 sequence, and the cha...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More