Wireless safety authentication method orienting to mobile terminal
An identity verification method and mobile terminal technology, applied in the field of wireless security identity verification, can solve problems affecting system security, achieve the effects of preventing malicious registration, reducing the risk of malicious access, and preventing replay attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] The present invention will be further described below in conjunction with accompanying drawing.
[0040] Step (1). Mobile terminal registration:
[0041] 1-1. Fill in the registration form on the mobile terminal, and send the user information of the registration form to the authentication server.
[0042] 1-2. After receiving the user information sent by the mobile terminal, the authentication server searches the local database for the record of the user name (Email) in the user information. If the user name already exists, it prompts that the user has registered; if the user name does not If present, registration is allowed.
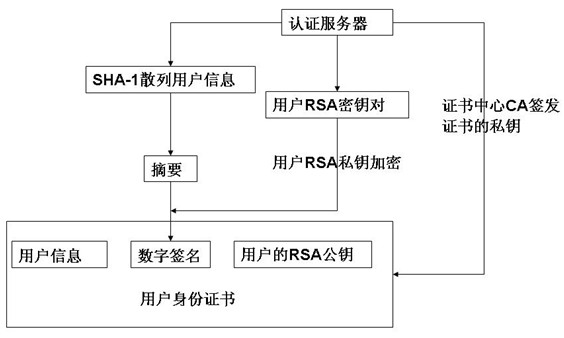
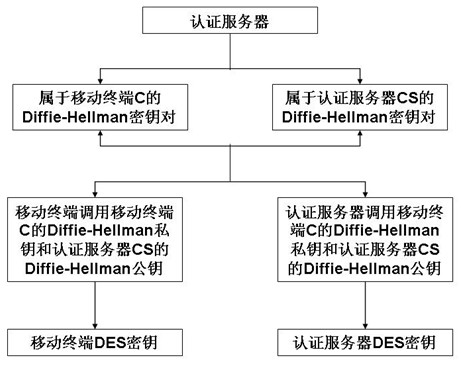
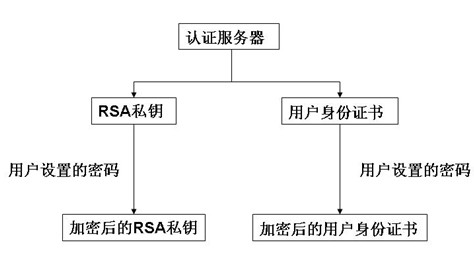
[0043] 1-3. During the registration process, the authentication server generates the user identity certificate, the user RSA private key, the Diffie-Hellman (DH) key pair belonging to the mobile terminal C and the Diffie-Hellman (DH) key pair belonging to the authentication server CS ;like figure 2As shown, the authentication server invokes t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More