Crypto-operation supporting microprocessor, method and system
A microprocessor and processing method technology, applied in transmission systems, digital transmission systems, user identity/authority verification, etc., can solve problems such as inflexibility, and achieve high performance and efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
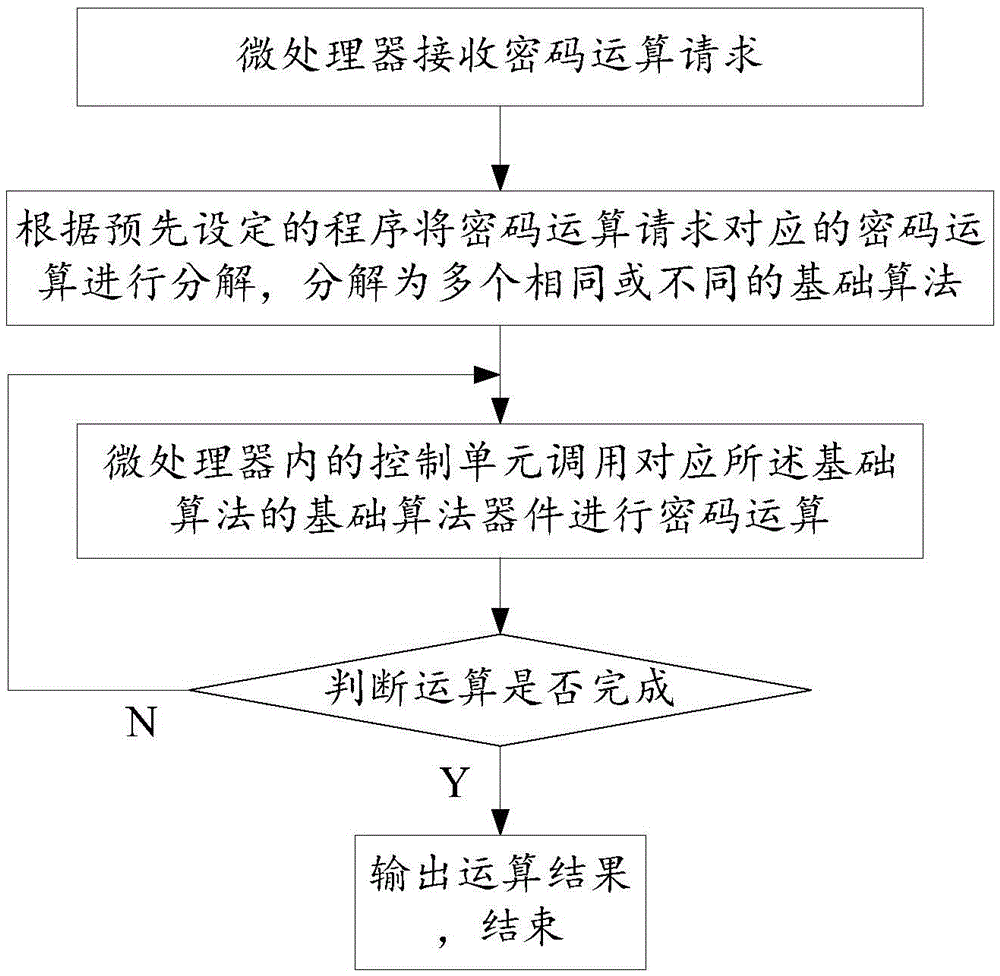
[0047] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
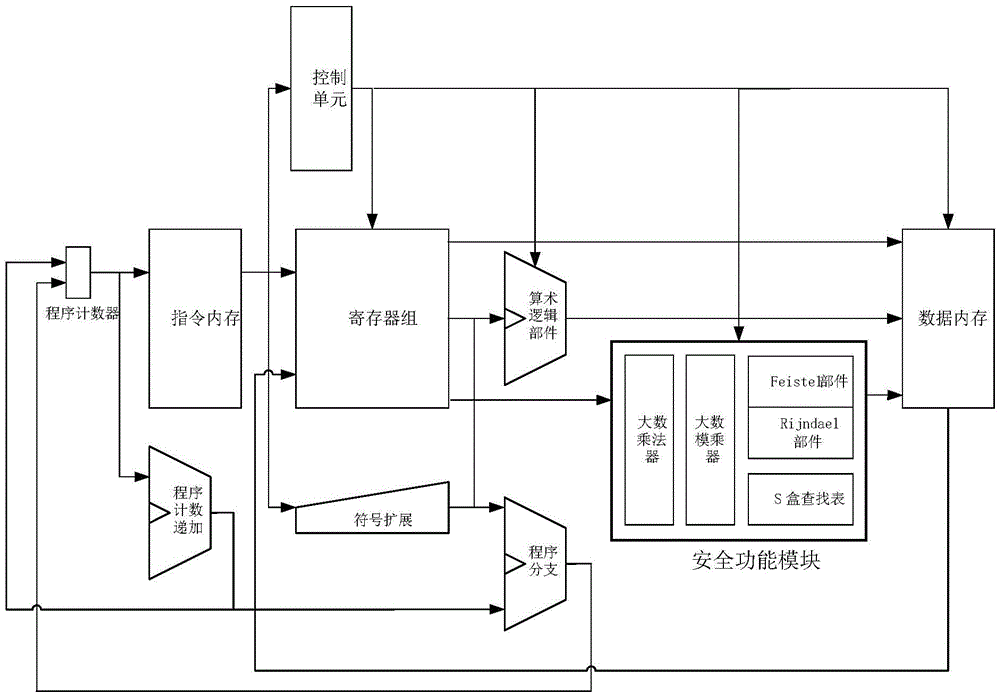
[0048] A microprocessor supporting cryptographic operations described in Embodiment 1 of the present invention is characterized in that it includes a security function module built in the microprocessor;
[0049] The safety function module integrates at least one basic algorithm device.
[0050] In Embodiment 2 of the present invention, on the basis of Embodiment 1, a control unit is further included, and the control unit schedules the basic algorithm devices in the safety function module according to the settings to realize the operation of complex algorithms.
[0051] In Embodiment 3 of the present invention, on the basis of Embodiment 1 or 2, the basic algorithm device includes a large number multiplier, a large ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More