Host kernel data reduction and protection method
A core data, active protection technology, applied in digital data protection, electrical digital data processing, platform integrity maintenance, etc., to reduce overhead, reduce performance overhead, and improve reliability.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
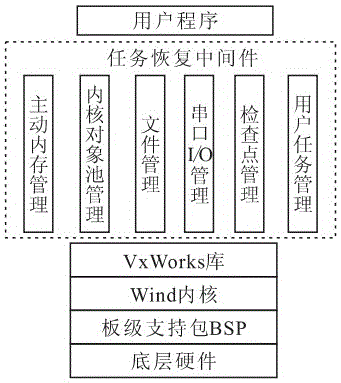
[0029] refer to figure 1and figure 2 As shown, the present invention provides a host kernel data restoration and protection method, which is divided into two parts: establishing a kernel data restoration method system and designing a kernel data active protection prototype system.
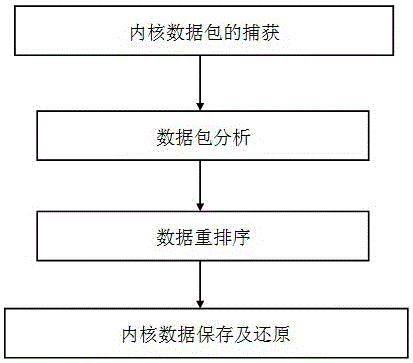
[0030] A. Establish the kernel data restoration method system as follows:
[0031] Before realizing kernel data restoration, it is first necessary to obtain kernel data and perform corresponding processing on it, including analysis and reorganization sorting. This restoration method first captures kernel data packets, and the kernel uses the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More