Cloud Computing Information Security Visualization System Based on Trusted Computing
A technology of trusted computing and information security, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0059] The present invention will be further described in detail below through specific embodiments and in conjunction with the accompanying drawings.
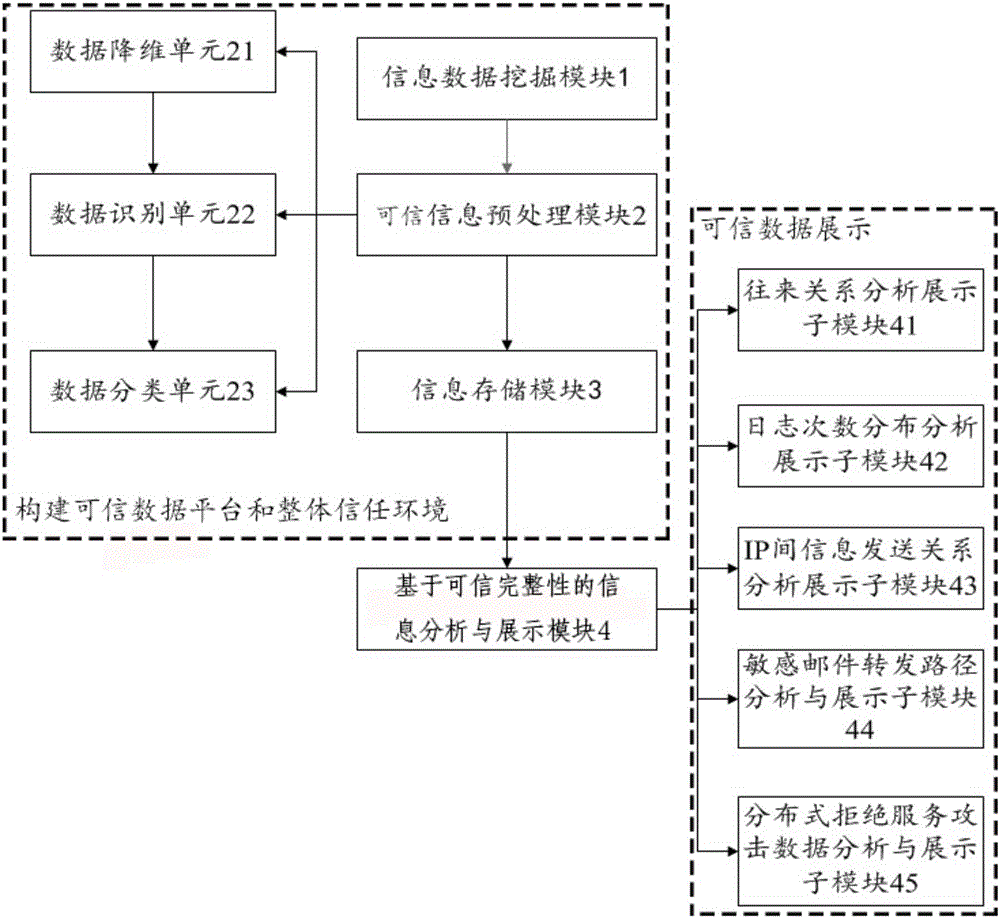
[0060] see figure 1 , the cloud computing information security visualization system based on trusted computing in this embodiment includes an information data mining module 1, a trusted information preprocessing module 2, an information storage module 3 and an information analysis and display module based on trusted integrity that are connected in sequence 4;
[0061] The information data mining module 1 authenticates the hardware nodes in the network for information collection, judges the reliability of the network hardware nodes, establishes the trust relationship of the collected information, and obtains the original information by grabbing network data packets in the local area network. Data, the original information data includes three types of data types: detection data of sensitive information transmission between IPs,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More