Decentralized public key management method and system based on trusted network
A technology of decentralization and management method, applied in the field of information security, can solve the problems of loose organization and not being widely used, and achieve the effect of accurate verification and guarantee of validity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
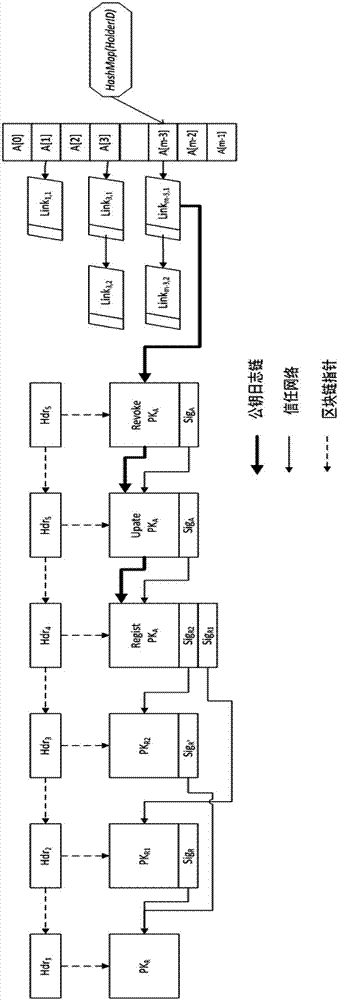
[0072] 1) Decentralized platform structure
[0073] This embodiment is built on the basis of the block chain system, such as Figure 6 As shown, the blockchain network includes the following entities:
[0074] ① System member P:={P 1 ,...,P n}: for each member P i It is an independent execution node of the system and stores a copy of the blockchain BC;
[0075] ②Distributed network net: a P2P network that ensures the interconnection between members in the system;
[0076] ③Block storage structure BC:={B 1 ,...,B n}: Blockchain is composed of many data blocks B i A distributed storage structure composed of each data block B i :={hdr i , body i} consists of a "block header hdr i " and a "data store body" containing a certain number of data records i " consists of two parts;
[0077] ④Consensus agreement: An agreement to ensure that all members in the blockchain system cooperate with each other and obtain common results, such as mining mechanism, Byzantium consensus ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More