System and method for resisting physical attacks of printer
A physical attack and printer technology, applied in the field of information security, can solve problems such as data leakage, low security, illegal memory and interface data, etc., and achieve the effects of reducing performance impact, comprehensive protection range, and improving encryption efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0068] The present invention will be described in further detail below with reference to the accompanying drawings and specific embodiments.
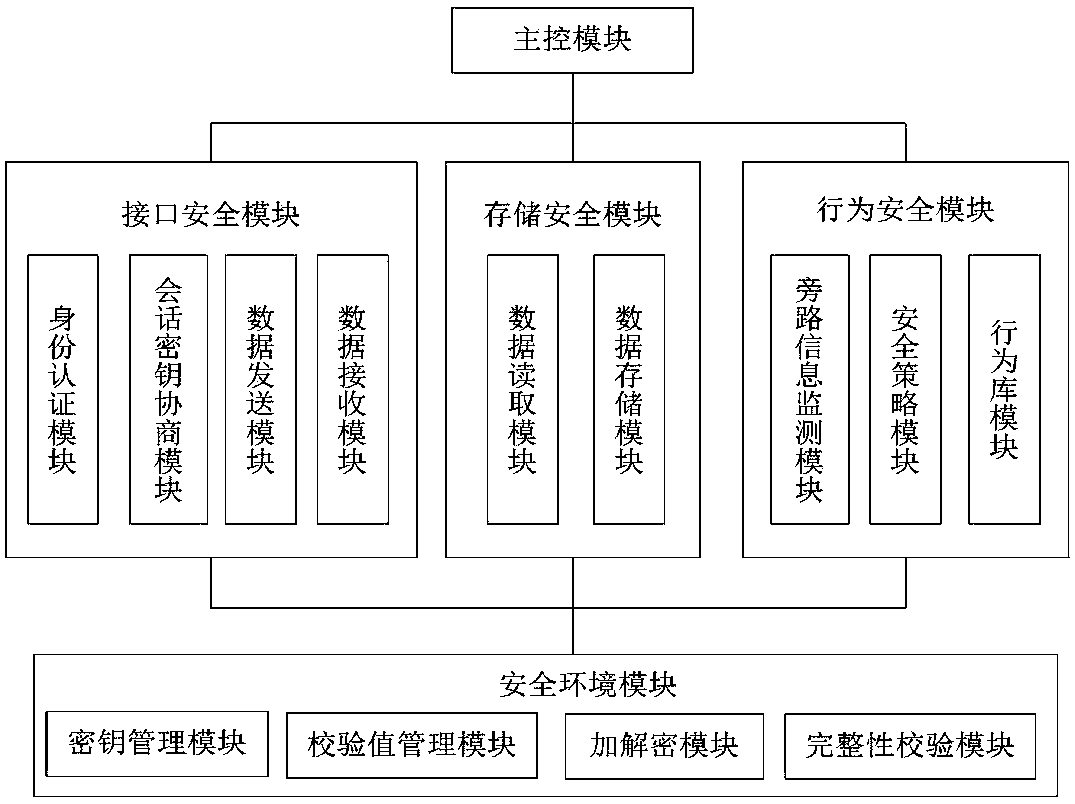
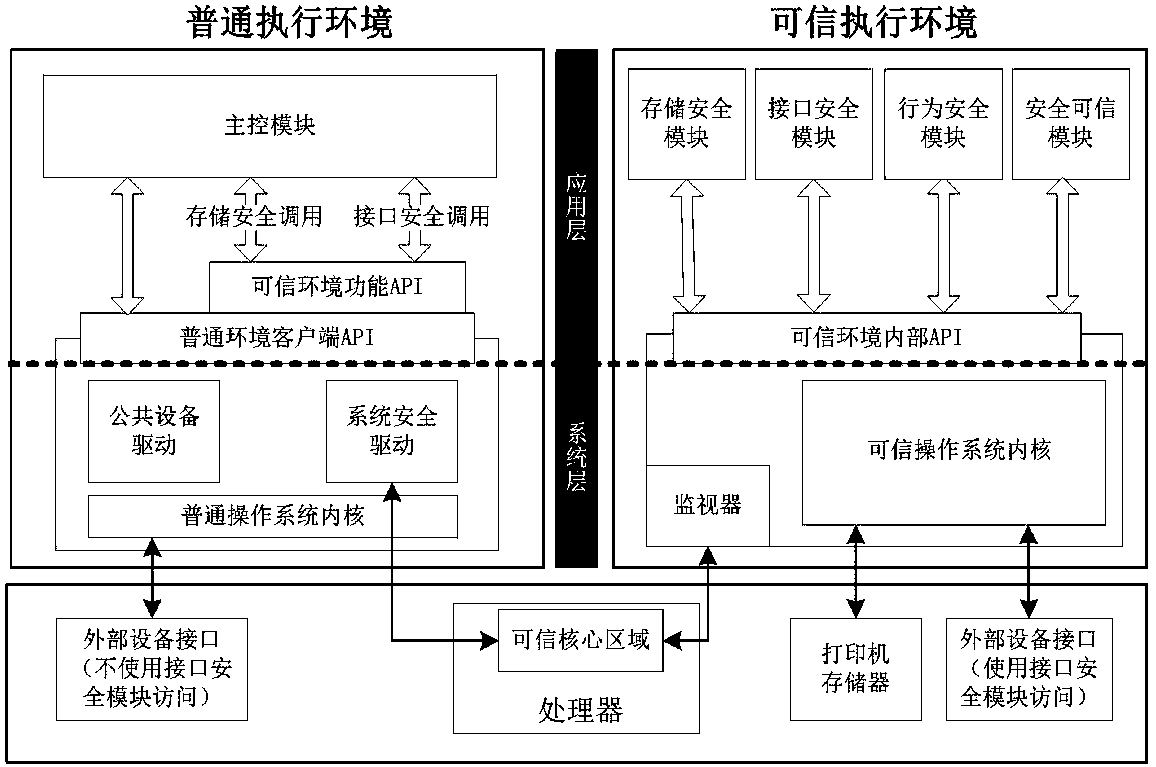
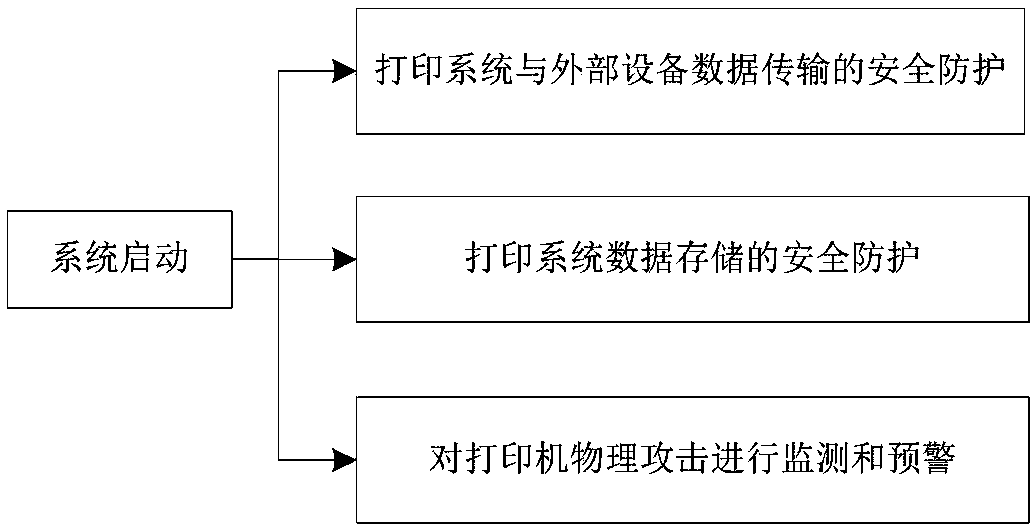
[0069] refer to figure 1 , a system that resists physical attacks on printers, including a main control module, an interface security module, a storage security module, a behavioral security module, and a security and trustworthy module. By using the hard isolation architecture of TrustZone technology, the system environment is divided into common execution environment and There are two parts of the trusted execution environment. In the common execution environment, process control functions are mainly performed, while sensitive data is processed and run in the trusted execution environment. figure 2 As shown, the general execution environment application layer includes the main control module of the printing system, and the trusted execution environment application layer includes the security and trust module, the storage security mod...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More