Distributed intrusion detection method based on federated learning and trust evaluation and system thereof
An intrusion detection system, intrusion detection technology, applied in specific environment-based services, machine learning, communication between vehicles and infrastructure, etc., can solve the problem of time-consuming training process
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
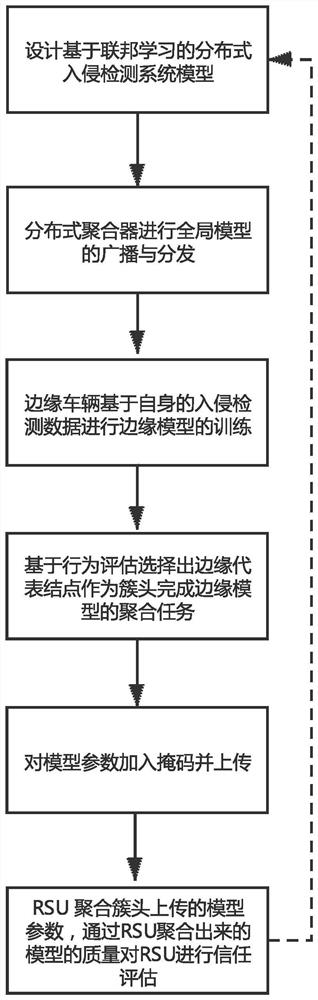
[0037] Such as figure 1 As shown in , a distributed vehicle intrusion detection method based on federated learning and trust evaluation is divided into 6 steps,
[0038] Step 1: Analyze the traditional intrusion detection system and design a distributed vehicle intrusion detection system model based on federated learning;
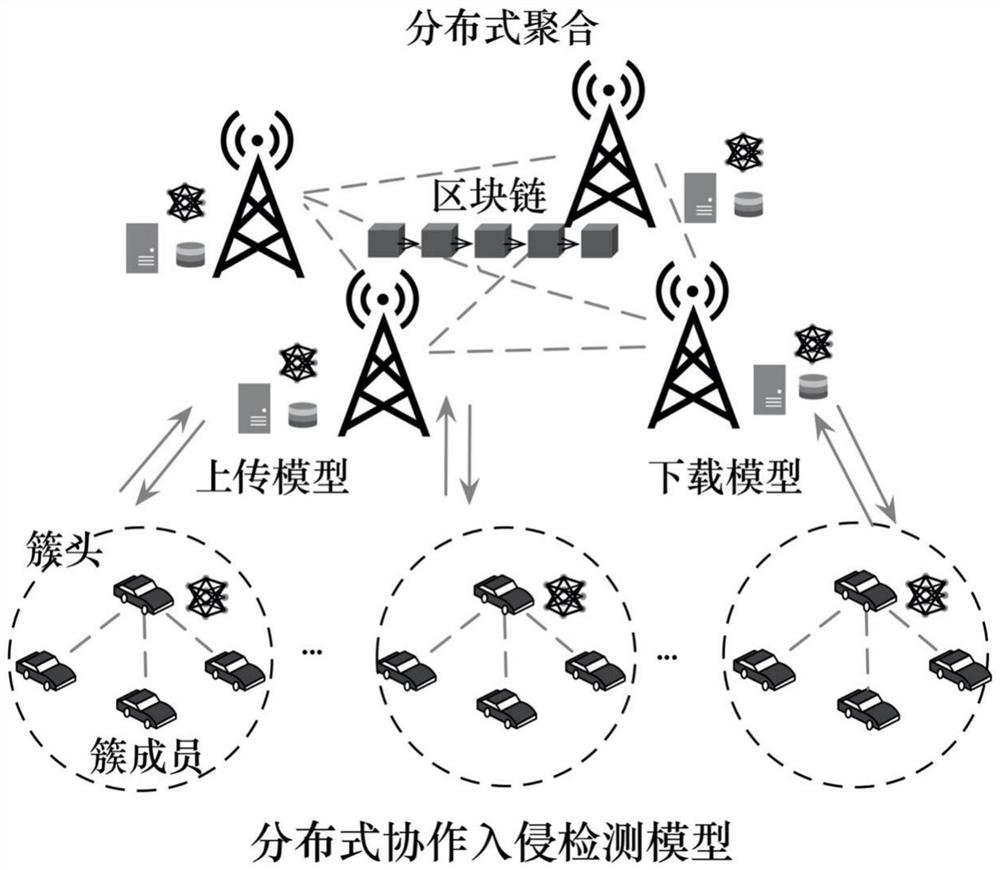
[0039] Step 2: Building and pre-training the intrusion detection model based on federated learning, and the roadside unit RSU acts as a distributed aggregation server to broadcast and distribute the global model;
[0040] Step 3: The edge vehicle performs edge model training based on the received global model and its own intrusion detection data;
[0041] Step 4: Based on the behavior evaluation, select the edge representative node as the cluster head to complete the aggregation task of the edge model.
[0042] Step 4.1: In order to complete the aggregation of edge models, each cluster needs to select a cluster head as the cluster head to aggregate the e...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More