Method for defensing transmission control protocol synchronous flooding attack and transmission control protocol agent
A technology of transmission control protocol and flooding attack, which is applied in the field of synchronous flooding attack, which can solve the problems of CPU resource occupation, affecting the establishment of normal connection, and affecting the speed of establishing normal connection, so as to achieve the effect of improving defense and speeding up
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
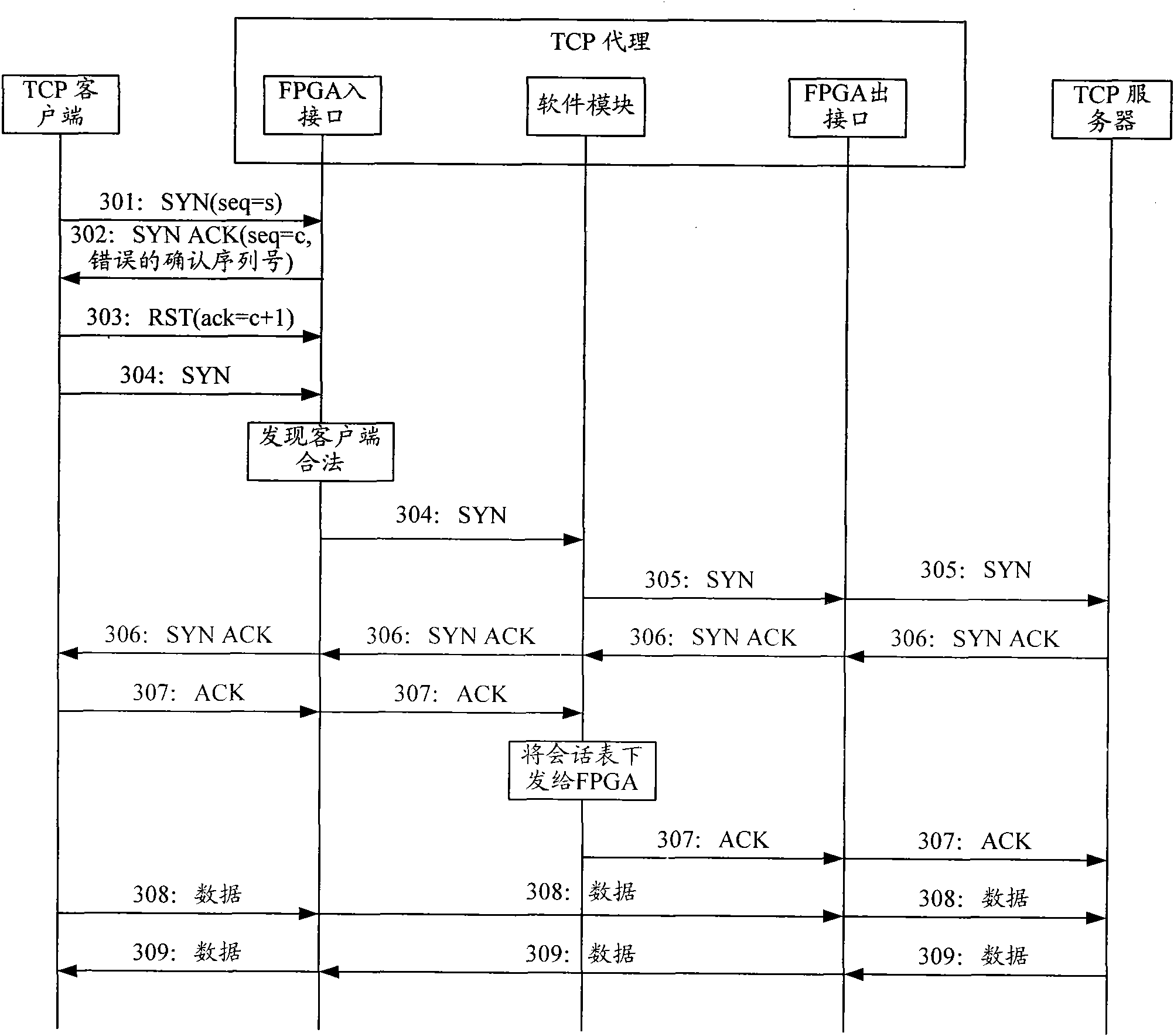
[0081] The core idea of the present invention is: because the interface of TCP agent is usually realized by FPGA, therefore, in the present invention, the legitimacy verification of client is completed by FPGA, after the legitimacy verification of client is passed, the software module of TCP agent end begins to establish client The TCP connection between the client and the server, and the session table is sent to the FPGA, and then the FPGA forwards the data message exchanged between the client and the server according to the session table.
[0082] The present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0083] image 3 In the one-way proxy mode provided by Embodiment 1 of the present invention, the message flow diagram of defending against TCP SYN Flood attacks, such as image 3 As shown, the specific steps are as follows:
[0084] Step 301: the client sends a SYN message with sequence numbe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More