Method, system and device of security certificate
A technology for security authentication and authentication request, applied in the field of security authentication, which can solve problems such as poor user experience and complex maintenance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
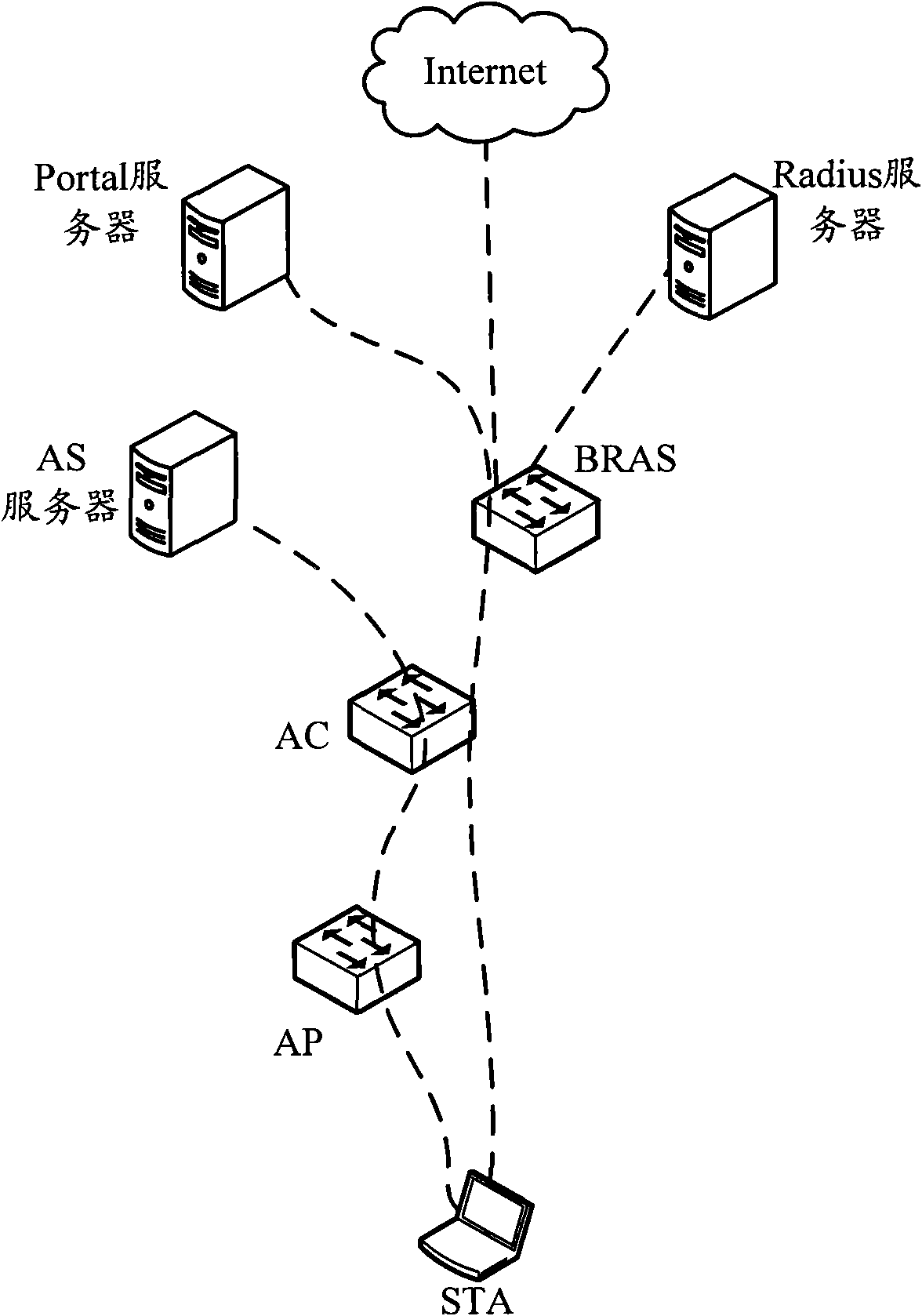
[0042] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0043] The main method provided by the present invention can be as Figure 4 As shown, it mainly includes the following steps:
[0044] Step 401: After the AC activates the air interface authentication for the STA, the AC encapsulates the air interface authentication request in a remote user dial authentication system (Radius) protocol message and sends it to the BRAS.
[0045] Step 402: The BRAS sends the Radius protocol message encapsulated with the air interface authentication request to the air interface authentication server, and sends the Radius protocol message encapsulated with the authentication result returned by the air interface authentication server to the AC.
[0046] Step 403: When the AC determines that the authentication result i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More