Entity Authentication Method Based on Secret Sharing Encryption
An authentication method and secret sharing technology, applied in the field of entity authentication scheme, can solve the problem that the security requirements of cluster heads are relatively high, and achieve the effect of preventing impersonation attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] Below in conjunction with example the present invention will be further described:
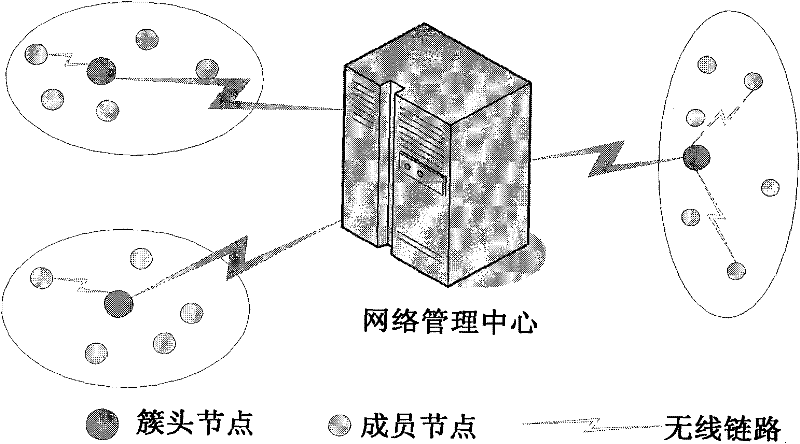
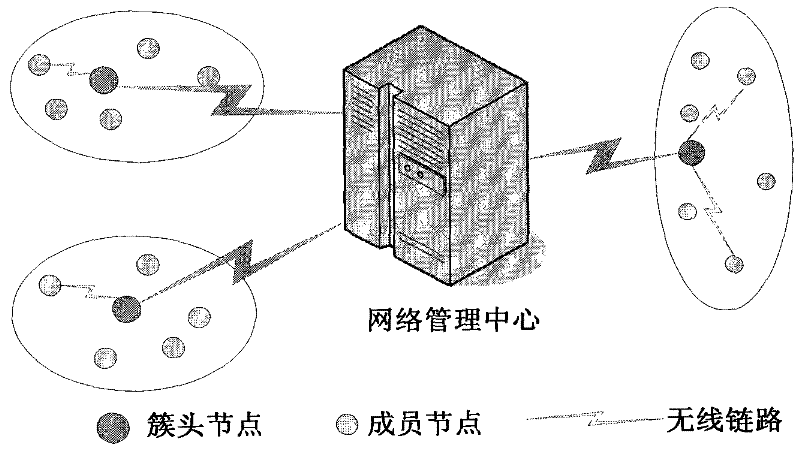
[0038] 1) Network clustering
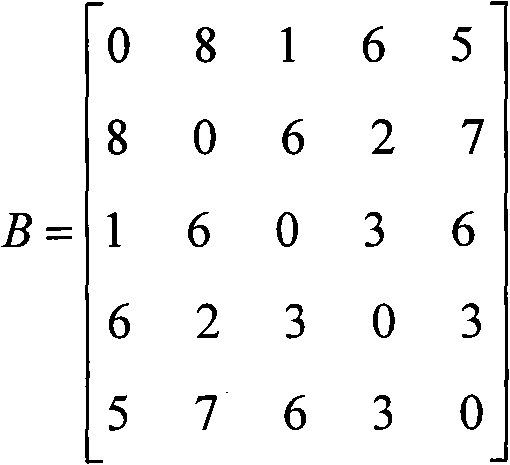
[0039] Assuming that there are 5 nodes in a certain cluster of self-organizing network, the distance relationship between them can be expressed by matrix B.
[0040] B = 0 8 1 6 5 8 0 6 2 7 1 6 0 3 6 6 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More