DICOM (Digital Imaging and Communications in Medicine) medical image encrypting and decrypting method based on edge detection
An edge detection and medical image technology, applied in the field of image processing, can solve the problems of slow calculation speed, good confidentiality, loss of image information, etc., and achieve the effect of reducing the amount of encrypted data, reducing the amount of calculation, and improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0046] The plaintext image GM of the present embodiment is a skull image with a size of 256×256 from the collection of CASIMAGE DICOM sample graphics files, such as image 3 shown.
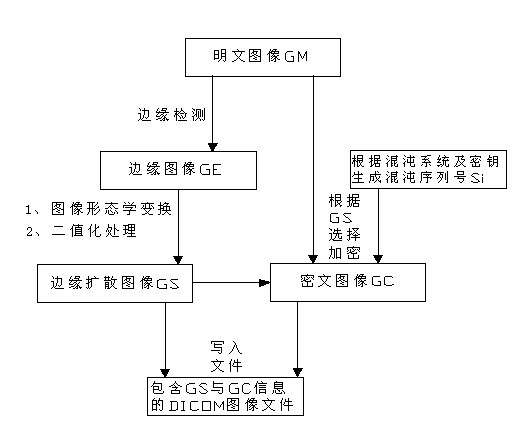
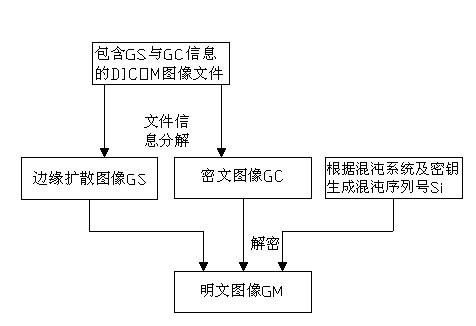
[0047] like figure 1 Shown: a kind of DICOM medical image encryption and decryption method based on edge detection comprises encryption process and decryption process, and described encryption process is carried out in the following steps:
[0048] step one, yes image 3 Perform edge detection on the plaintext image GM shown, and obtain the edge image GE of the plaintext image GM, such as Figure 4 shown;
[0049] The edge detection method adopted is: Convolve the image with a 3*3 Laplace convolution kernel.
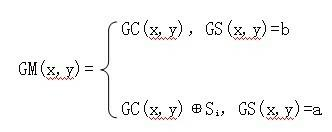
[0050] Step 2, using image morphological transformation to diffuse the edge in the edge image GE, and binarize the diffused image to obtain the edge diffusion image GS, the pixel value of the edge part of the edge diffusion image GS is a , and the rest of the pixel values are b;
[0...
Embodiment 2
[0084] The plaintext image GM of the present embodiment is also a skull image with a size of 256×256 selected from the CASIMAGE DICOM sample graphics file collection, such as Figure 11 shown.
[0085] This embodiment is roughly the same as Embodiment 1, except that the adopted edge detection method is: use a square filter Sobel operator with a width of 3 to perform a first-order derivation on each of the horizontal and vertical axes; the adopted The image morphological transformation method is as follows: a 3*3 rectangular kernel with a reference point at the center performs an iterative expansion operation.
[0086] The plaintext image GM, edge image GE, edge diffusion image GS, and ciphertext image GC in the encryption process of this embodiment are as follows: Figure 11 , 12 , 13, and 14; the ciphertext image GC, edge diffusion image GS, and plaintext image GM in the decryption process are shown as Figure 15 , 16 , 17 shown. The key used in this embodiment is a=0.66...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More