Circuit security testable design method capable of detecting inactive hardware Trojan horse and detecting method of hardware Trojan horse
A hardware Trojan horse and design method technology, applied in computer security devices, computing, electrical digital data processing and other directions, can solve problems such as difficult detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
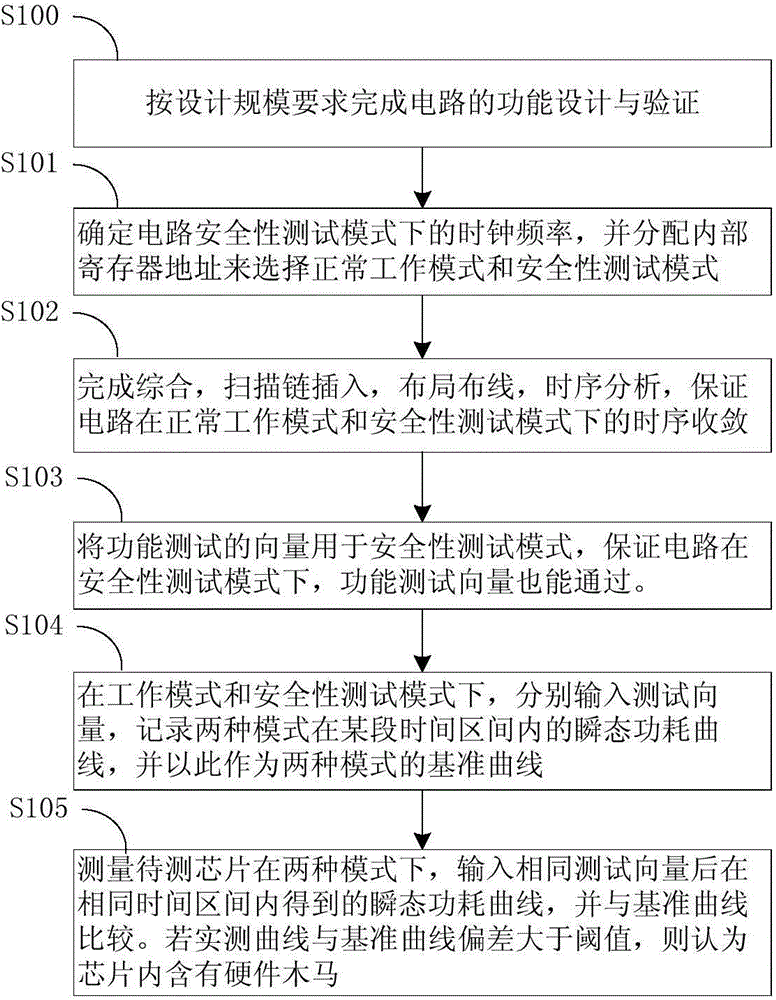
Method used
Image
Examples
Embodiment Construction
[0025] The present invention will be further described below in conjunction with specific drawings and embodiments.
[0026] Design for Testability (DFT, Design for Testability) is a very important part of integrated circuit design. It is mainly used to detect whether there are manufacturing defects in the chip during the manufacturing process, which affects the function of the circuit and the yield. And people have developed a variety of DFT techniques to more effectively detect defects in chip manufacturing. However, for the security detection of whether there is a hardware Trojan in the integrated circuit, there is no general and standard process such as DFT at present. Moreover, current technologies for hardware Trojan detection, such as logic testing and bypass analysis and detection, all rely on such a prerequisite, that is, the hardware Trojan in the circuit is triggered or is in a working state. However, there is a type of hardware Trojan that does not affect the func...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More