A hardware Trojan real-time detection system and its design method
A technology for real-time detection of hardware Trojan horses, applied in computing, computer components, instruments, etc., can solve problems such as difficult detection of Trojan horses, achieve the effect of improving data transmission rate and efficiency, and improving hardware resource utilization
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be further described in detail below in conjunction with the accompanying drawings. Obviously, for those skilled in the art, other legends can be obtained according to these drawings without creative effort.
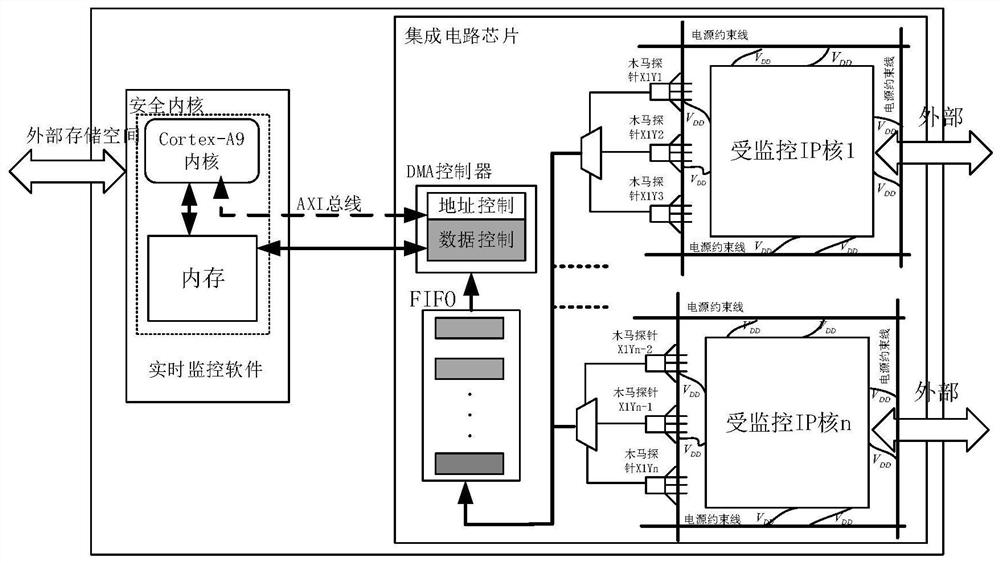
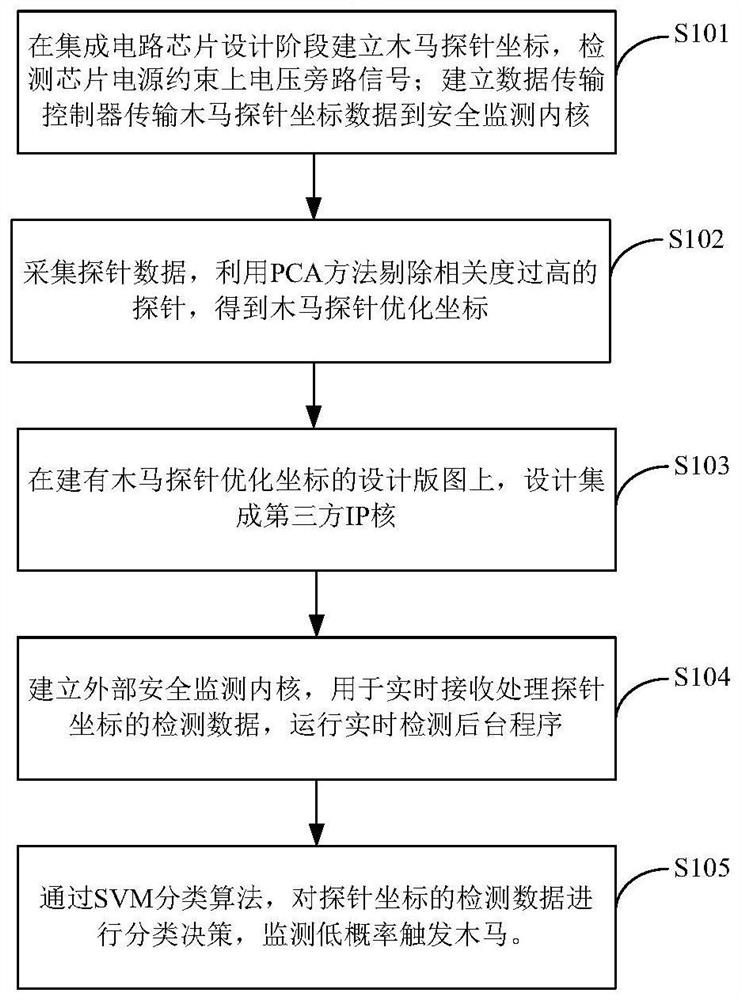
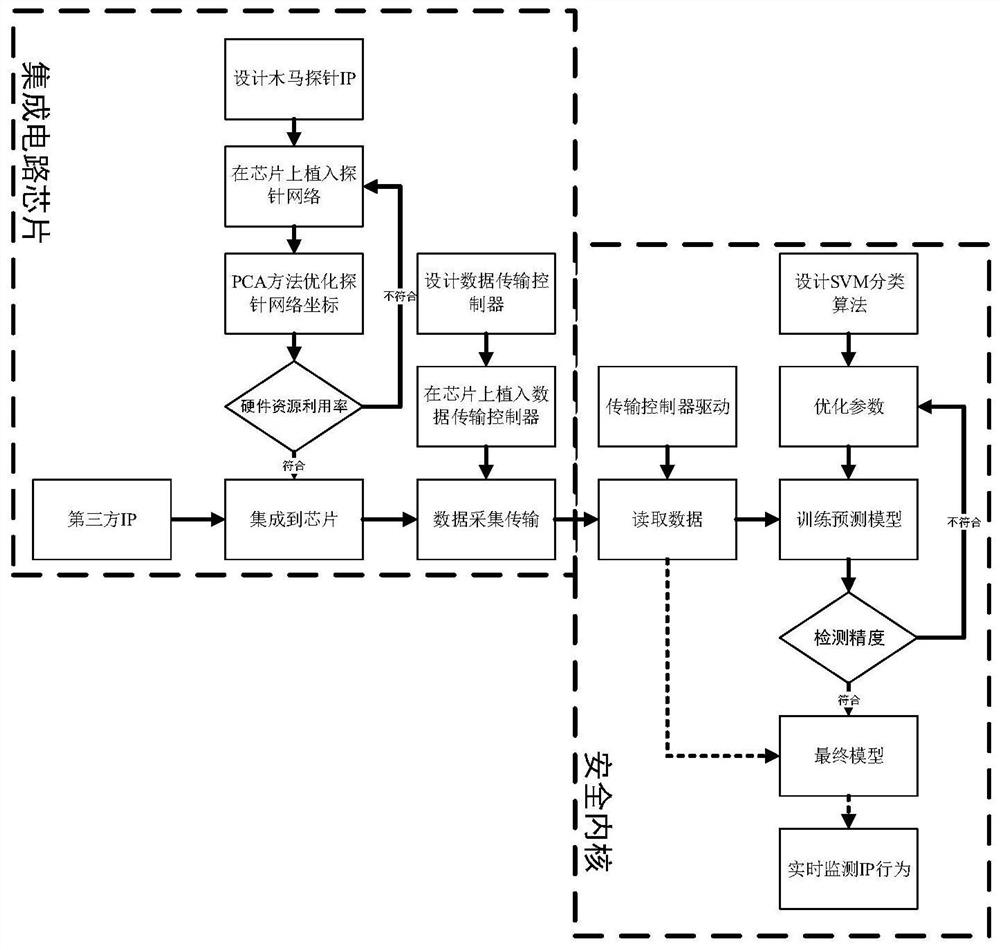
[0026] Such as figure 1 As shown, the hardware Trojan real-time detection system provided by the present invention mainly includes three parts: a Trojan probe, a data transmission controller and a security monitoring kernel. The security monitoring kernel is also referred to as the security kernel in the accompanying drawings and the following description.
[0027] In the design stage of the integrated circuit chip, a certain number of Trojan horse probes are arranged on the layout of the integrated circuit chip to ensure that the power constraint lines in each area of the chip can be covered. The Trojan horse probes implanted...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More