Distributed trusted identity authentication method and system, storage medium and terminal
An identity authentication and distributed technology, applied in user identity/authority verification, transmission system, digital transmission system, etc., can solve problems such as single point failure, attack, interception, etc., to ensure security and consistency, and avoid time overhead , the effect of reducing time overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
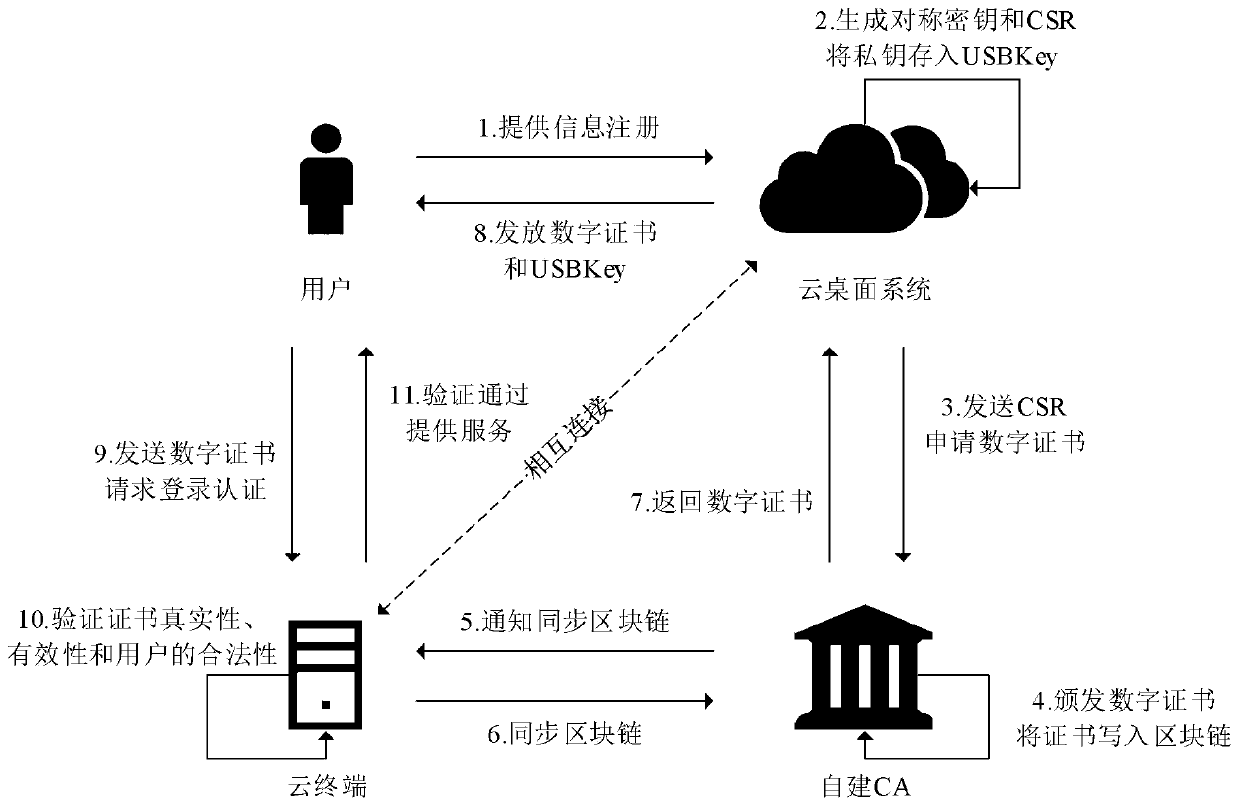
[0062] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0063] Aiming at the problems existing in the prior art, the present invention provides a distributed trusted identity authentication method, system, storage medium, and terminal. The present invention will be described in detail below in conjunction with the accompanying drawings.
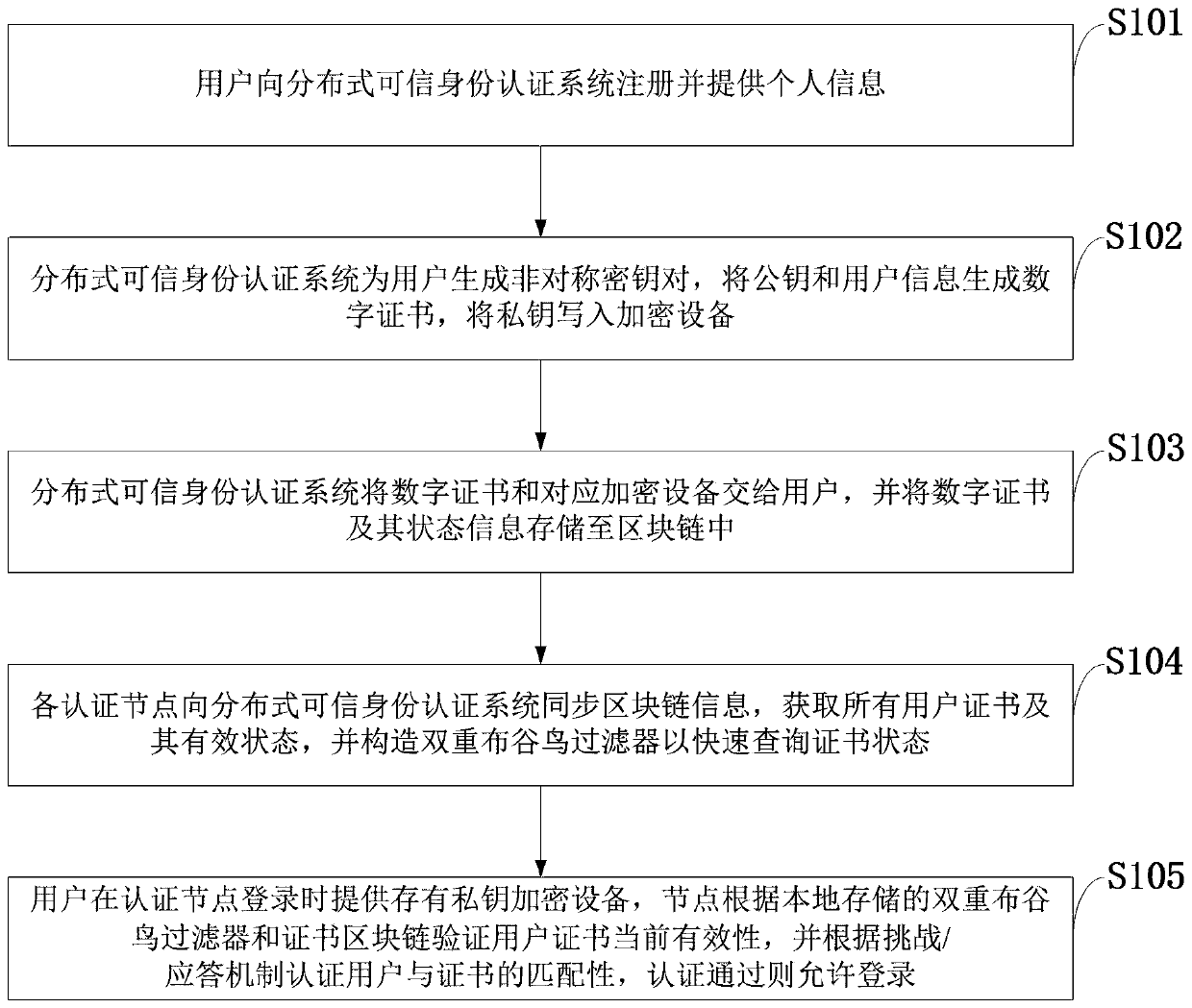
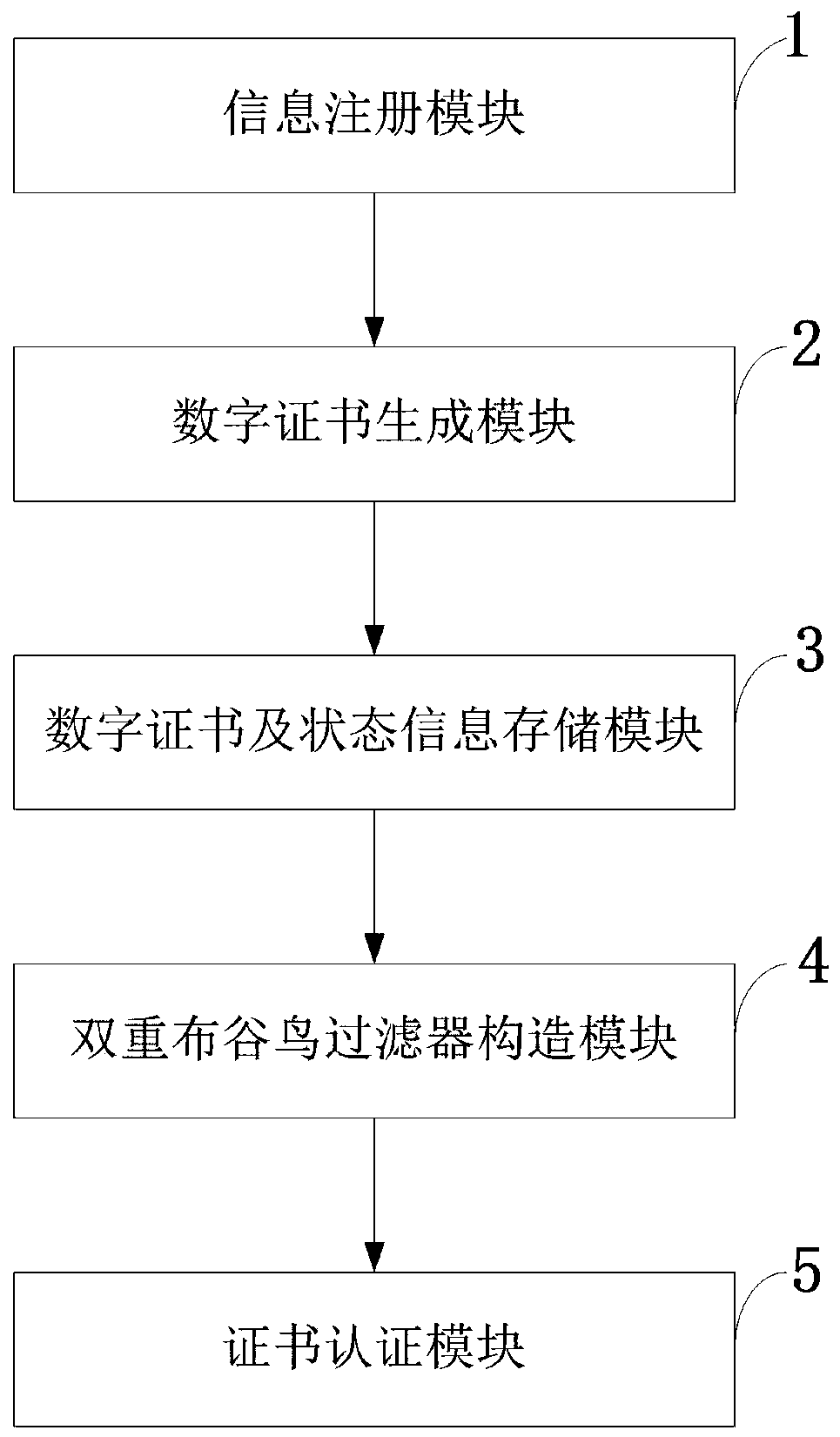
[0064] Such as figure 1 As shown, the distributed trusted identity authentication method provided by the present invention includes the following steps:
[0065] S101: The user registers with the distributed trusted identity authentication system and provides personal information;
[0066] S102: The distributed trusted identity authentication...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com