Network attack processing method and device, computer equipment and storage medium
A technology of network attack and processing method, applied in the field of network attack processing method, computer equipment and storage medium, and device, to achieve the effect of being beneficial to network security maintenance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
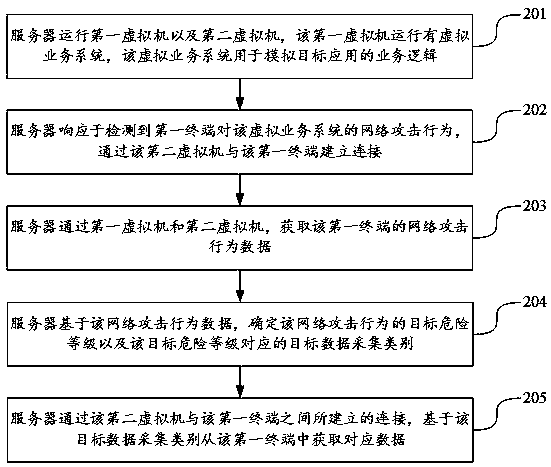
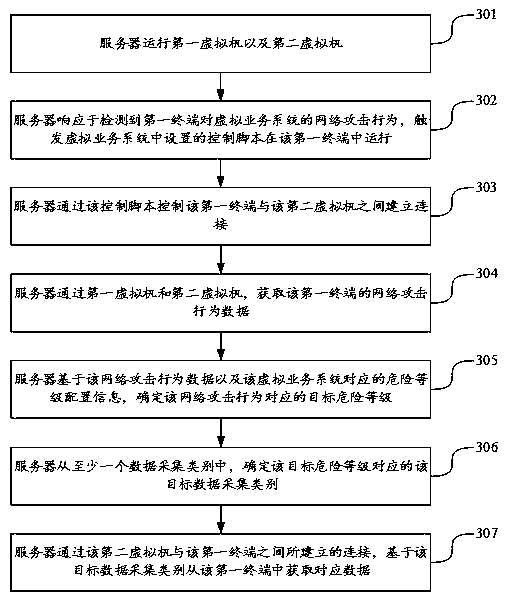
[0052]In order to make the purpose, technical solutions and advantages of the application clearer, the following will further describe the implementation of the application in detail with reference to the accompanying drawings. Obviously, the described embodiments are part of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0053] In this application, the terms "first" and "second" are used to distinguish the same or similar items with basically the same function and function. It should be understood that "first", "second" and "nth" There are no logical or timing dependencies, nor are there restrictions on quantity or order of execution.
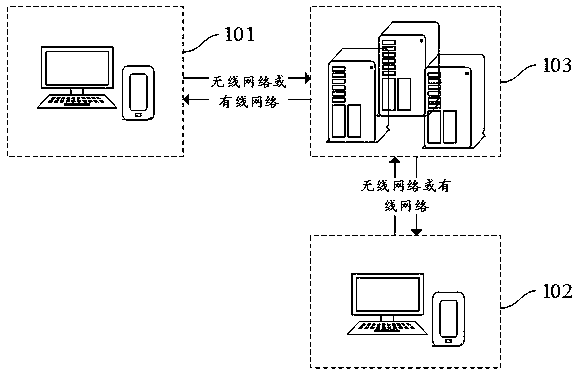
[0054] Cloud technology (Cloud technology) is a general term for network technology, information technology, integration technology, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More