Authentication information processing method, terminal and network equipment
An information processing method and technology of network equipment, applied in the field of authentication information processing method, terminal and network equipment, can solve the problems of inaccessibility of attackers, correlation attack, consumption of large computing resources, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
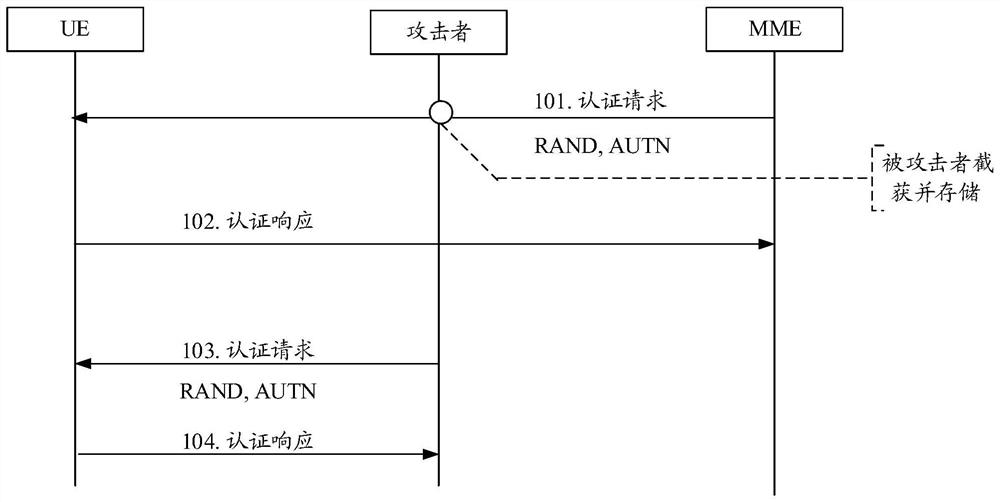
[0076] Before elaborating the authentication information processing method of the embodiment of the present invention in detail, a brief introduction to correlation attacks is given first.
[0077] figure 1 It is a schematic diagram of the flow of correlation attacks in related technologies; figure 1 A 4G network (such as an LTE network) is taken as an example for illustration. Such as figure 1 shown, including:
[0078] Step 101: a Mobility Management Entity (MME, Mobility Management Entity) sends an authentication request message to the UE, and the authentication request message includes a random challenge (RAND, Random challenge) and an authentication token (AUTN). In this step, the attacker may intercept the authentication request message, obtain and store the random challenge (RAND) and authentication token (AUTN) in the authentication request message.
[0079]Step 102: the UE performs network authentication, and after the network authentication is completed, the UE s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More