Circuits and methods for modular exponentiation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
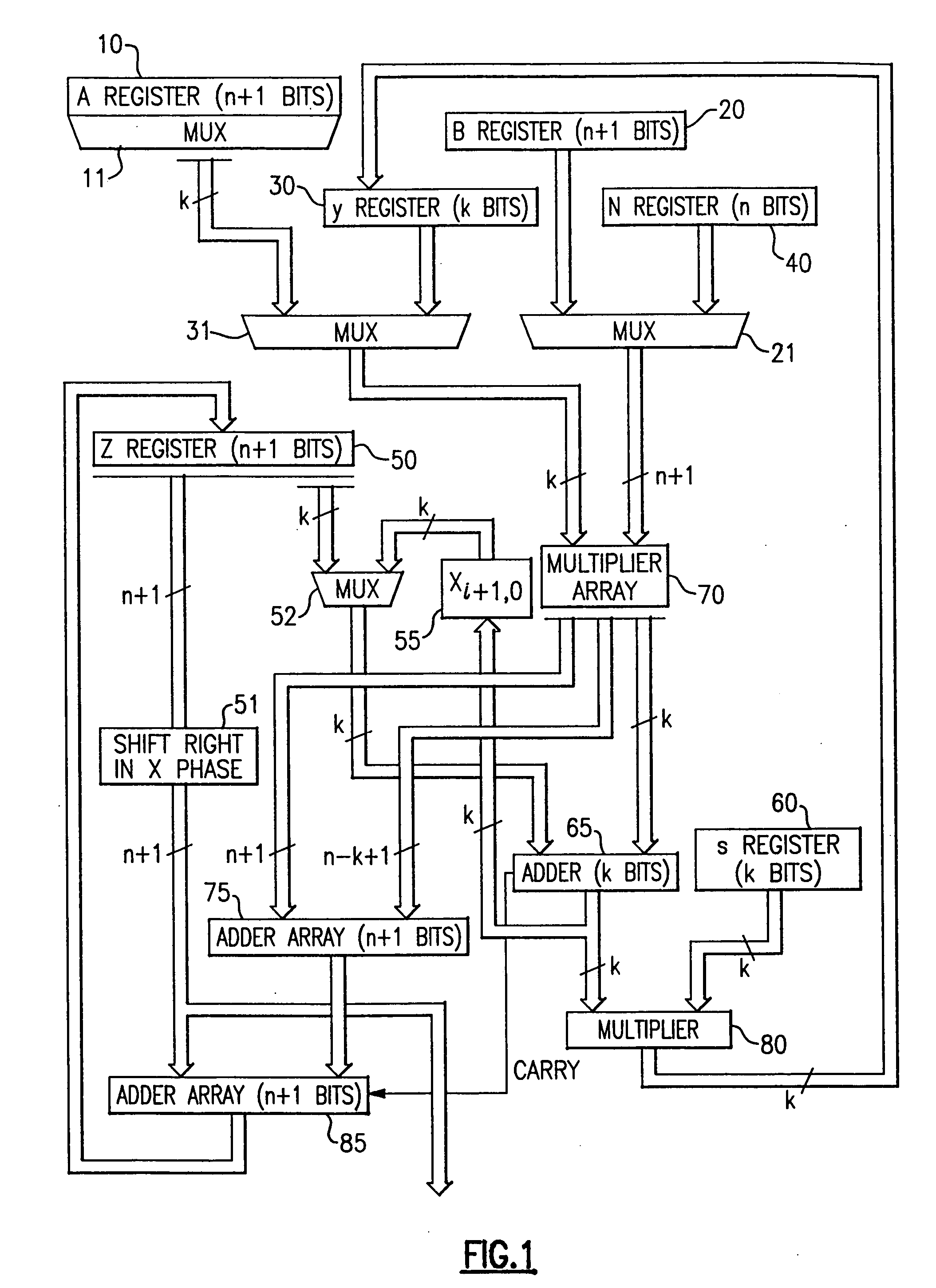
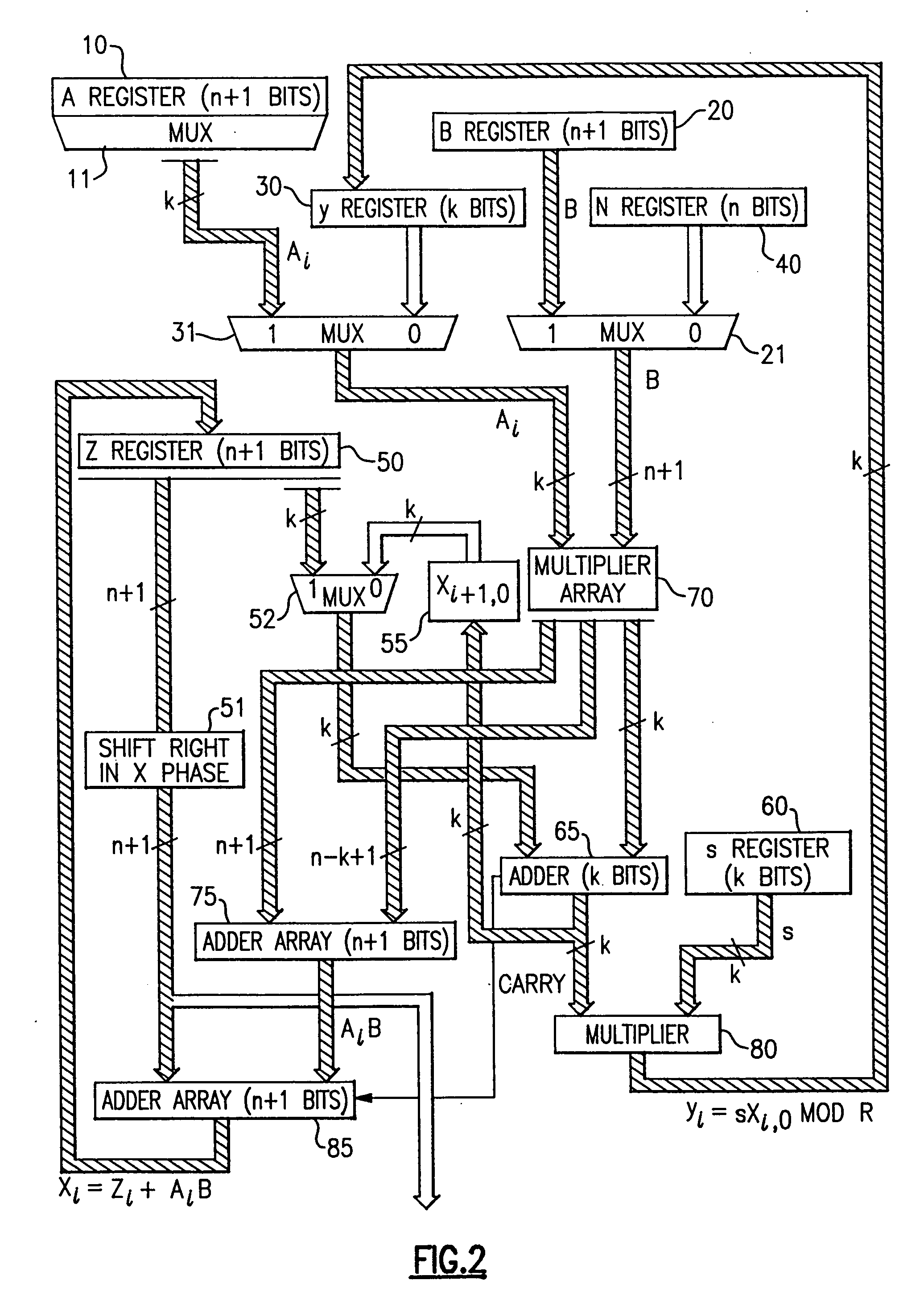
[0083] The structure and operation of the present invention is dependent upon the partitioning of one of the multiplying factors into a plurality of k bit-wide pieces. Thus, instead of representing a binary number A as ∑i=0n-1ai2i,
one of the multiplying factors in the present invention is represented instead in the form Am-1Rm-1+…+A2R2+A1R+A0=∑j=0m-1AjRi ,
where R=2k. In this representation, the number A is represented in block form where each of the m blocks includes k bits. That is, each Ai represents an integer having k bits.
[0084] In the present system, multiplication modulo an odd number N is a significant object. Also, for purposes of understanding the present invention, the symbol n is used to denote the number of bits in the binary representation for N. Also, for present purposes, it is assumed that the number A, as stored in Register A (reference numeral 10 in FIG. 1), is the number that is partitioned into m blocks. In general, the number of blocks m is selecte...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More