Nonlinear transformation method for symmetric key encryption and implementation method thereof
A technology of symmetric key encryption and nonlinear transformation, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The present invention will be further described below in conjunction with specific examples.
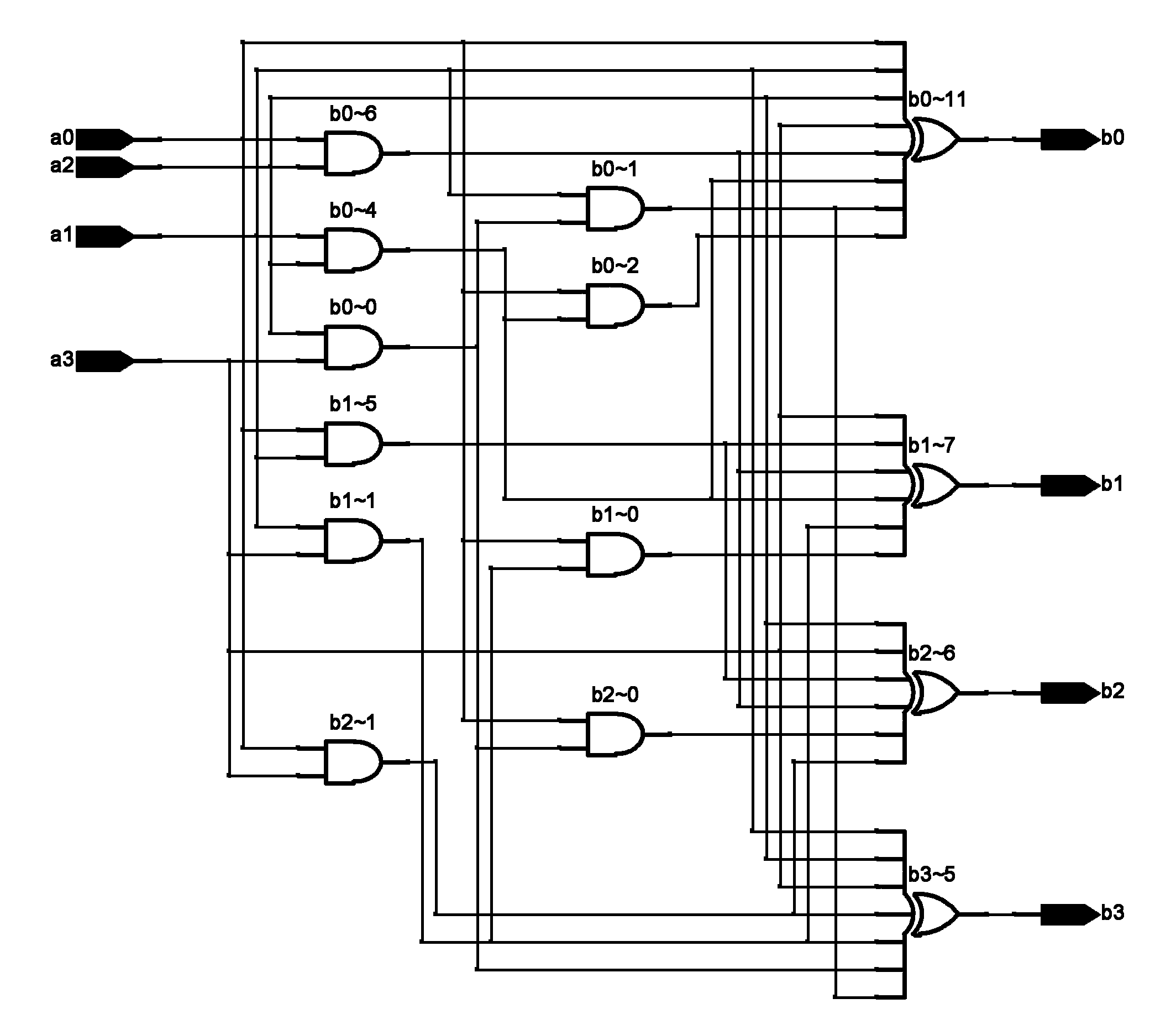
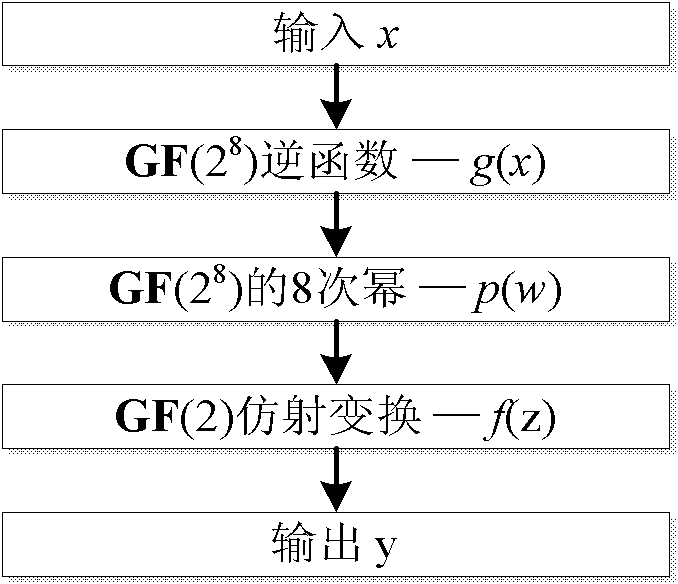
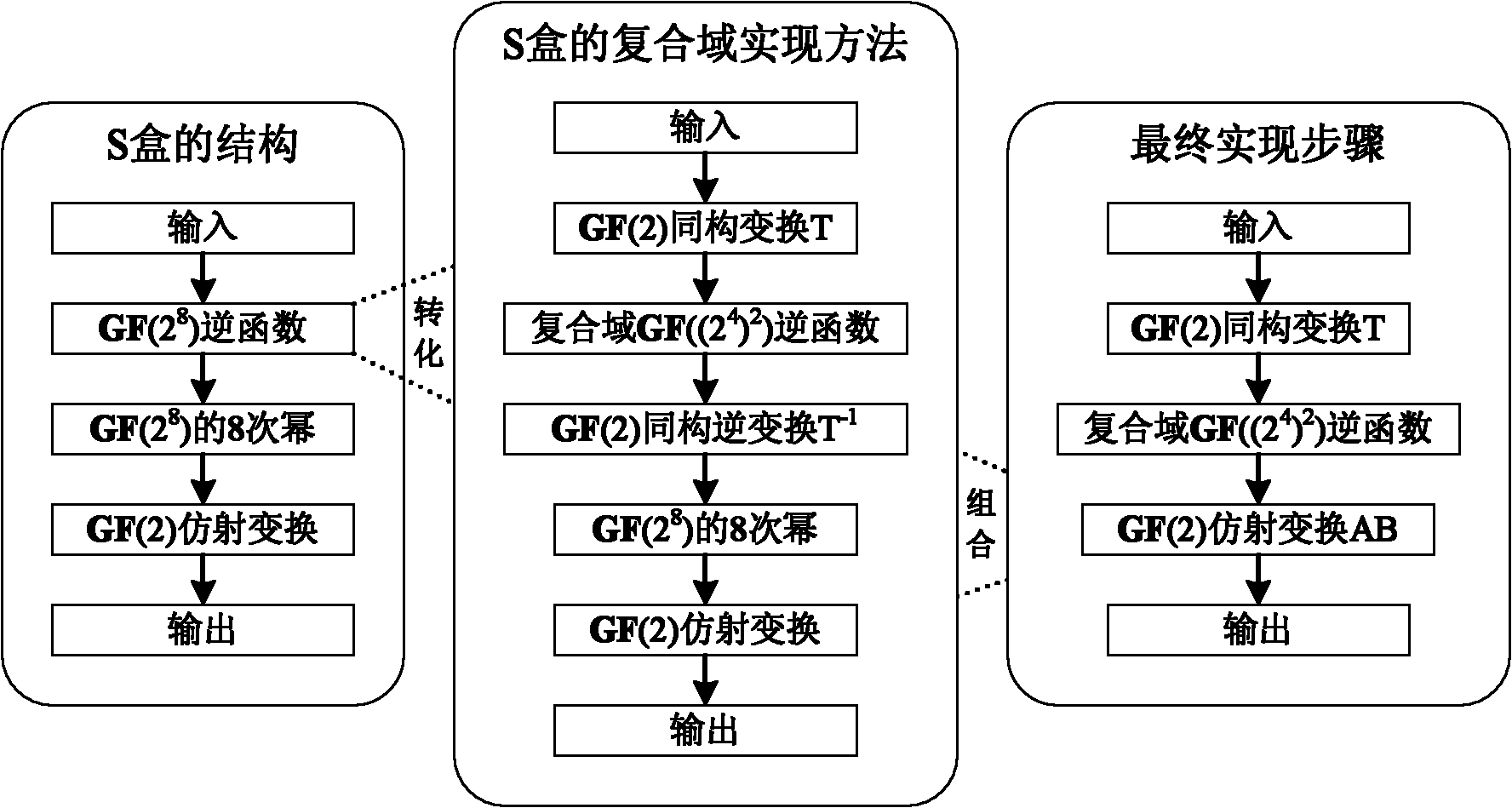
[0039] The hardware implementation of the S-box provided by the present invention can use the composite domain method, its algebraic structure, and the hardware implementation adopts the relationship between the computing structure of the composite domain method and the simplified computing structure such as figure 2 As shown, according to the simplified structure, image 3 The overall design drawing is given, which can be divided into the following three parts:
[0040] 1. Perform a linear transformation T on the input 8-bit data, and its matrix form is:
[0041] T · x = 0 0 1 0 0 0 0 ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More