Credible data access control method applied to cloud storage of mobile devices
A mobile device, access control technology, applied in the field of cloud computing security, can solve problems such as difficulty in finding k for P and Q
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
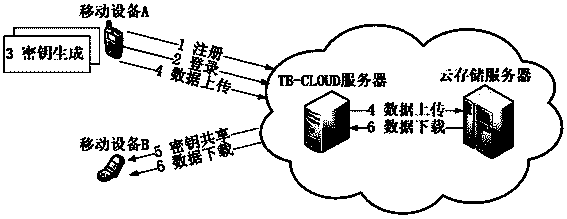
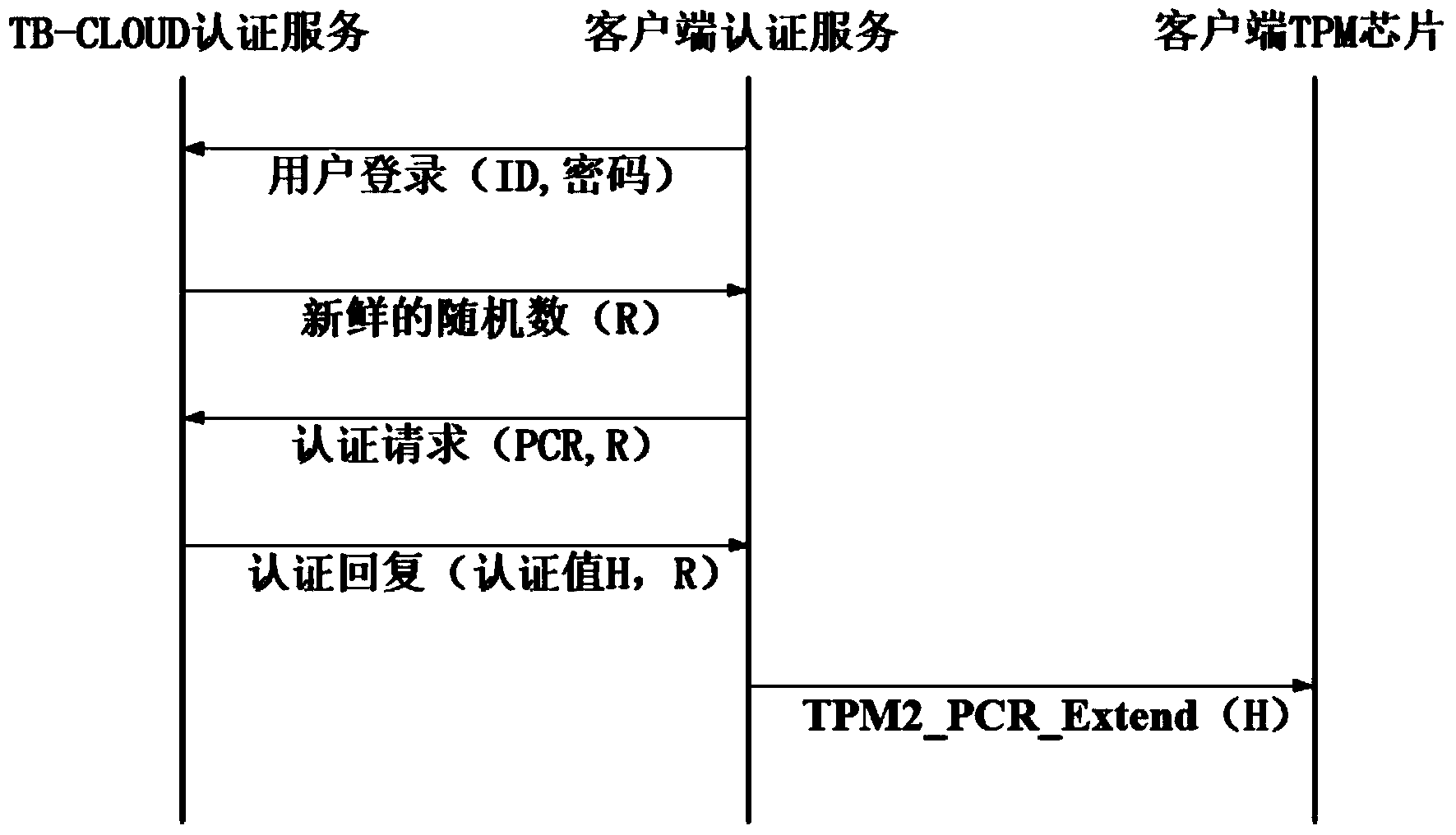
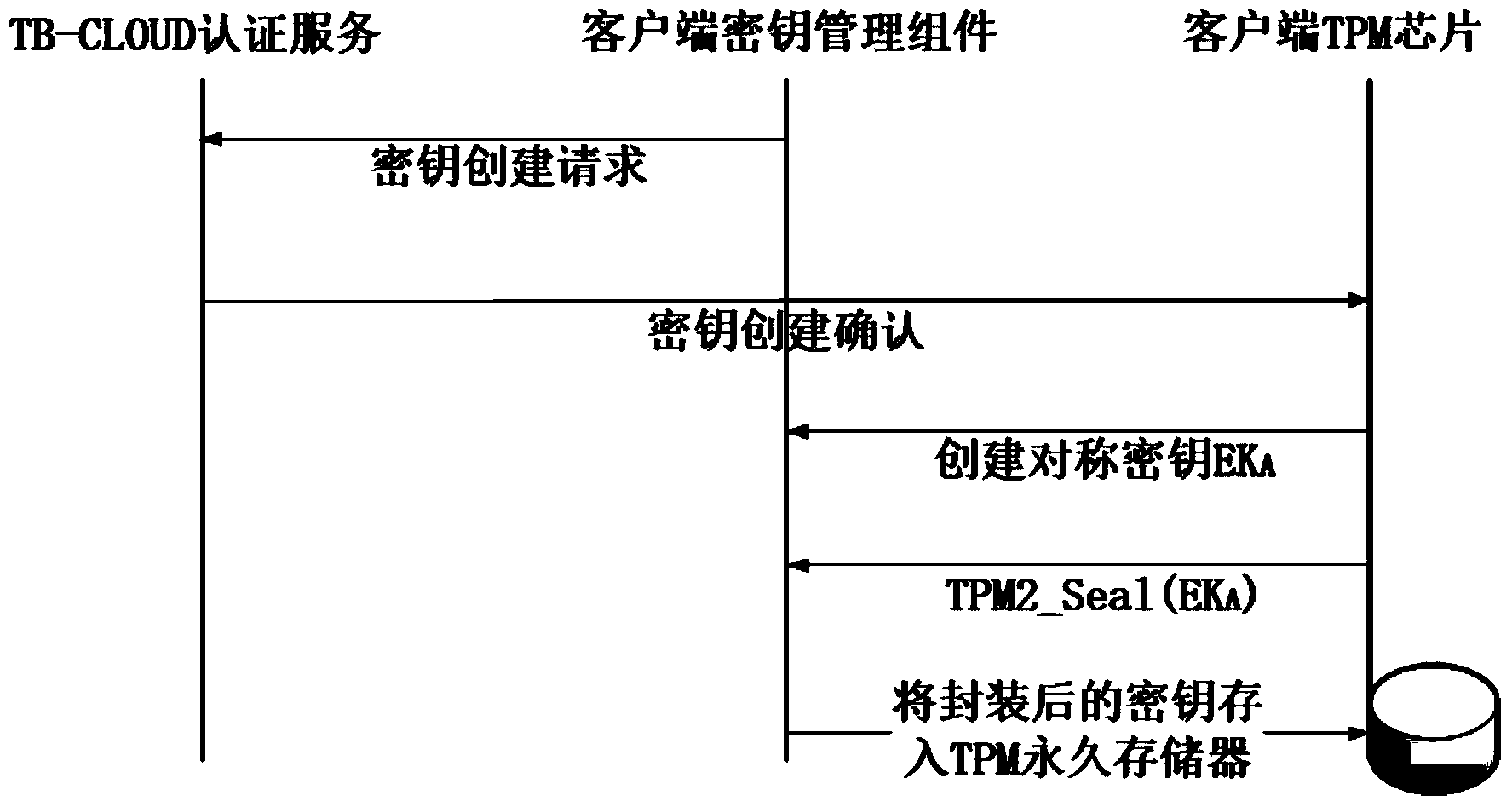
[0040] The trusted access control method will be described in detail below in conjunction with the accompanying drawings, figure 1 It is a flow chart of the present invention; figure 2 For login with authentication process; image 3 Create a protocol flow diagram for the key; Figure 4 Flowchart for sharing keys for multiple mobile devices.
[0041] Main symbols and algorithm explanations:
[0042] (1) The value stored in the PCR represents the measurement value of the current system, and a fixed-length value is obtained by a hash algorithm in the TPM, that is, the PCR n =Hash(PCR n-1 ||Measurement n )Calculated;
[0043] (2) The random number R represents a fresh randomly generated number, which can ensure that each session is fresh;
[0044] (3)EK A Represents a symmetric encryption and decryption key, used to encrypt or decrypt user data stored in the cloud;
[0045] (4)K B Represents the public key of mobile device B, which is used to encrypt the symmetric data ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More