Data processing method
A data processing and data technology, which is applied in the field of network information security, can solve the problems of confidential data hacking and other problems, and achieve the effect of preventing man-in-the-middle attacks, ensuring security, and preventing counterfeit attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] In order to more clearly illustrate the technical solutions in the embodiments of the present invention or the prior art, the following will briefly introduce the drawings that need to be used in the description of the embodiments or the prior art. Obviously, the accompanying drawings in the following description are only These are some embodiments of the present invention. Those skilled in the art can also obtain other drawings based on these drawings without creative work.
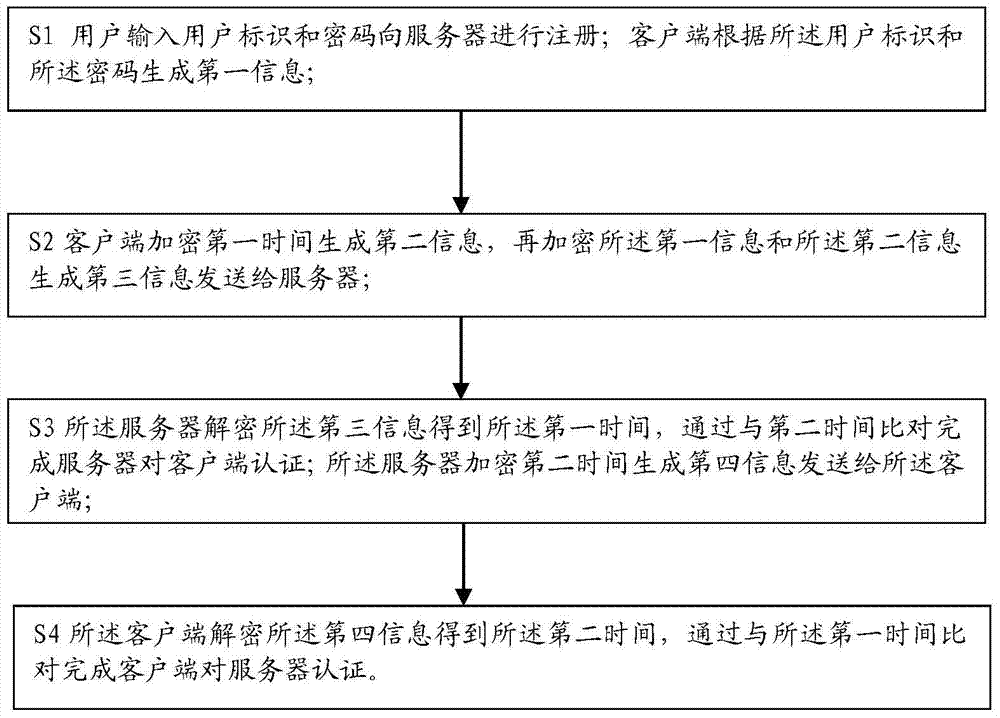
[0046] As a specific embodiment of the present invention, figure 1 It is a schematic diagram of the steps of the embodiment of the data processing method provided by the present invention. The invention provides a data processing method, comprising the steps of:
[0047] S1 The user enters the user ID and password to register with the server; the client generates first information according to the user ID and the password;
[0048] S2 The client encrypts the first time to generate second informa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More