Efficient privacy protecting audit scheme based on chameleon hash function of cloud storage
A technology of privacy protection and auditing scheme, which is applied in the field of cloud storage and information security, can solve problems such as inappropriate integrity auditing, and achieve the effect of solving a large amount of calculation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
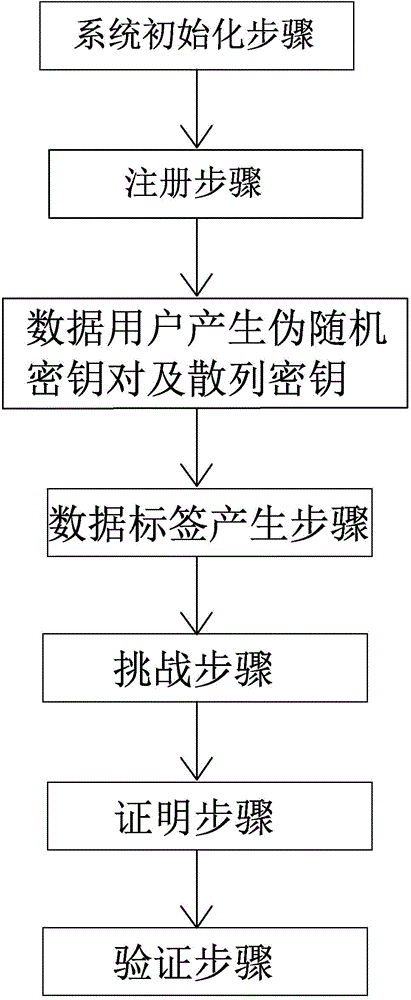
[0058] as attached figure 1 As shown, the efficient privacy protection audit scheme based on chameleon hash in the cloud storage of the present invention comprises the following steps:
[0059] (1) System initialization steps:
[0060] Public system parameter Param=(G 1 ,G 2 ,G T ,e,Φ,g 1 , g 2 ,h,Y CA ,h 1 , u 1 ,...,u t );
[0061] (2) Registration steps:
[0062] The data user generates a public-private key pair and registers with the CA, and the CA generates a public key certificate;
[0063] (3) Data users generate pseudo-random key pairs and hash keys;
[0064] (4) Data label generation steps:
[0065] The data user blocks and encrypts the data file, and then uses his own pseudo-random key pair to generate the data label t i , and then label the generated data t i , The encrypted data block is uploaded to the cloud storage server;
[0066] (5) Challenge steps:
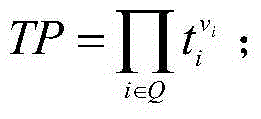
[0067] When the data user needs to check the integrity of the data file, the relevant informa...
Embodiment 2
[0073] Such as figure 1 Shown, except following difference, all the other are identical with embodiment 1:
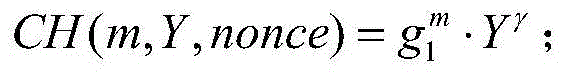
[0074] The calculation method of the hash value H is in the cyclic group G 1 Calculate on
[0075] In step (1), (G 1 ,G 2 ,G T ) is a three-order large prime number p>2 k The multiplicative cyclic group of , where k is a given security parameter, g 1 , g 2 G respectively 1 ,G 2 Generator; bilinear map e:G 1 ×G 2 →G T ;Group G 2 to group G 1 The homomorphism Φ; the collision-free hash function h:{0,1} * →G 1 ; h 1 () is a one-way encrypted hash function; the certificate center CA randomly selects a public-private key pair Select t random numbers x at the same time 1 ,x 2 ,...,x t ∈ Z p ,calculate The data user chooses a secure signature algorithm Sign, and finally discloses the system parameters
[0076] Param=(G 1 ,G 2 ,G T ,e,Φ,g 1 , g 2 ,h,Y CA ,h 1 , u 1 ,...,u t );
[0077] In step (2), the data user randomly selects S ID ∈ Z P...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More