Method for mutual authentication of user identities based on elliptic curve passwords
An elliptic curve and user identity technology, which is applied in the field of security and privacy protection in wireless communication, can solve problems such as loss of system security, and achieve the effect of accelerating authentication speed, reducing communication overhead and calculation overhead, and reducing the number of verifications
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] The present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments.
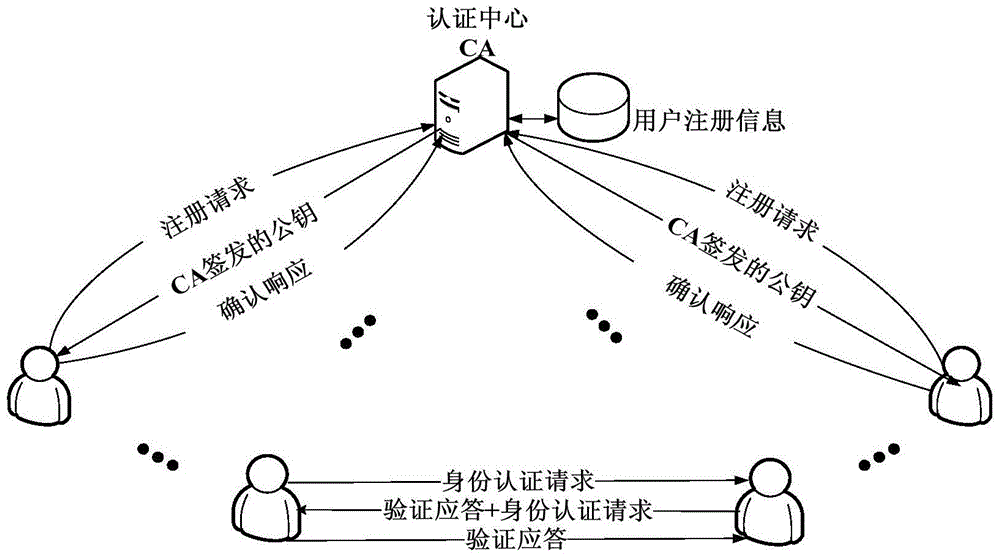
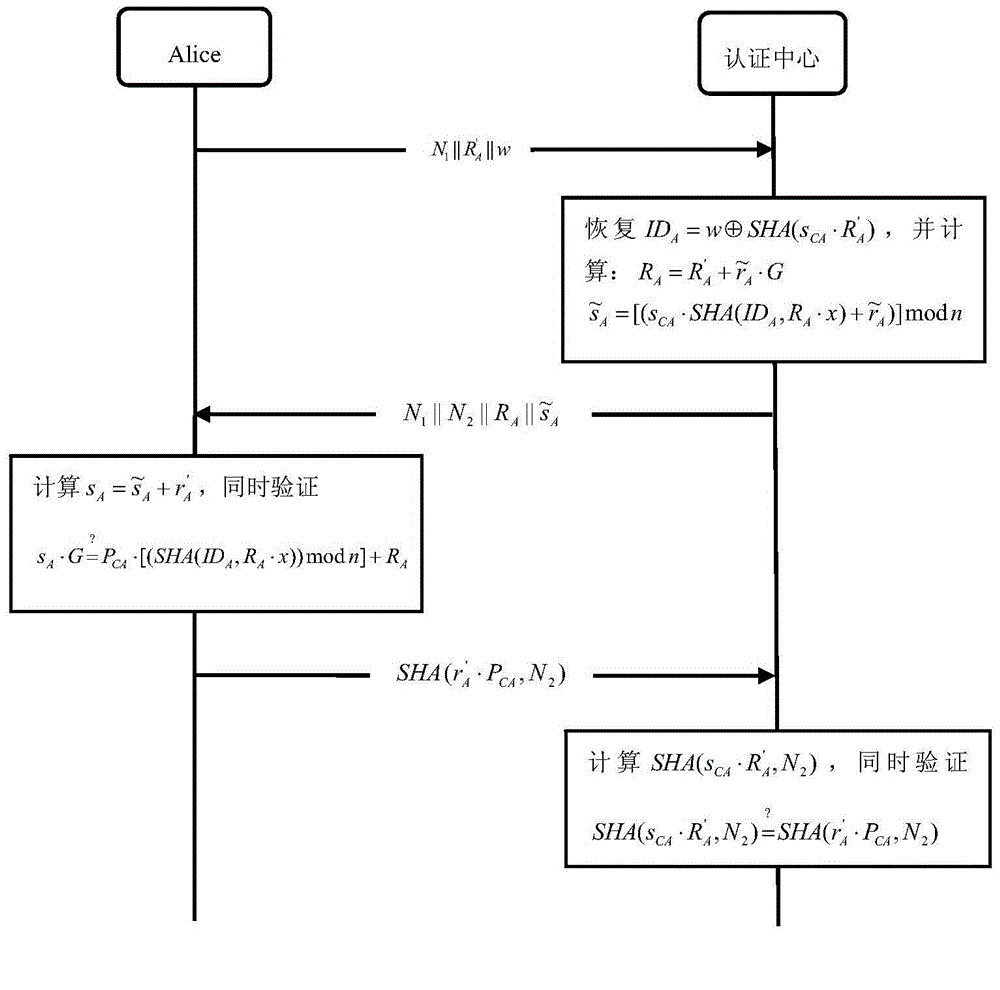
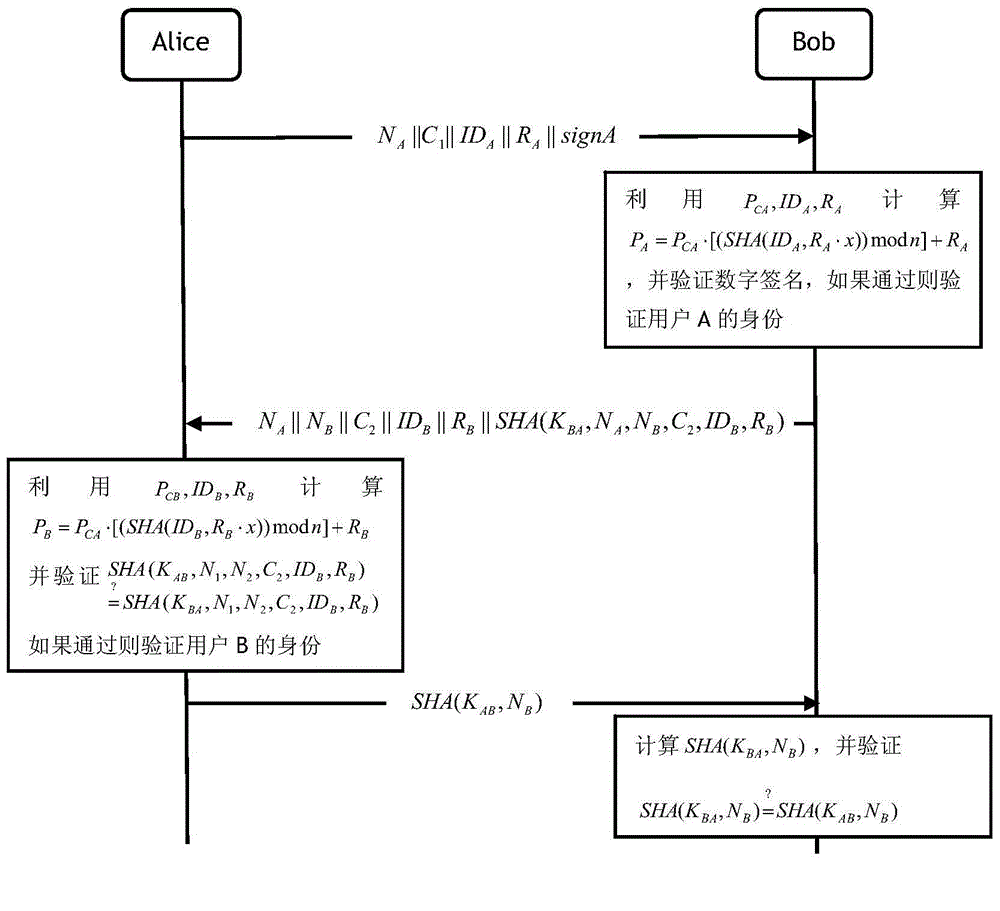
[0047] The method of the present invention includes system initialization, user registration stage and user identity mutual authentication stage, such as figure 1 shown.
[0048] This example is implemented through the following steps:
[0049] Step 1. System initialization. First, the CA (certification center) selects a 160-bit elliptic curve E(GF(p)) based on the prime number field GF(p) recommended by the SEC 2 standard. The elliptic curve equation is:
[0050] the y 2 =x 3 +ax+b(modp), a, b∈GF(p), and (4a 3 +27b 2 )modp≠0
[0051] Elliptic curve domain parameter is T=(p,a,b,G,n,h), CA randomly selects an integer s CA as its private key, and s CA ∈[2,n-2], by calculating P CA =s CA G obtains its public key;
[0052] Step 2, user registration phase, first users Alice and Bob generate their public / private key pair s by registering ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More