JPEG image encryption method compatible in format and invariant in size
A technology compatible with formats and encryption methods, applied in the field of JPEG image encryption, can solve the problems of increasing the size of ciphertext images, destroying statistical correlation, and increasing ciphertext images, achieving good format compatibility, good resistance to brute force attacks, The effect of low computational burden
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0058] The specific implementation of the present invention will be further described below in conjunction with the accompanying drawings and examples, but the implementation and protection of the present invention are not limited thereto.
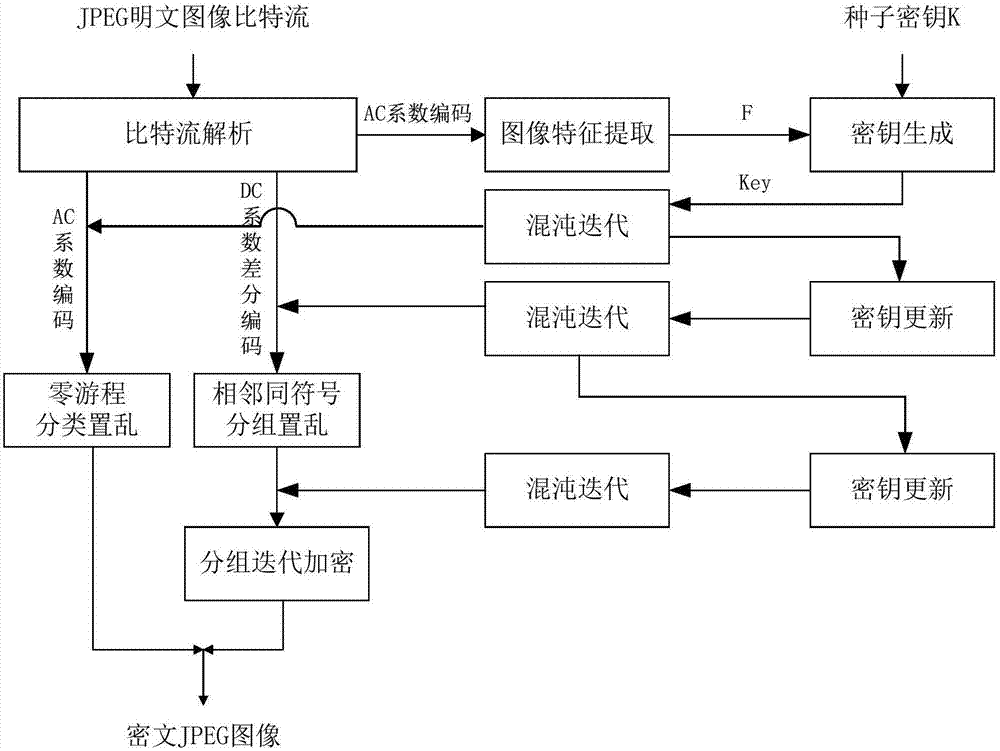
[0059] This example provides a JPEG image encryption method with compatible format and invariant size, see figure 1 , the present invention includes the following steps.
[0060] Step 1: Input the JPEG image to be encrypted, and read the quantization table, Huffman table and DCT coefficient coded bit stream.
[0061] For a JPEG image file, it contains several segments, such as a quantization table segment, a Huffman table segment, and a DCT coefficient coding segment, and the corresponding information can be read out from the corresponding segment.
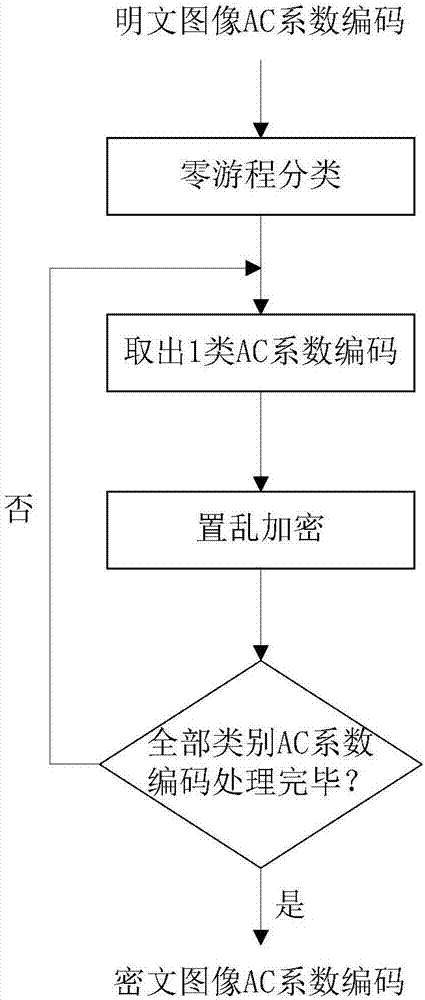
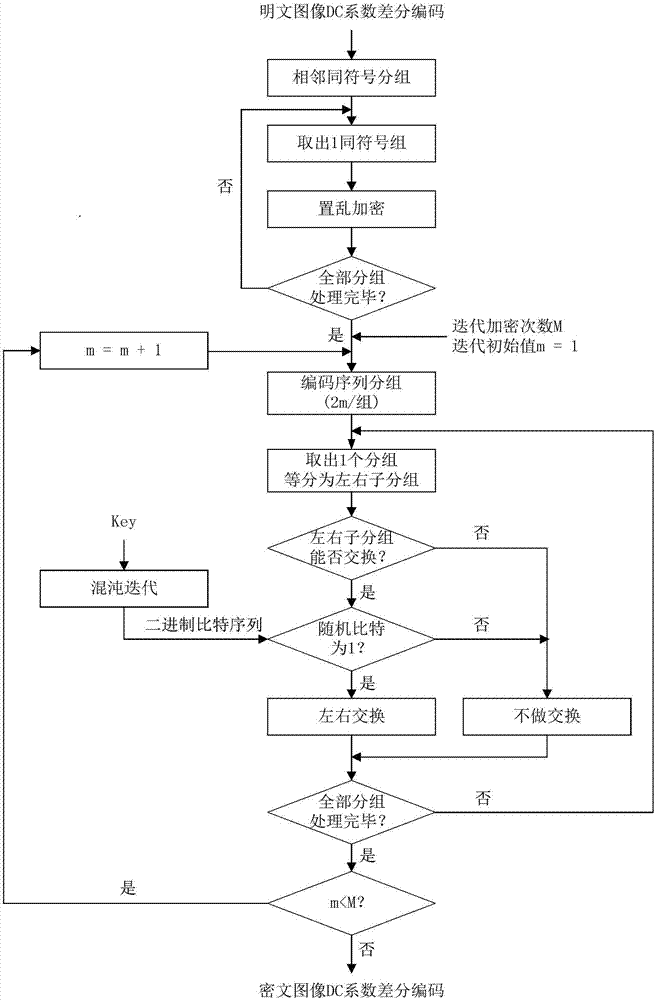
[0062] Step 2: According to the Huffman table, all DC coefficient differential codes and AC coefficient codes of each DCT block of the JPEG image are parsed from the DCT coefficient coded bit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More