Data security protection system and method based on Internet of Things
A data security and protection system technology, applied in the direction of digital data protection, based on specific mathematical models, digital data authentication, etc., can solve problems such as easy data loss, solve key management difficulties, realize timely analysis, and ensure safety and reliability Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
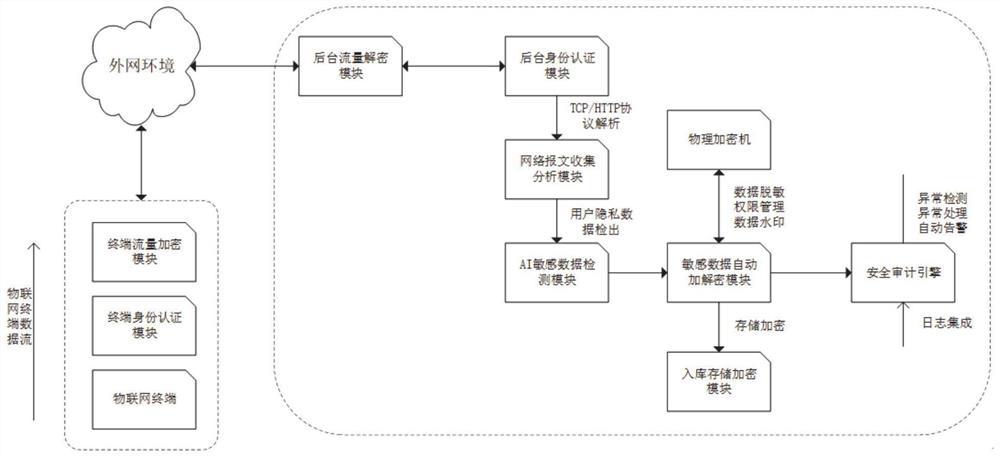
[0069] In one or more embodiments, a data security protection system based on the Internet of Things is disclosed, which utilizes multiple data security software and hardware modules, fully utilizes the AI detection model and the sensitive data rule model, and realizes more transparency in the Internet of Things scenario Sensitive data protection and data automatic desensitization achieve the effect of data security protection.
[0070] Specifically, refer to figure 1 , the data security protection system based on the Internet of Things includes:
[0071] (1) The IoT terminal identity authentication module is configured to register and authorize terminal equipment to obtain terminal digital certificates and equipment information;
[0072] (2) The terminal network traffic encryption module is configured to establish a TLS1.2 secure encrypted channel through key negotiation with the background system, and send the original protocol data traffic of the terminal on this secure ...
Embodiment 2
[0096] In one or more implementations, a data security protection method based on the Internet of Things is disclosed. The method is based on the system in Embodiment 1, and specifically includes the following process:
[0097] Step 1: The terminal device registers and authorizes, and obtains the terminal digital certificate and device information;
[0098] Step 2: The terminal negotiates keys with the background, exchanges keys, and creates a TLS1.2 secure channel;
[0099] Step 3: The terminal sends the original protocol data traffic in the secure channel, and brings in the terminal certificate and device information for authentication and authorization;
[0100]Step 4: The background traffic decryption module decrypts the traffic ciphertext when the traffic reaches the background system, obtains the original protocol data traffic, terminal certificate and device information, and verifies the identity legitimacy of the IoT terminal based on the digital certificate and termin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More