AES key arrangement method
A key and round key technology, applied in the field of information security, can solve the problems of inability to complete algorithm power consumption, efficiency and security performance, and achieve the effect of reducing correlation, increasing security, and increasing cryptographic characteristics
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, but not all of the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present invention.
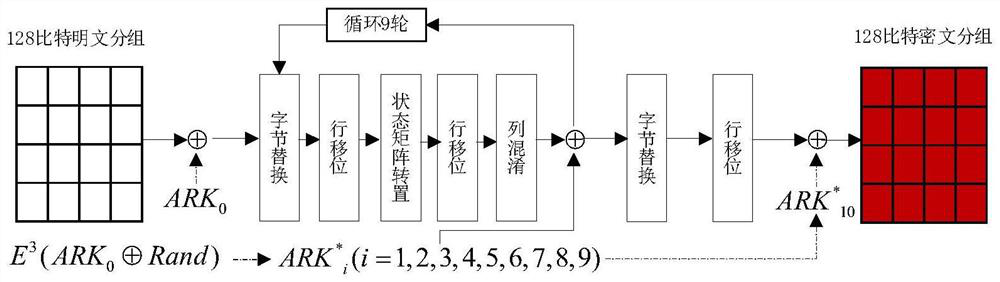
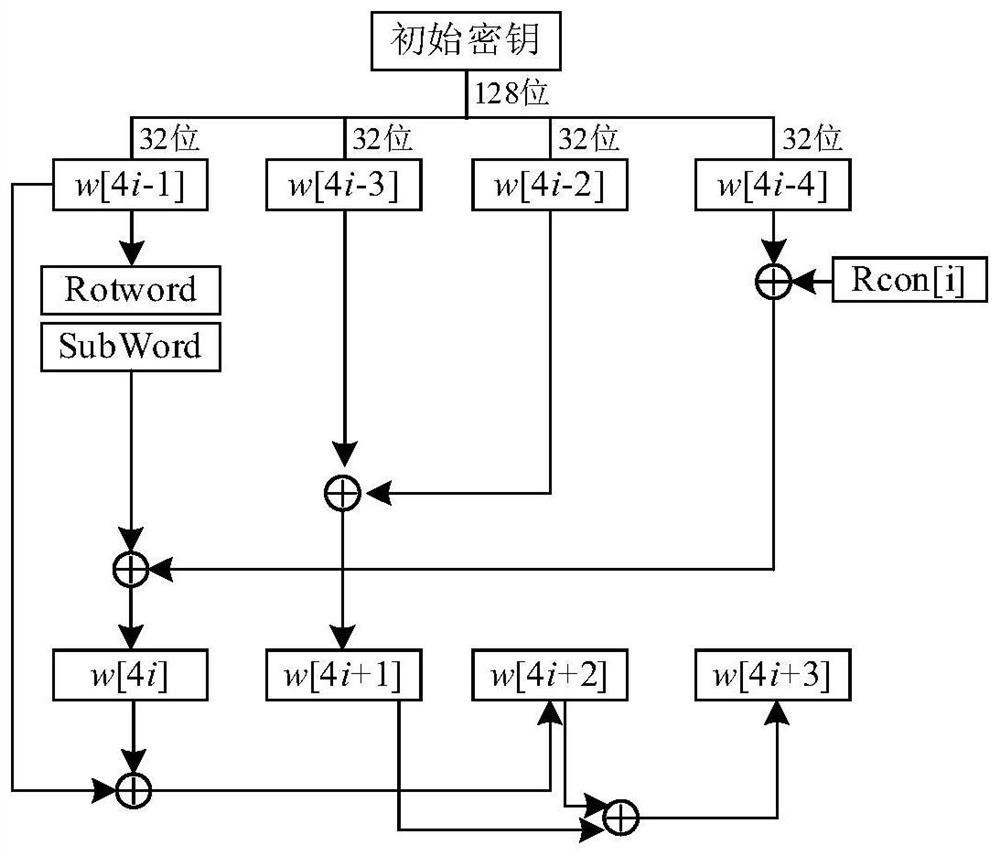
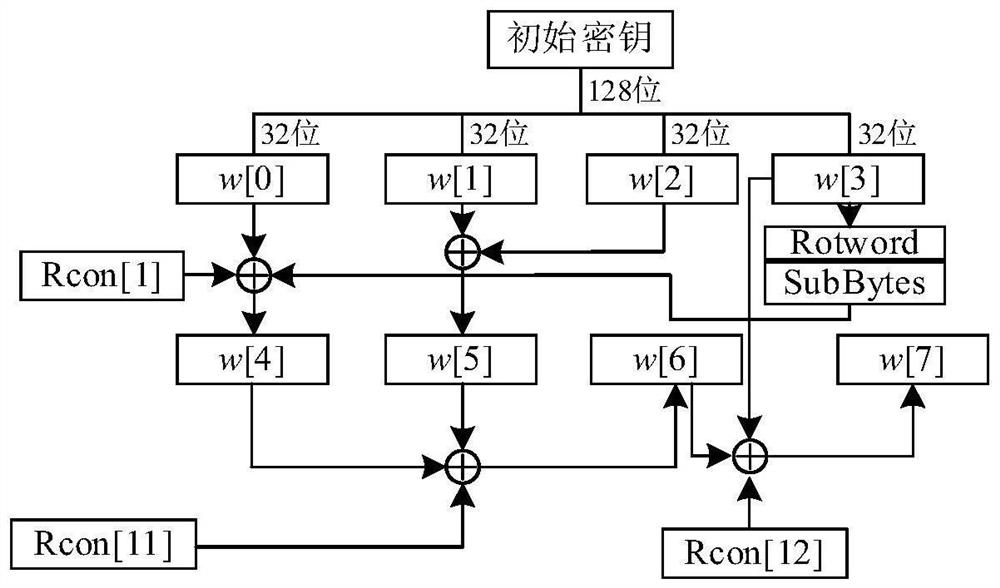
[0023] see figure 1 , an AES-128 key arrangement method, when using AES-128 encryption for sensitive data sets, using software or hardware to implement the present invention, and generating a random sequence Rand through a binary integer chaotic sequence generation module, the binary integer chaotic sequence The sequence generation module is connected with a round function module and a key expansion module, the round function module i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More