Storage abnormal detecting method based on artificial immunity
An anomaly detection and artificial immunization technology, which is applied in the fields of instruments, calculations, electrical digital data processing, etc., can solve problems such as inability to diagnose users, inability to achieve storage anomaly active defense capabilities, and failure to reach
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
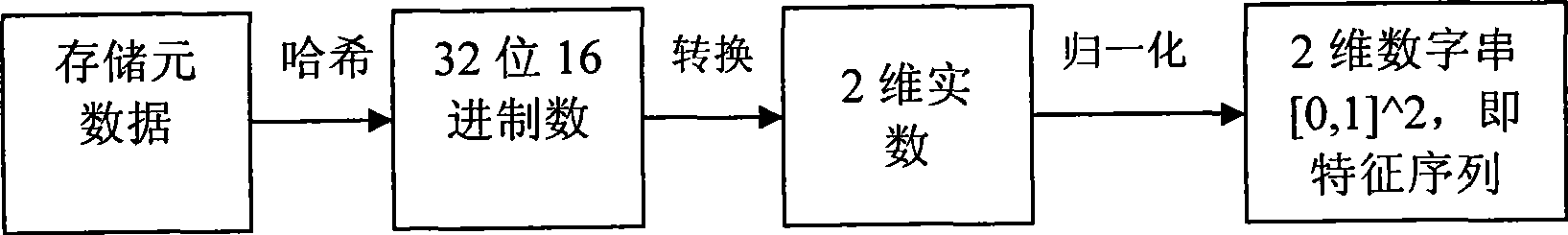
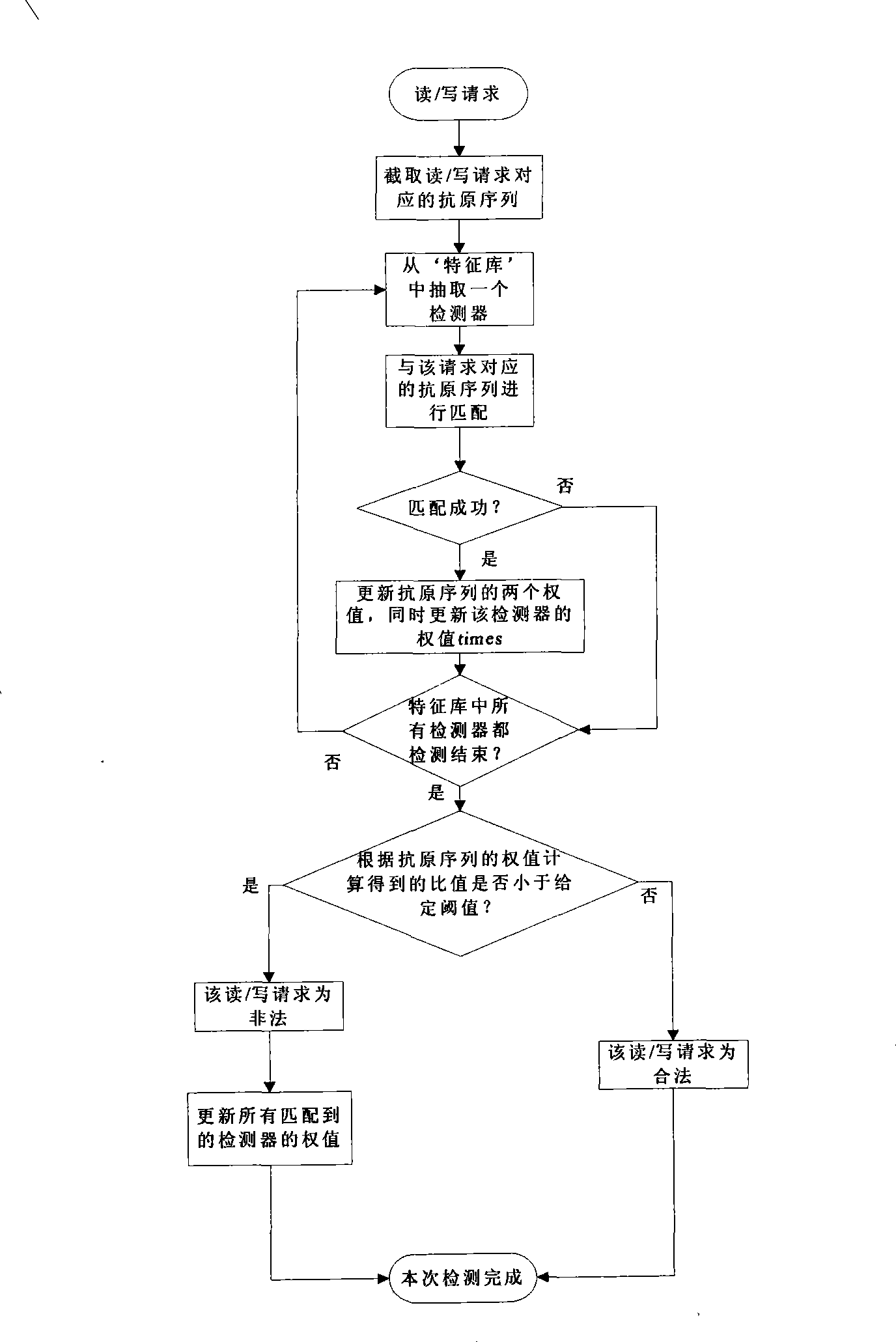
[0017] In large-scale storage systems, it is difficult to detect anomalies in all data because the data volume is usually huge. Metadata is the information describing other data, that is, the data of the data. We will identify abnormal read / write access requests by monitoring the relevant metadata of user access. This method can reduce the calculation and design complexity of the detection system . A metaphor for the immune principle of the biological immune system, drawing on the immune mechanism of generating antibodies and matching antigens in organisms, and finally identifying 'self' and 'others'. Below in conjunction with accompanying drawing and example the present invention is described in further detail.
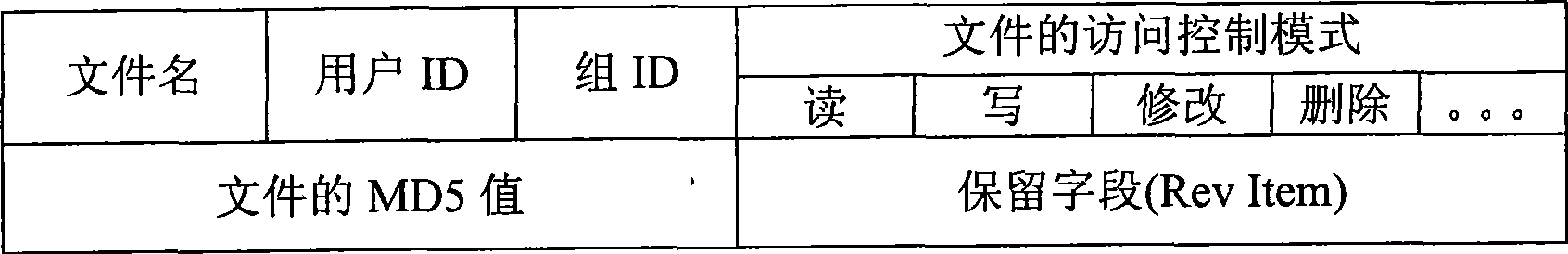
[0018] How to get storage metadata? The first is to intercept the system call of the access request, and then combine the access control mode and MD5 value of the requested file to form a figure 1 The storage metadata data structure shown includes file name, user ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More