Association analysis method and device for security logs
A correlation analysis and log technology, applied in the field of data processing, can solve problems such as business requirements that are no longer applicable, and achieve the effect of avoiding performance overhead, reducing pressure, and improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
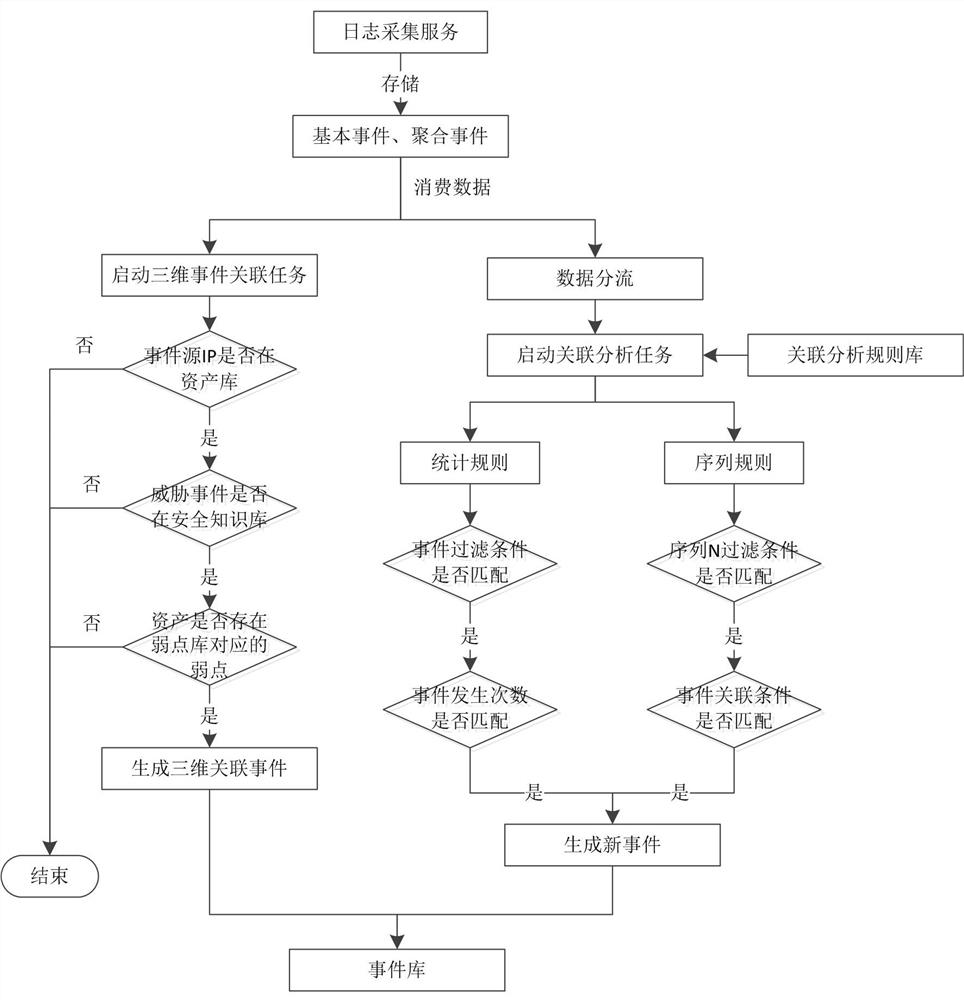
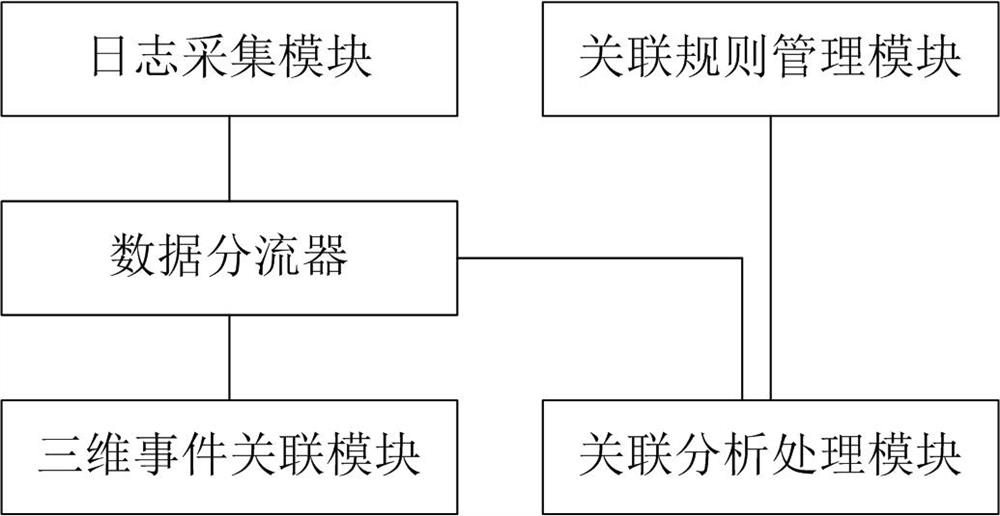
[0023] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be described clearly and completely below with reference to the accompanying drawings in the embodiments of the present invention.
[0024] For the convenience of understanding, the terms involved in the embodiments of the present invention are explained below:
[0025] The log audit system is a network security tool that uses big data collection, modeling, and analysis technology to detect threats and abnormal behaviors in the network in time through multi-dimensional information collection and automated correlation analysis of various network resources. Through the security linkage with firewall, intrusion prevention, terminal security and other products, it can effectively deal with threats and abnormal behaviors.
[0026] Raw events: Logs that have not yet been processed are col...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More