Sandbox construction method based on mimicry thought
A construction method and sandbox technology, applied in the field of network security, to achieve the effects of preventing breaches, ensuring correctness, increasing cognition and attack difficulty
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
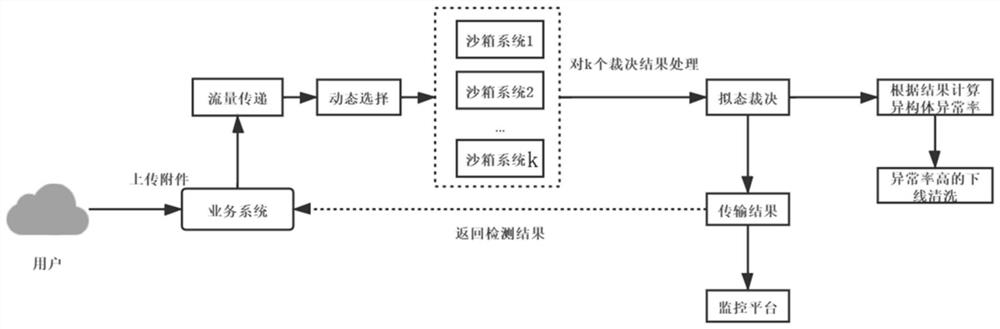
[0026] The invention designs a sandbox construction method based on the idea of mimic defense, which can actively defend against malicious attacks on the file system. The present invention designs a flow transfer module, a sandbox heterogeneous module, a mimicry judgment module, and a monitoring platform module, and realizes the construction of a mimicry sandbox by building a module for a sandbox isomer, and detects the operating system, simulation speed, and malware The sandbox is heterogeneously processed in terms of behavior and other aspects, so that the sandbox has active defense capabilities. When the traffic passes through the sandbox system module, the module will select k from all sandbox isomers for traffic processing. After the processing result is judged by the mimicry judgment module, the abnormal rate of each isomer is modified with the judgment result. When When the abnormal rate of a certain isomer is higher than a certain value, the isomer will be taken offl...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com