Service regulation and control network security and credibility auditing method and system suitable for 5G network
A business network and network technology, applied in information technology support systems, security devices, wireless communications, etc., can solve problems such as lack of credibility, signature invalidation, etc., to ensure privacy and security, and save power grid system resources.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
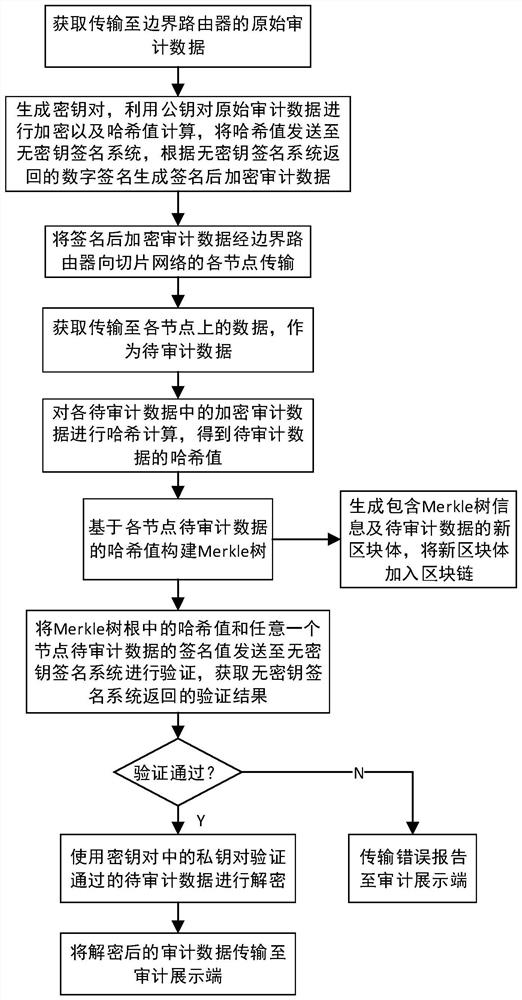
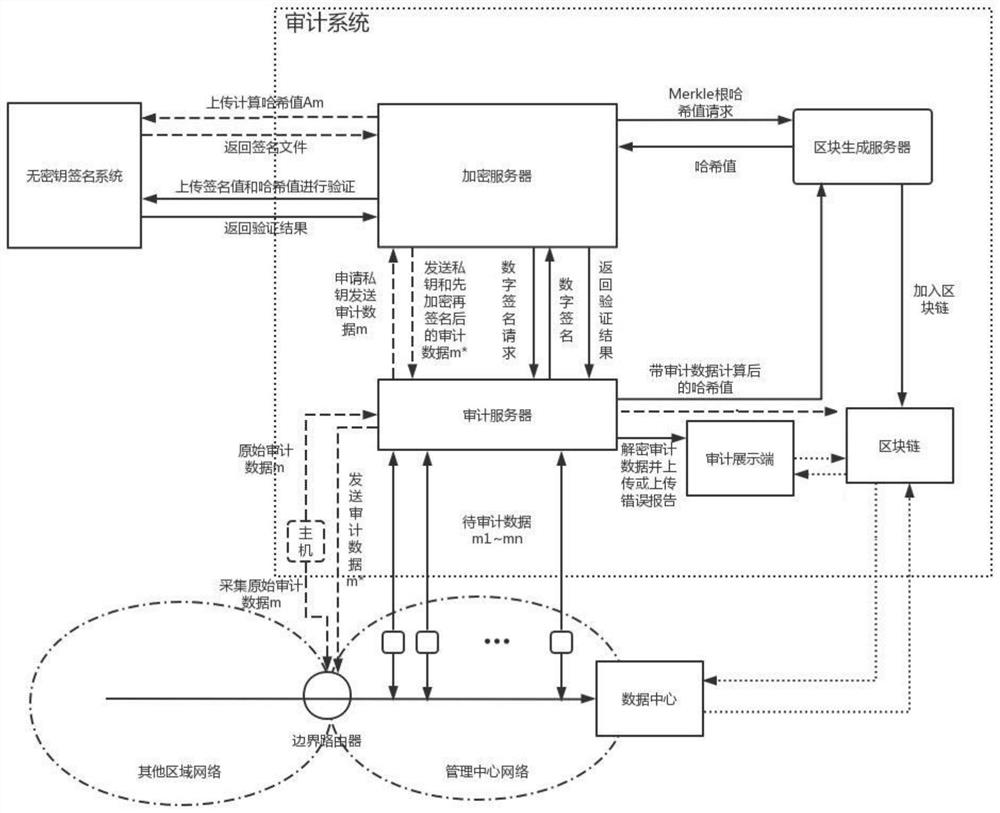
[0080] Based on the above inventive concept, this embodiment introduces a network security credible audit method for regulation and business services applicable to 5G networks, including:
[0081] Obtain original audit data, wherein the original audit data is audit data with the management center slice network as the target transmission direction;
[0082] Encrypt and sign the original audit data to generate signed encrypted audit data;
[0083] transmitting the signed and encrypted audit data to each node of the management center slicing network, and obtaining the data transmitted to each node as the data to be audited;
[0084] Hash calculation is performed on the encrypted audit data in the data to be audited of each node respectively, and the hash value corresponding to each data to be audited is obtained;
[0085] Build a Merkle tree based on the obtained hash value;
[0086] Obtain the hash value in the root of the Merkle tree and the signature value in the data to be ...
Embodiment 2
[0089] Based on the same inventive concept as Embodiment 1, this embodiment makes further improvements on the basis of the technical solution of Embodiment 1.
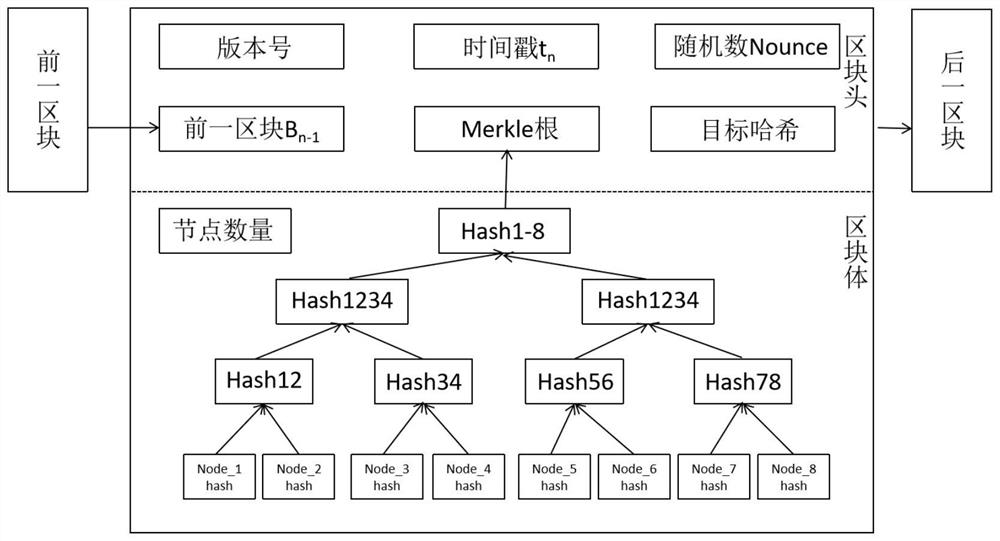
[0090] The method for trusted auditing network security of the regulation business applicable to the 5G network in this embodiment further includes: encapsulating the data to be audited obtained from each node and the Merkle tree information into a data block with a time stamp, and adding the data block to the area blockchain;
[0091] In the method, obtaining the hash value in the root of the Merkle tree and the signature value in the data to be audited on any node is: obtaining the hash value in the root of the Merkle tree and any one from the block body of the blockchain The signature value in the data to be audited on the node.
[0092] In the method, if the final verification fails, the audit error information is also stored in the corresponding block.
[0093] refer to figure 1 As shown, this embodiment specif...
Embodiment 3
[0118] With the inventive concept based on Embodiments 1 and 2, this embodiment introduces a network security credible auditing device for regulation business applicable to 5G networks, including:
[0119] an original audit data acquisition module, configured to acquire original audit data, wherein the original audit data is audit data with the management center slice network as the target transmission direction;
[0120] The encryption signature processing module is configured to encrypt and sign the original audit data to generate signed encrypted audit data;
[0121] a data acquisition module to be audited, configured to transmit the signed and encrypted audit data to each node of the management center slice network, and acquire the data transmitted to each node as the data to be audited;
[0122] The data to be audited data hash calculation module is configured to perform hash calculation on the encrypted audit data in the data to be audited of each node respectively, to o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More