Security apparatus for data transmission with dynamic random encryption
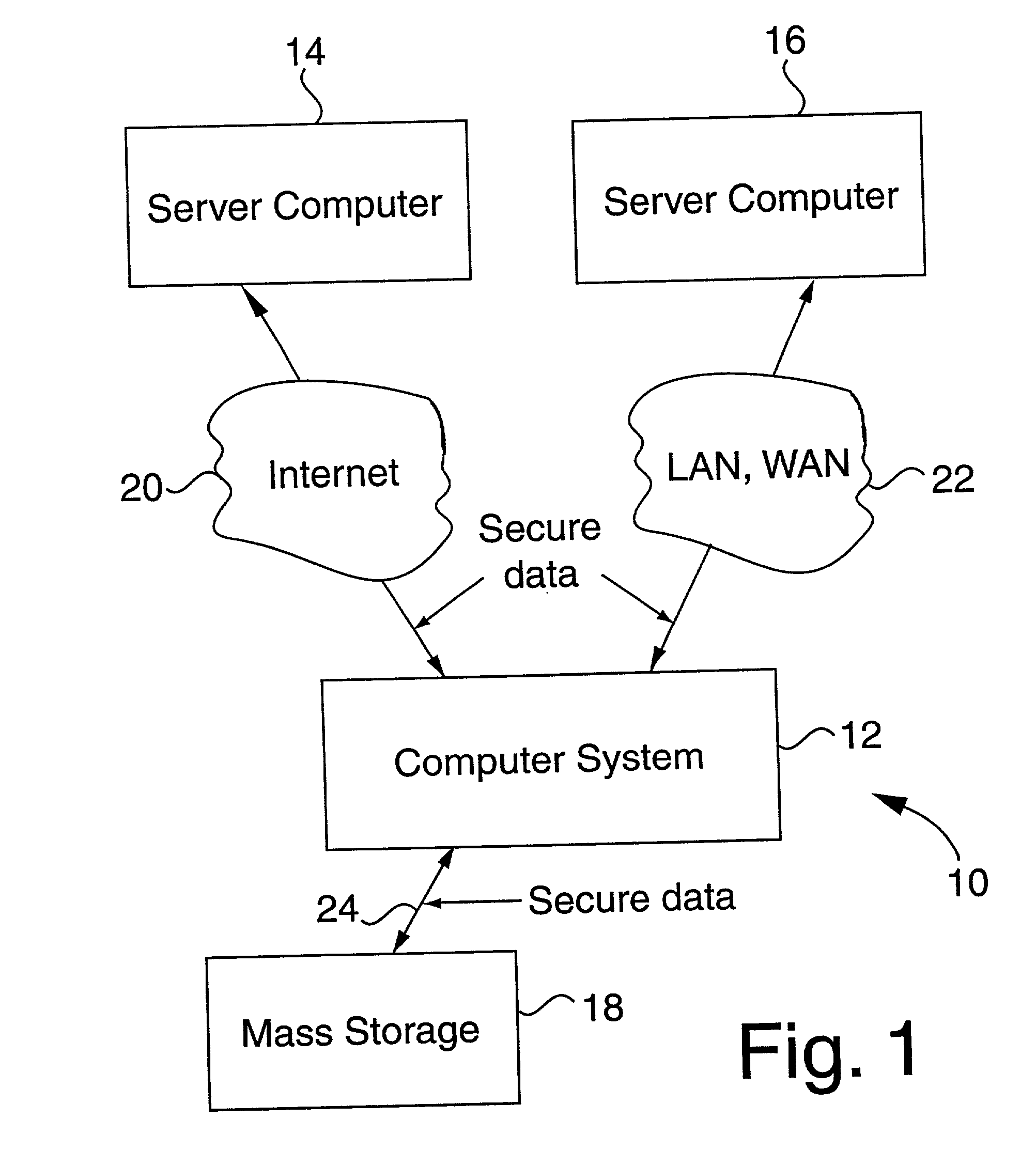
a technology of dynamic random encryption and security apparatus, which is applied in the field of data transmission, can solve the problem that the encryption schema stored in the memory of the external security unit cannot be read by anyone gaining unauthorized access to the computer itself, and achieves the effect of greater security and higher security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
embodiment 300
[0048] FIG. 5 illustrates a security unit 52 that communicates with computer 102. Security unit 52 includes a number input device 302 for inputting a number into either a PIN register 304 or public code register 306. The contents of these two registers are combined using merging logic 308 in order to produce an address which is stored in address register 312. Increment logic 310 is used to receive the contents of address register 312 and a relative address 314 from memory 316 in order to provide a new address for address register 312. Shift register 317 is used to transfer selected data from memory 316 through to computer 102.
[0049] Number input device 302 may be any suitable type of input device used for entering numbers, letters, and / or symbols into security unit 52. In one embodiment of the invention, simple number wheels 318 are used to enter a sequence of numbers. In the example shown, the number "4712" is being entered into the input device. The use of a rotary number wheel or...
embodiment 1200
[0096] FIG. 13 illustrates a flowchart 1300 of the embodiment 1200 operation. First, a key code is input to the controller 1210. The controller 1210 processes the key code and determines a first starting point and a length of control data. The first starting point is a first computed address within the array of random data 1220. The length of control data is defined as how many bytes of control data to retrieve from the array of random data 1220. The controller 1210 then accesses the array of random data 1220 at the first computed address determined by the key code, and retrieves the number of control bytes, from the array of random data 1220.
[0097] One skilled in the art will appreciate that the key code can include a plurality of key components or sub keys or codes such as a private code, a personal identification number (PIN) or a public code or combinations and multiples thereof. Such sub codes may be numeric, alphabetical, alpha-numeric, biometric, or graphical or any other for...
embodiment 1500
[0133] FIG. 15 illustrates another embodiment 1500 of the present invention. In this embodiment, the encryption / decryption system 1500 includes a first and second electronically readable media 1510, 1550 such as a magnetic media, optical media, magneto-optical media, CDROM, digital video disk (DVD), hard disk, or any other electronically readable media method. The first and second electronically readable media 1510, 1550 contains a random array. In an alternative embodiment, the first and second electronically readable media 1510, 1550 also include a plurality of encryption / decryption algorithms.
[0134] The encryptor 1530 includes the capability to read the first electronically readable media 1510 and to receive unencrypted data 1520. The encryptor 1530 reads the first electronically readable media 1510 and inputs the random array or a portion thereof and the encryption / decryption algorithm and then encrypts the unencrypted signal as described above to output an encrypted signal.
[013...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More