Security event automatic association and quick response system and method based on big data information
An information security and automatic association technology, applied in the field of information security, can solve the problems of low information synchronization efficiency, easy to be cracked, and low security, and achieve the effects of improving information synchronization efficiency, realizing real-time identification, and saving storage space
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
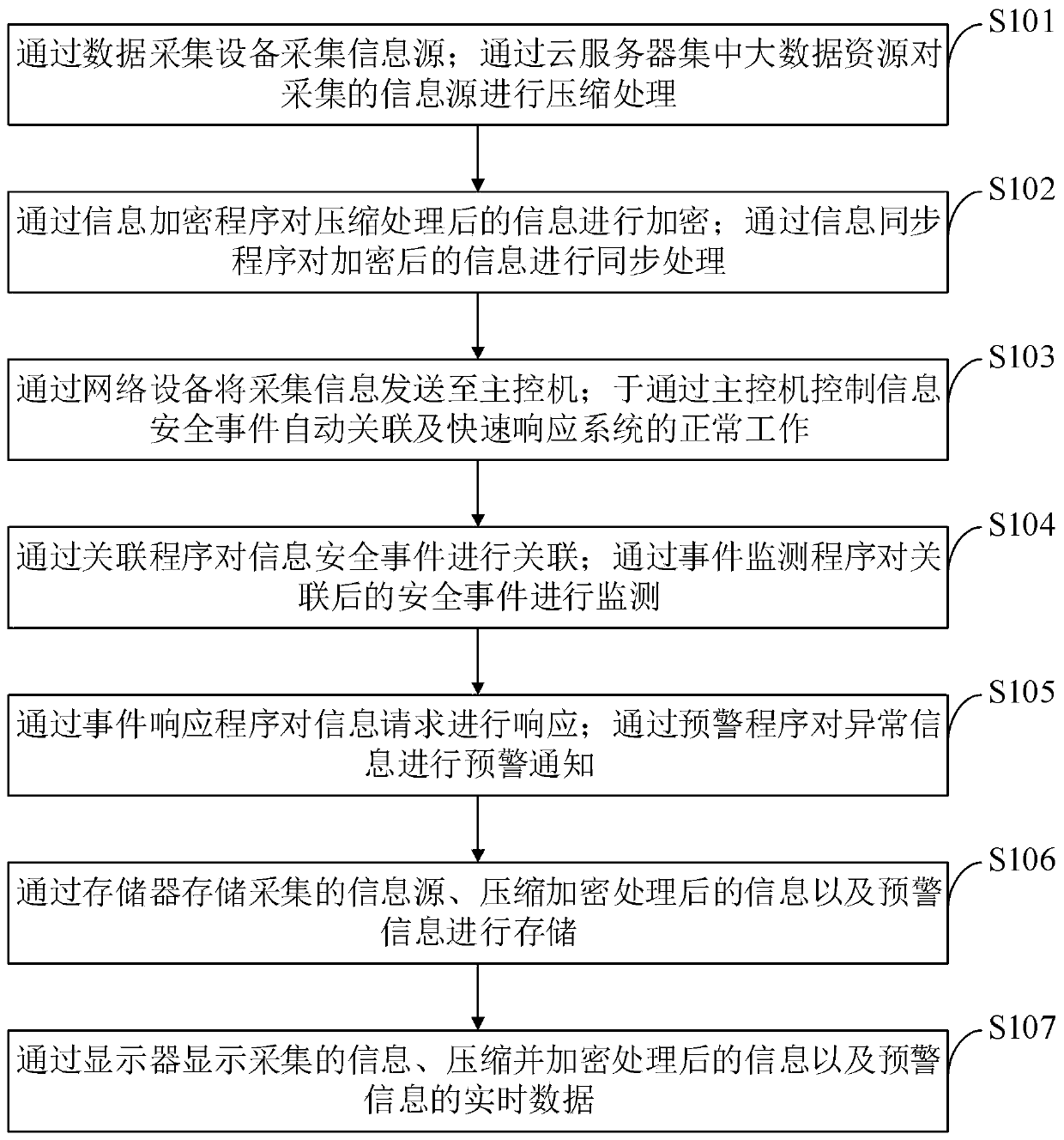
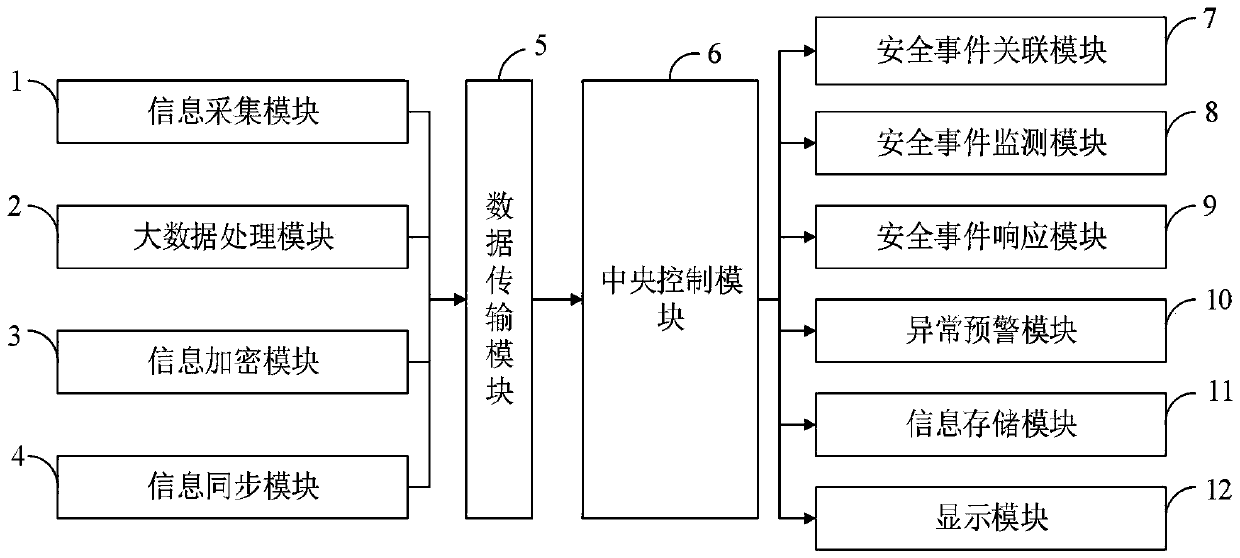
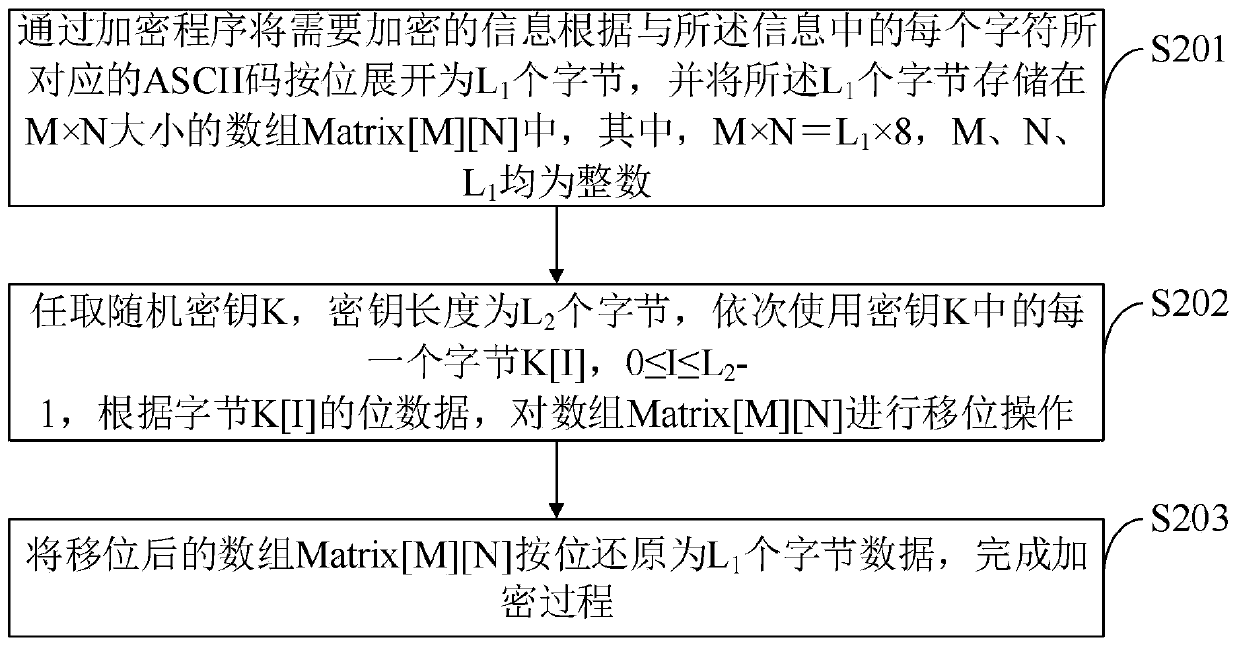
[0083] The automatic correlation and rapid response method based on big data information security events provided by the embodiment of the present invention is as follows: figure 1 As shown, as a preferred embodiment, such as image 3 As shown, the method for encrypting the collected information through the information encryption program provided by the embodiment of the present invention includes:
[0084] S201, expand the information to be encrypted into L bit by bit according to the ASCII code corresponding to each character in the information through the encryption program 1 bytes, and the L 1 bytes are stored in an array Matrix[M][N] of M×N size, where M×N=L 1 ×8, M, N, L 1 are integers.
[0085] S202, randomly select a random key K, and the key length is L 2 bytes, use each byte K[I] in the key K in turn, 0≤I≤L 2 -1, according to the bit data of byte K[I], the array Matrix[M][N] is shifted.
[0086] S203, restore the shifted array Matrix[M][N] to L bit by bit 1 b...
Embodiment 2
[0093] The automatic correlation and rapid response method based on big data information security events provided by the embodiment of the present invention is as follows: figure 1 shown, as Figure 4 As shown, as a preferred embodiment, the method for synchronizing encrypted information through an information synchronization program provided by the embodiment of the present invention includes:
[0094] S301. Configure an information editing server. The first terminal receives first information and sends it to the information editing server, where the first information is background entry information of the first terminal.
[0095] S302. The information editing server converts the first information into a first character string and sends it to the middleware server, and the middleware server sends the first character string to the information management server.
[0096] S303. The information management server presets a naming rule, and generates a storage directory and a file...
Embodiment 3
[0106] The automatic correlation and rapid response method based on big data information security events provided by the embodiment of the present invention is as follows: figure 1 shown, as Figure 5 As shown, as a preferred embodiment, the method for associating information security events through the association program provided by the embodiment of the present invention includes:
[0107] S401. Receive an original security event, where the original security event includes an attribute value.
[0108] S402. Perform a hash operation on the original security event according to the attribute value of the original security event, and obtain a hash value.
[0109] S403. Classify the attribute values from the root node to obtain an attribute tree; find a first value equal to the hash value on different attribute trees, and obtain a rule tree corresponding to the first value.
[0110] S404. Traverse the rule tree, and if the first event is matched from the root node of the rul...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com