[0002] In recent years, with the rapid development of information technologies such as
the Internet of Things,
cloud computing, and
mobile Internet,
information networks have developed toward the characteristics of internationalization, socialization, openness, centralization, mobility, and
personalization, bringing convenience, While efficient and
information sharing, it also brings many new problems and challenges to
information security. Unauthorized and unauthorized use of software and hardware resources leads to the leakage of sensitive information and the spread of malicious information, endangering the interests of society, the country, groups and individuals ;At present, the domestic and foreign information security markets are mainly concentrated on firewalls, intrusion detection,
vulnerability scanning and other anti-foreign products.
Network security is mainly based on single-point protection. A large number of security products are simply piled up, which cannot form a large-scale and systematic three-dimensional protection.
System; at the current stage of network information security development, the scale of the network continues to expand, network equipment and nodes continue to increase, and at the same time
network security incidents emerge in endlessly, which are becoming more and more serious. Only relying on a single
network security product in the past is no longer able to guarantee the
safe operation of network information. ; The industry pays too much attention to preventing information security incidents from outside, lacks effective solutions to insider threats, and lacks technical research and product development of security audit monitoring systems for insider threats; according to statistics, 80% of
attack events, stolen secrets Incidents come from inside, and insiders are more likely to have access to confidential, important, and sensitive information. There are more security problems from inside, and it is more difficult to prevent them. Once internal security problems occur, the loss will be greater; the comprehensive audit and monitoring system of information security is the current and even The focus of the future information
security industry is a vital link in the construction of
informatization and the key to ensuring the healthy, stable and
sustainable development of
informatization;
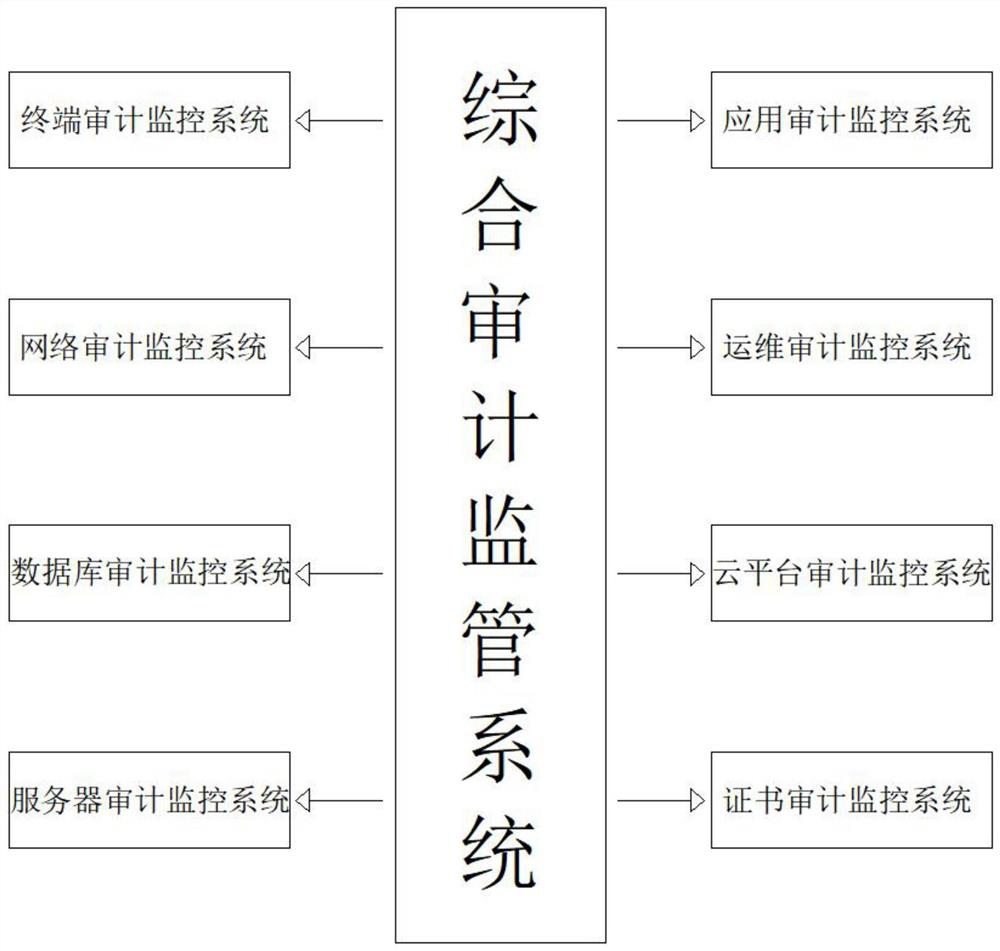
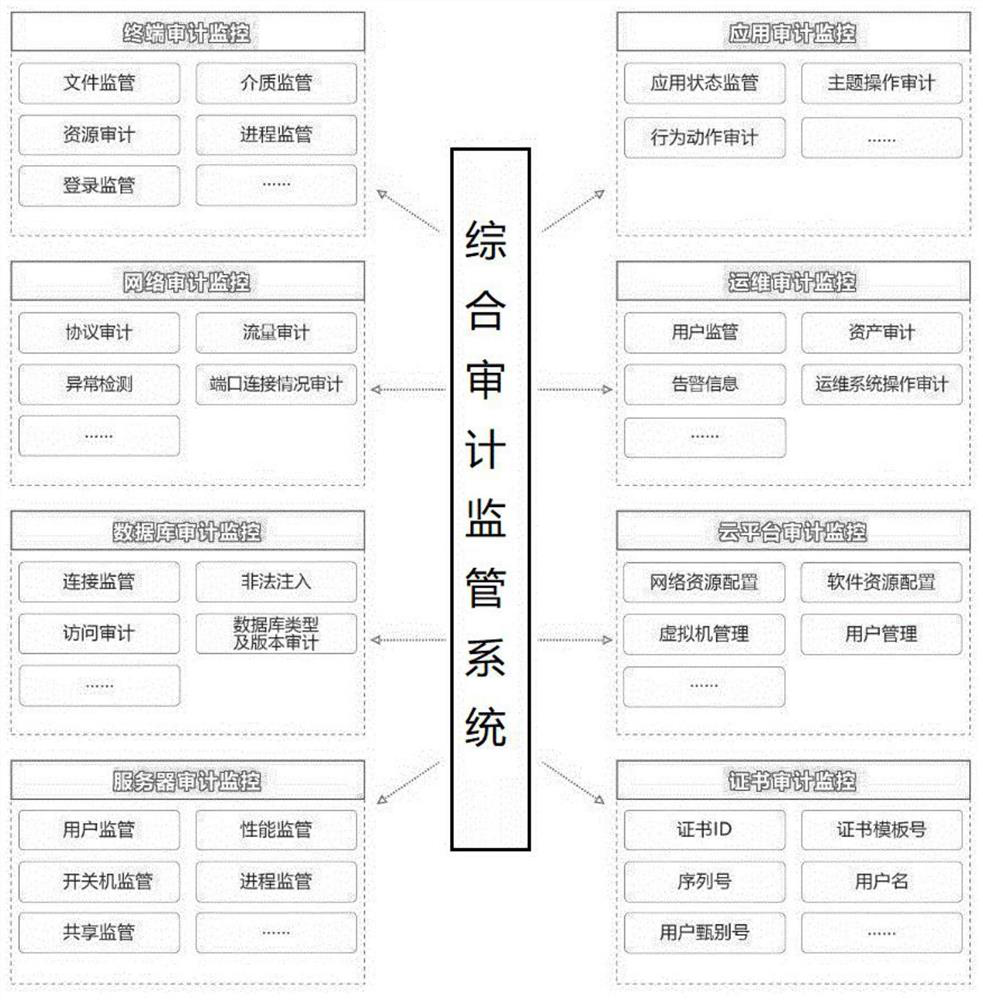
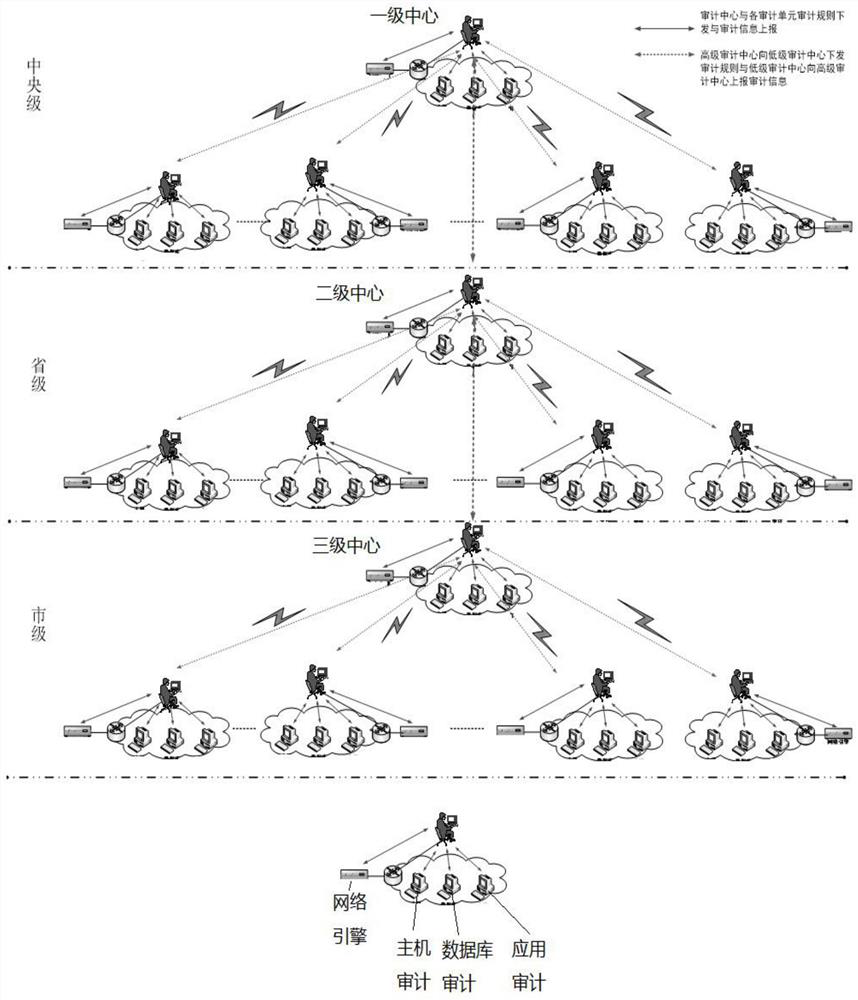
[0003] In today's information systems, various audit systems have been initially applied, such as: database audit and network
information audit, etc. However, with the continuous expansion of the network scale, audit products with a single function have certain limitations, and The ability to comprehensively analyze and comprehensively manage audit information is far from enough; complete functions, unified management, cross-regional, cross-
network segment, and
centralized management are the ultimate development goals of the security audit system; the domestic general understanding of computer information security is to ensure
Confidentiality, integrity,
usability,
controllability and non-repudiation (non-repudiation) of information in computer information systems, referred to as "five properties"; security audit is one of the important guarantees of these "five properties", it All network resources in the system (including databases, hosts, operating systems, security devices, etc.) conduct security audits,
record all events that occur, and provide them to system administrators as a basis for
system maintenance and security precautions. Security audits are like
bank monitoring systems , no matter who enters or leaves the
bank, it is registered truthfully, and everyone's actions in the
bank, even the movement of a teacup, are recorded truthfully. Once there is an emergency, you can quickly check the entry and exit records and behavior records to determine the problem location, in order to take corresponding measures; in recent years, with the development of e-government, the scale of
information system has continued to expand, and the equipment used in the system has gradually increased. Each equipment has its own audit module. In addition, there are special The audit system designed for a certain kind of
network application cannot achieve comprehensive security audit of the computer
information system, which results in a low safety factor. In addition, the existing audit system cannot monitor and review the operation behavior of internal personnel, and the user All processes using the
computer network system cannot be accurately tracked and are not comprehensive enough. Therefore, the present invention proposes a comprehensive audit supervision system to solve the problems existing in the prior art
 Login to View More
Login to View More  Login to View More
Login to View More